Containers are often considered secure due to isolation, but in reality, misconfigurations and weak practices can completely break that isolation.
If you're a security professional, pentester, or DevOps engineer, understanding Docker vulnerabilities is critical to preventing real-world attacks.
🚨 Why Docker Security Matters
Docker shares the host OS kernel, which means:
- A single misconfiguration can expose the entire host
- Attackers can escalate privileges from container → host
- Sensitive data can be leaked through poor design
👉 In short: containers are not VMs — isolation is weaker
🧱 1. Image-Based Vulnerabilities
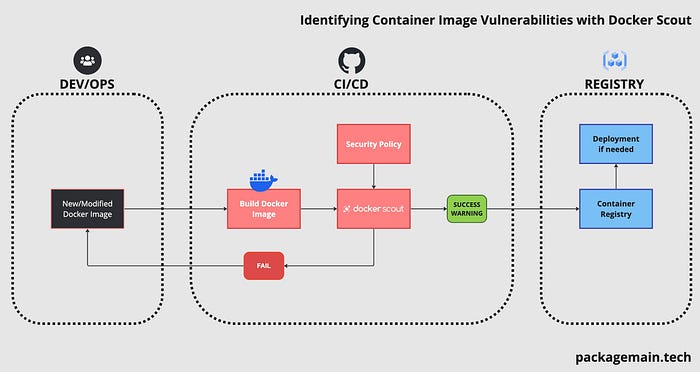

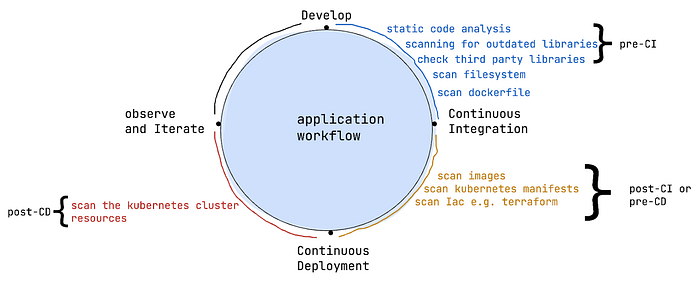
Docker images are the foundation of containers. If the image itself is vulnerable, everything built on top of it is compromised.
🔴 Common Issues:
- Outdated software packages (CVEs)
- Hardcoded credentials inside layers
- Using untrusted public images
- Malicious backdoors
🛠️ Example:
trivy image vulnerables/web-dvwa👉 Scans image for known vulnerabilities
⚙️ 2. Container Misconfiguration

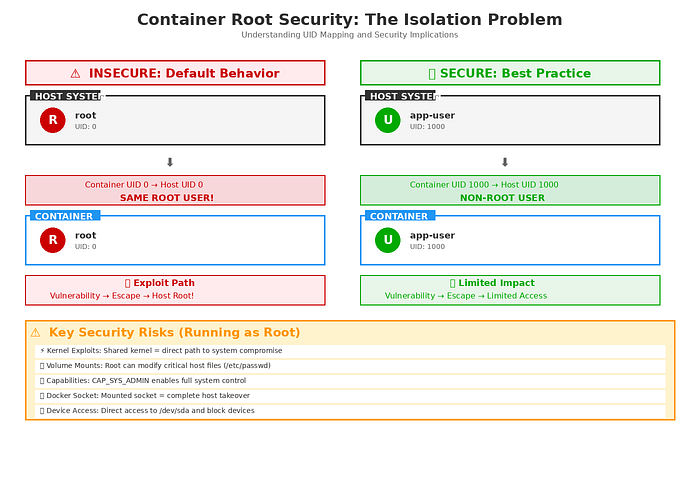
Even secure images become dangerous when run with insecure settings.
