Difficulty : Medium
Note : All of the content and images are from https://tryhackme.com/room/
Room : https://tryhackme.com/room/cooctusadventures
Enjoy.
Task 1 The story so far…
Previously on Cooctus Tracker Overpass has been hacked! The SOC team (Paradox, congratulations on the promotion) noticed suspicious activity on a late night shift while looking at shibes, and managed to capture packets as the attack happened. (From Overpass 2 — Hacked by NinjaJc01)
Present times Further investigation revealed that the hack was made possible by the help of an insider threat. Paradox helped the Cooctus Clan hack overpass in exchange for the secret shiba stash. Now, we have discovered a private server deep down under the boiling hot sands of the Saharan Desert. We suspect it is operated by the Clan and it's your objective to uncover their plans.
Note: A stable shell is recommended, so try and SSH into users when possible.
Nmap Port Scanning :
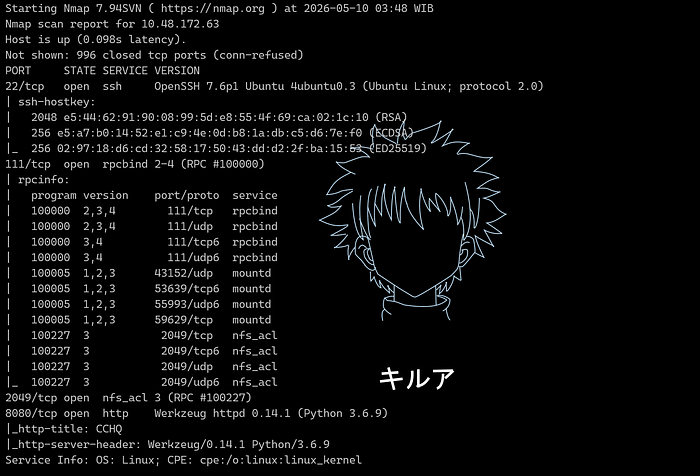
Nmap scan report for 10.48.172.63
Host is up (0.098s latency).
Not shown: 996 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 e5:44:62:91:90:08:99:5d:e8:55:4f:69:ca:02:1c:10 (RSA)
| 256 e5:a7:b0:14:52:e1:c9:4e:0d:b8:1a:db:c5:d6:7e:f0 (ECDSA)
|_ 256 02:97:18:d6:cd:32:58:17:50:43:dd:d2:2f:ba:15:53 (ED25519)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100005 1,2,3 43152/udp mountd
| 100005 1,2,3 53639/tcp6 mountd
| 100005 1,2,3 55993/udp6 mountd
| 100005 1,2,3 59629/tcp mountd
| 100227 3 2049/tcp nfs_acl
| 100227 3 2049/tcp6 nfs_acl
| 100227 3 2049/udp nfs_acl
|_ 100227 3 2049/udp6 nfs_acl
2049/tcp open nfs_acl 3 (RPC #100227)
8080/tcp open http Werkzeug httpd 0.14.1 (Python 3.6.9)
|_http-title: CCHQ
|_http-server-header: Werkzeug/0.14.1 Python/3.6.9
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 25.18 secondsNFS Credentiasl paradoxial.test:ShibaPretzel79
Answer the questions below
Q1.) Paradox is nomming cookies
paradox@cchq:~$ cat user.txt
cat user.txt
THM{2dccd1ab3e03990aea77359831c85ca2}Answer : THM{2dccd1ab3e03990aea77359831c85ca2}
Q2.) Find out what Szymex is working on
szymex@cchq:~$ cat user.txt
THM{c89f9f4ef264e22001f9a9c3d72992ef}Answer : THM{c89f9f4ef264e22001f9a9c3d72992ef}
Q3.) Find out what Tux is working on
tux@cchq:~$ cat user.txt
THM{592d07d6c2b7b3b3e7dc36ea2edbd6f1}Answer : THM{592d07d6c2b7b3b3e7dc36ea2edbd6f1}
Q4.) Find out what Varg is working on
varg@cchq:~$ cat user.txt
THM{3a33063a4a8a5805d17aa411a53286e6}Answer : THM{3a33063a4a8a5805d17aa411a53286e6}
Q5.) Get full root privileges
root@cchq:~# cat /root/root.txt
THM{H4CK3D_BY_C00CTUS_CL4N}Answer : THM{H4CK3D_BY_C00CTUS_CL4N}

Thanks for reading my blog sir ;)
Lawvye