The goal of this challenge is to perform a DOM-based Cross-Site Scripting (XSS) attack by injecting malicious JavaScript into a dynamic part of the application.
Challenge Overview
Title: DOM XSS Category: Cross-Site Scripting (XSS) Difficulty: ⭐ (1/6)
Tools Used
- Web browser
Methodology
The approach focuses on identifying an injection point in the application and testing how user input affects the DOM.
1. Identify the Injection Point
The search functionality is a possible vector for XSS attacks because the q parameter in the URL updates content dynamically in the application.
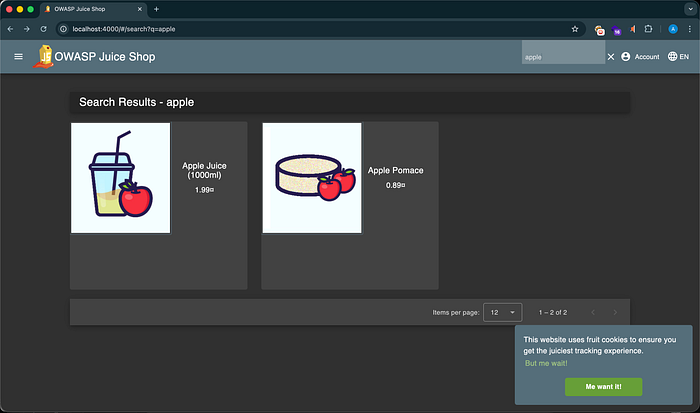
2. Test Normal Input
Test with a normal search string such as apple to verify the functionality of the search feature.
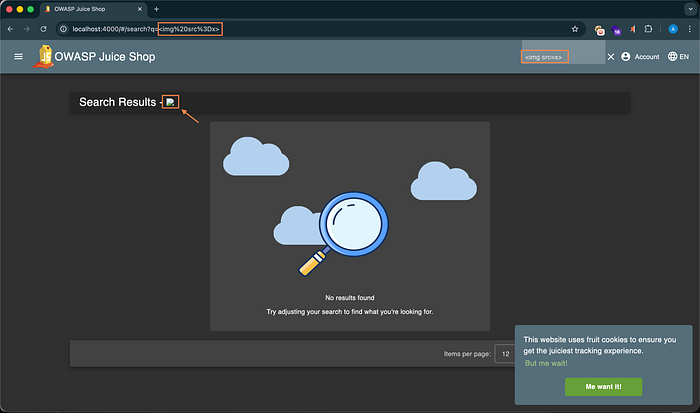
3. Attempt to inject HTML using the payload:
<img src=x>The broken image icon appears on the page, which indicates that HTML is being rendered in the DOM and confirms successful HTML injection.
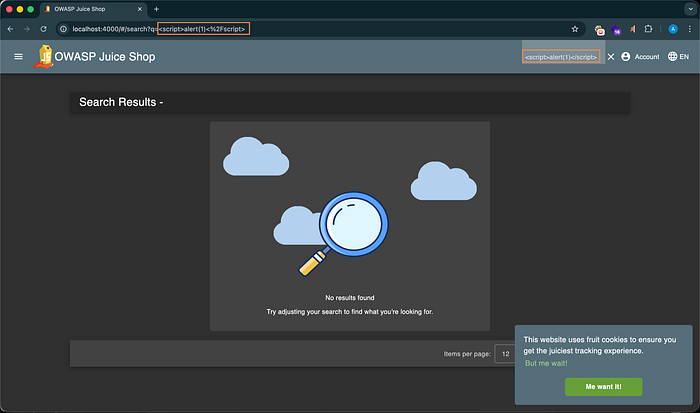
4. Attempt to inject a script payload using:
<script>alert(1)</script>No alert appears, which indicates that script tags are being filtered or sanitized by the application.
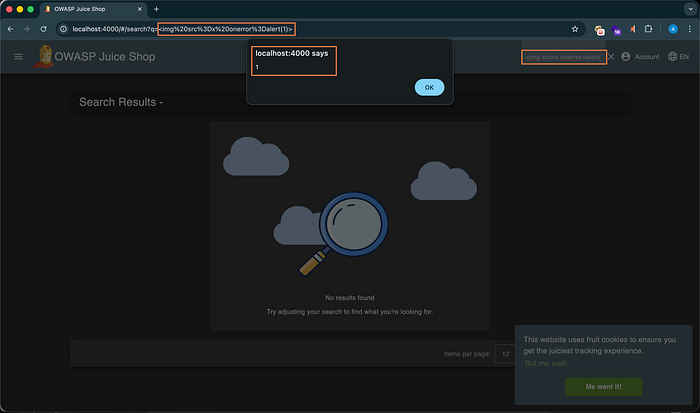
5. Attempt to inject an HTML tag with an event handler using:
<img src=x onerror=alert(1)>The alert executes when the image fails to load, confirming that event handlers are not properly sanitized and JavaScript execution is possible.
6. Inject the required payload:
<iframe src="javascript:alert(`xss`)">Navigating to the manipulated URL executes the JavaScript from the iframe source attribute and triggers the alert, completing the challenge.
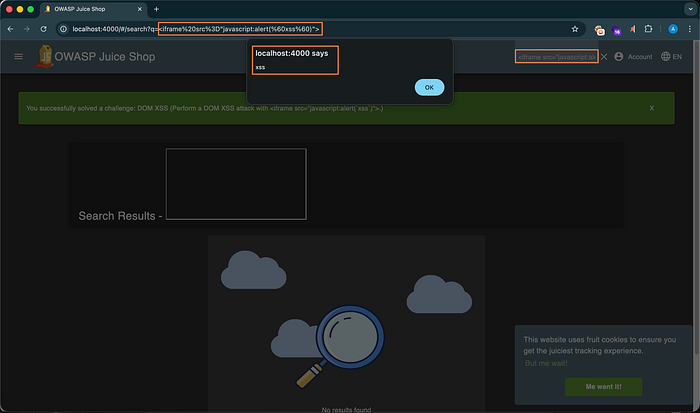
Solution Explained
The vulnerability exists due to client-side routing and unsafe DOM manipulation.
The application uses hash-based routing, visible in the URL structure:
/#/search?q=payloadEverything after the # is handled by the browser and processed by JavaScript rather than being sent to the server. The application reads this value from location.hash and injects it directly into the DOM.
Because the input is inserted into a dangerous sink without proper sanitization, the iframe payload executes JavaScript directly in the browser. This results in a DOM-based XSS vulnerability, where the attack occurs entirely on the client side without server involvement.
This demonstrates how improper handling of URL fragments and unsafe DOM rendering can lead to script execution.
Remediation
To prevent DOM XSS vulnerabilities, the following should be implemented:
- Use frameworks with built-in XSS protection and ensure their security features are properly configured.
- Sanitize and validate all user inputs before inserting them into the DOM.
- Avoid dangerous sinks such as
innerHTML,eval, and direct DOM injection of user-controlled data. - Implement a strong Content Security Policy (CSP) to restrict executable scripts and reduce the impact of potential XSS attacks.
- Ensure client-side routing does not expose unsanitized input directly to the DOM.