🔴 Common Issues:
- Running containers with
--privileged - Containers running as root user
- Excessive Linux capabilities
- No security restrictions
⚠️ Risk:
👉 Attackers can gain elevated access and escape the container
📂 3. Volume & File System Exposure
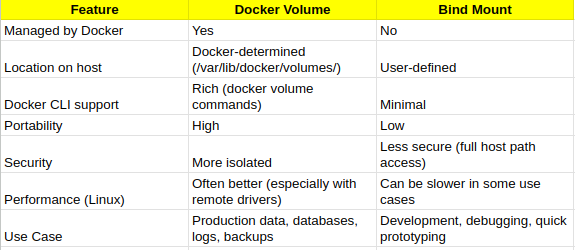
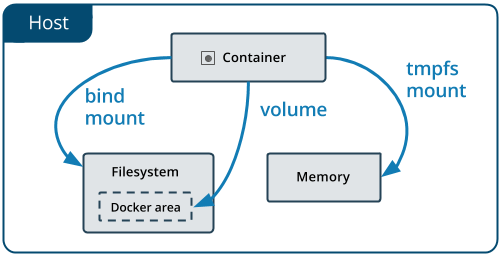

Improper volume mounting is one of the most critical Docker risks.
🔴 Common Issues:
- Mounting host root directory:
-v /:/host- Exposing sensitive directories (
/etc,/root) - Mounting Docker socket
🔥 Critical Impact:
👉 Full host system compromise
🌐 4. Network Vulnerabilities
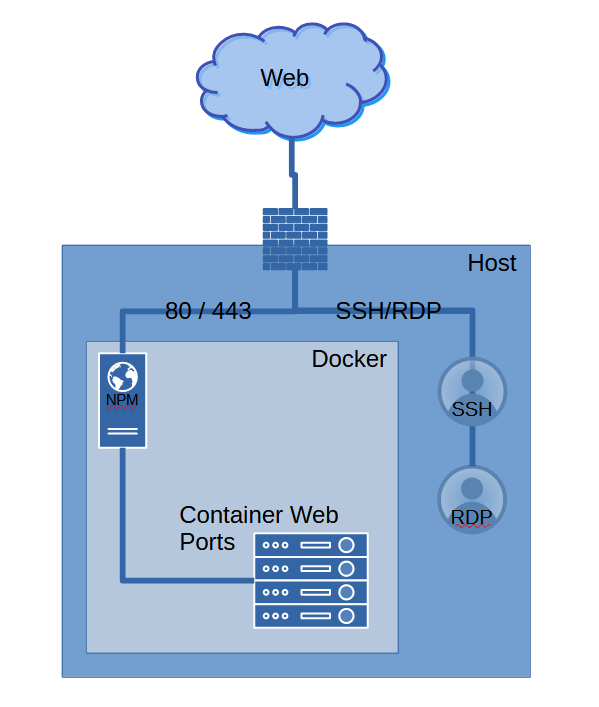
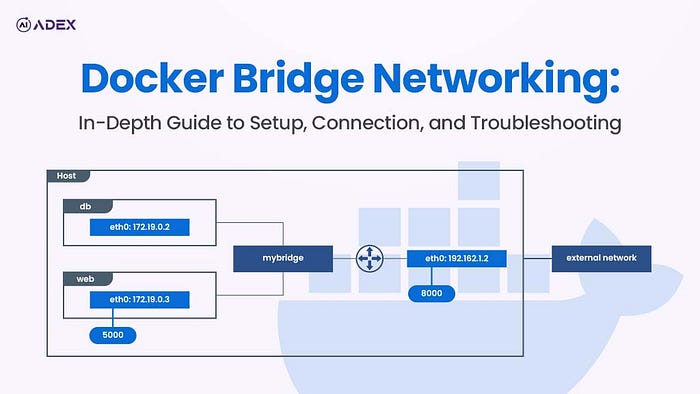

Containers expose services, often without proper restrictions.
