Vulnerability Details
Insecure logging occurs when a mobile application writes sensitive information into logs (e.g., Logcat, local files, crash reports, or analytics events).
These logs may be accessible by:
- Other applications (on rooted/debuggable devices)
- Attackers with physical access
- Developers via debugging tools
As a result, sensitive data exposure may occur.
Vulnerable Code Example:
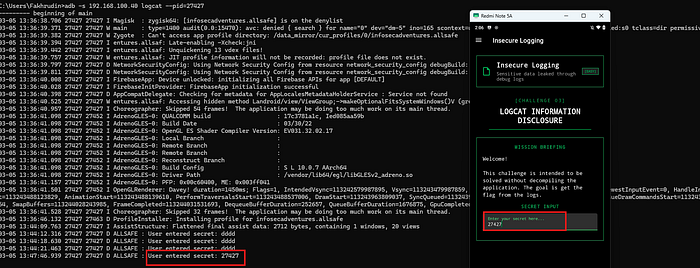
Log.d("ALLSAFE", "User entered secret: " + secret.getText().toString());How to Identify Insecure Logging?
- Enable USB debugging on the Android device or Emulator
- Obtain the Process Identifier (PID) of the target application:

adb shell pidof <package_name>3. Monitor logs for the specific process:
adb shell logcat --pid=<PID>4. Interact with the application and observe whether sensitive data (e.g., passwords, tokens) appears in the logs
Impact
Insecure logging may lead to:
- Credential leakage (passwords, tokens, API keys)
- Exposure of personal data (name, email, national ID)
- Financial data leakage (credit card information)
- Disclosure of internal application logic
Mitigation
- Never log sensitive data (passwords, tokens, PII)
- Disable debug logs in production builds
- Use logging levels appropriately (INFO, WARN, ERROR)
- Implement secure logging practices and data masking
Secure Code Example
static /* synthetic */ boolean lambda$onCreateView$0(TextInputEditText secret, TextView v, int actionId, KeyEvent event) {
if (actionId == 6 && !TextUtils.isEmpty(secret.getText())) {
if (BuildConfig.DEBUG) {
Log.d("ALLSAFE", "User input triggered"); // No sensitive data logged
}
return false;
}
return false;
}Conclusion
Insecure logging is a common yet critical vulnerability in mobile applications that can lead to unintended exposure of sensitive information. Even though logging is essential for debugging and monitoring, improper handling of logs — especially in production environments — can significantly increase the attack surface.
Developers must ensure that no sensitive data is written to logs and that debugging features are disabled in release builds. Implementing secure logging practices is crucial to protect user data and maintain application security.

