In the world of cybersecurity, there is a dangerous myth: the "Silver Bullet." Many organizations believe that if they just buy the most expensive firewall or the latest AI-driven antivirus, they are safe.
But in a landscape where attackers only need to be right once while defenders must be right every single time, relying on a single line of defense is a recipe for disaster. This is where Defense in Depth (DiD) comes in — not just as a buzzword, but as the bedrock of modern digital survival.
Introduction to Defense in Depth
At its core, Defense in Depth is a strategic approach to cybersecurity that implements multiple layers of security controls throughout an information technology system. Its purpose is to provide redundancy: if one control fails, others are in place to block the progression of an attack.
Think of it as a bank vault. To get to the money, a thief doesn't just have to pick a lock. They have to bypass the perimeter fence, avoid the security guards, disable the cameras, crack the biometric scanner, and then deal with the reinforced steel door.
Historical Context
The concept didn't start with computers. It is a transformation of the military strategy known as Elastic Defense. Historically, ancient fortresses used moats, high walls, and inner keeps. If the enemy crossed the moat, the wall stopped them. If the wall fell, the inner keep provided a final stand.
In the 1990s, the National Security Agency (NSA) adapted this philosophy for the digital age. As networks became more complex and "flat" perimeters disappeared, the industry realized that we must assume a state of "Assume Breach" — operating under the premise that an attacker will eventually get through one layer.
Layered Security Explained
To build a robust DiD strategy, we categorize defenses into three primary types of controls:
1. Physical Controls
These protect the actual hardware.
- Examples: CCTV cameras, biometric locks on data centers, security guards, and even "mantraps" that prevent tailgating into sensitive areas.
2. Technical (Logical) Controls
These are the hardware and software protections that safeguard data and networks.
- Examples: Firewalls, Multi-Factor Authentication (MFA), Encryption, Intrusion Detection Systems (IDS), and Endpoint Detection and Response (EDR).
3. Administrative (Policy) Controls
Often overlooked, these are the "human" layers. They ensure the technology is used correctly.
- Examples: Information security policies, Incident Response plans, and Security Awareness Training to prevent social engineering.
Implementation in Technology Companies
For a modern tech company, Defense in Depth must be integrated into every stage of the lifecycle:
- Network Security: Segmenting the network so that a breach in the "Marketing" VLAN doesn't allow an attacker to jump into the "Production" database.
- Application Security: Implementing "Secure by Design" principles, such as input validation and regular code audits (SAST/DAST).
- Endpoint Security: Protecting the laptops and mobile devices of employees who are often working remotely.
- Data Security: The "Crown Jewels." Even if an attacker steals a database, encryption at rest ensures they cannot read the contents.
- The Human Element: Phishing simulations and a culture of security where employees feel empowered to report suspicious activity.
Conclusion: The Resilience Mindset
Defense in Depth isn't about being "unhackable" — it's about being resilient. By creating a series of hurdles, you slow an attacker down, increase the cost of their attack, and significantly raise the chances of detecting them before they reach their objective.
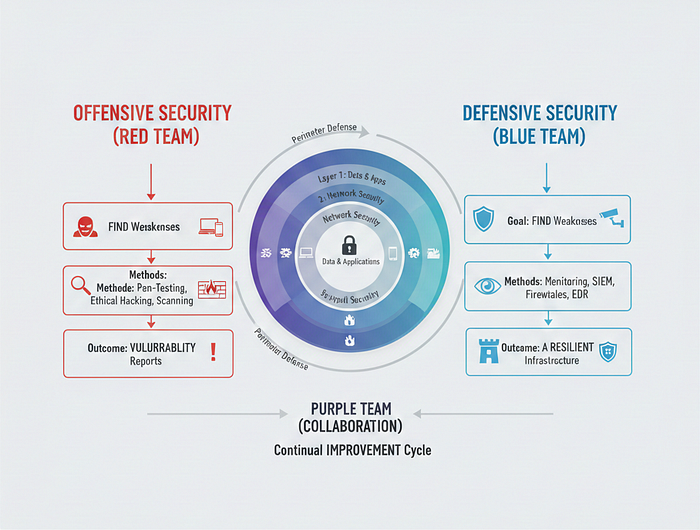
In our next entry, we will move from the strategy of defense to the teams that execute it. We'll be diving into the high-stakes world of Red Teams vs. Blue Teams to see how offensive and defensive security experts square off to make systems stronger.