🔴 Common Issues:
- Exposed ports (
0.0.0.0) - No firewall rules
- Flat container networking
🛠️ Example:
nmap -p- localhost👉 Identifies open and vulnerable services
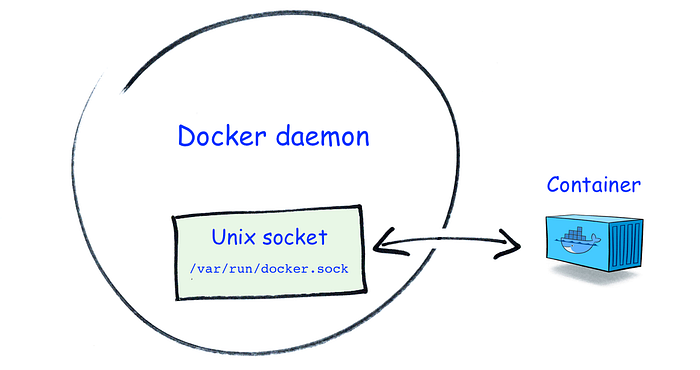
🧠 5. Docker Daemon Vulnerabilities
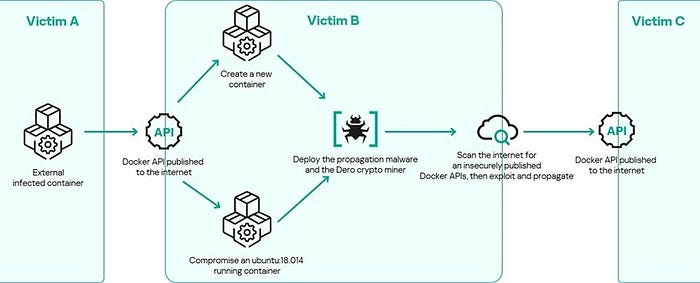
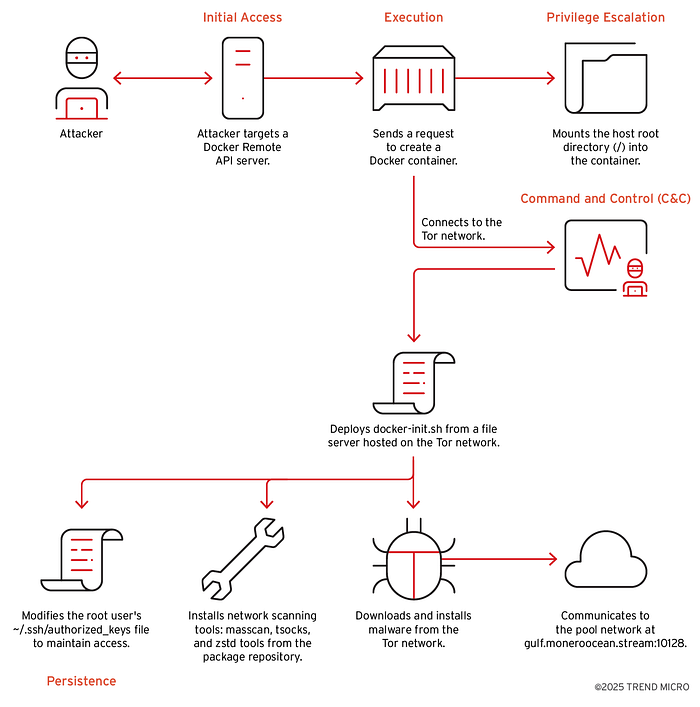
The Docker daemon is the brain of Docker — if compromised, everything is compromised.
🔴 Common Issues:
- Exposed API (
port 2375) - No authentication or TLS
- Misconfigured permissions
🔥 Impact:
👉 Remote attacker can:
- Run containers
- Execute commands
- Mount host filesystem
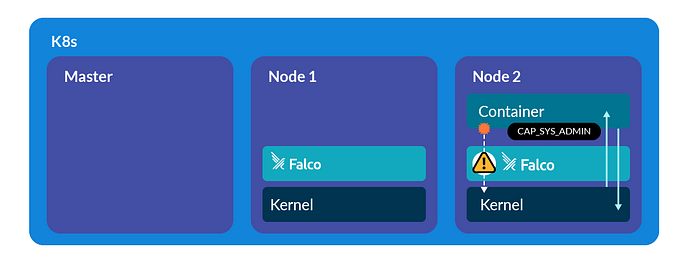
☸️ 6. Orchestration Vulnerabilities (Kubernetes / Swarm)
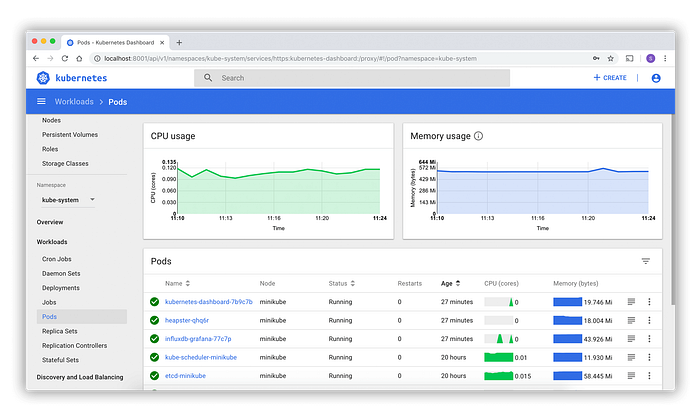


In enterprise environments, Docker is often managed by orchestration tools.
🔴 Common Issues:
- Public Kubernetes dashboards
- Weak RBAC policies
- Plain-text secrets
- Privileged pods
⚠️ Risk:
👉 Full cluster compromise
🔓 7. Container Escape Vulnerabilities

This is the ultimate goal for attackers.
🔴 Causes:
- Privileged containers
- Kernel vulnerabilities
- Misconfigured namespaces
- Docker socket exposure
🔥 Impact:
👉 Escape container → gain host-level access
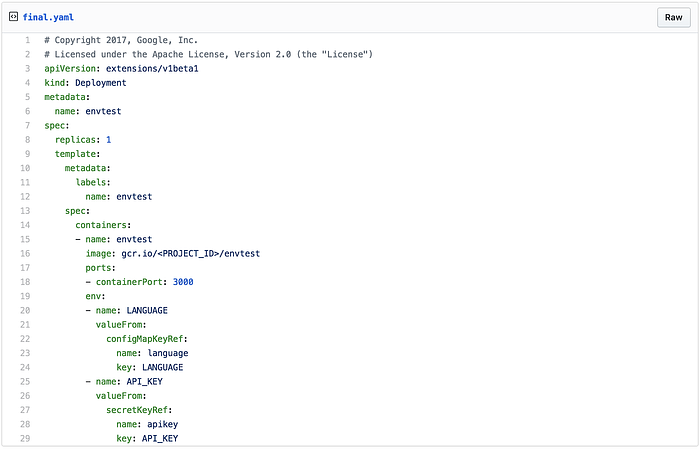
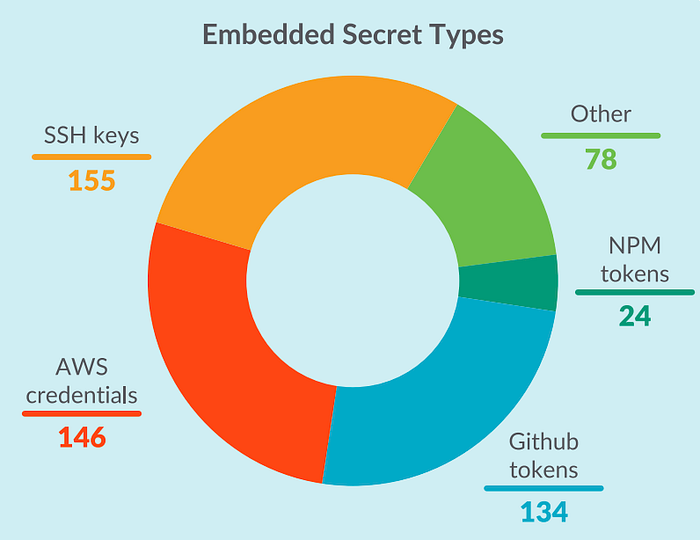
🔑 8. Secrets Management Issues
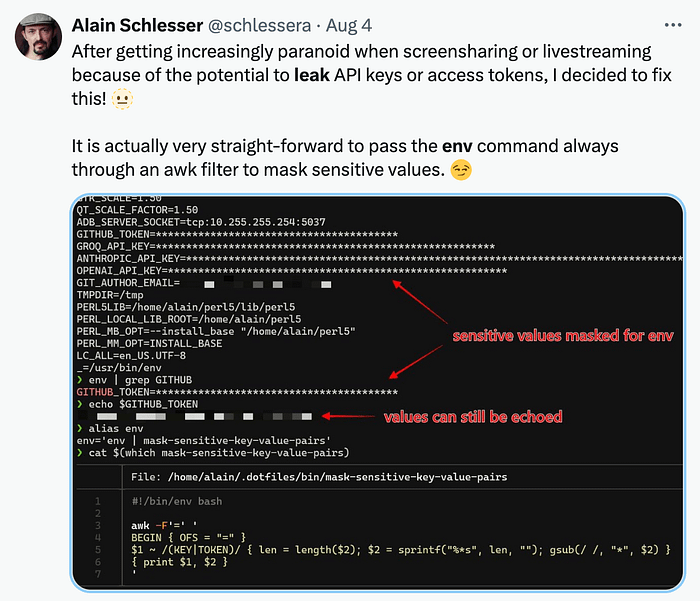


Sensitive data is often mishandled inside containers.
🔴 Common Issues:
- Secrets in environment variables
- Credentials inside images
- Logs exposing tokens
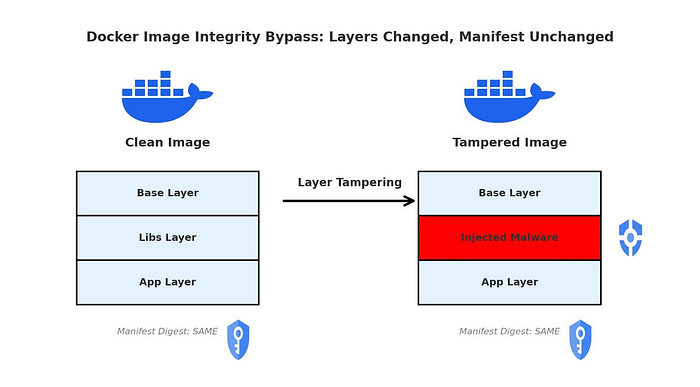
🧬 9. Supply Chain Attacks
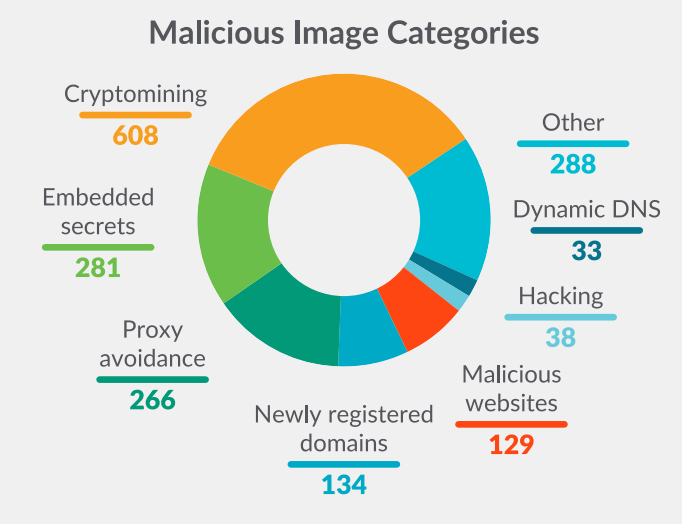


Attackers target the software supply chain.
🔴 Common Issues:
- Fake images (typosquatting)
- Compromised base images
- Malicious dependencies
🛡️ Best Practices to Secure Docker
✔ Use official and verified images
✔ Avoid --privileged mode
✔ Run containers as non-root users
✔ Restrict volume access
✔ Scan images regularly (Trivy, Clair)
✔ Secure Docker daemon with TLS
✔ Monitor runtime behavior (Falco)
🧠 Final Thoughts
Docker security is not just about tools — it's about mindset.
A real attacker doesn't "hack Docker" directly. Instead, they:
- Exploit weak configurations
- Abuse permissions
- Move laterally across containers
- Escape to the host system
👉 If you understand these vulnerability types, you're already ahead of most defenders.
