ABSTRACT
Digital forensics plays a critical role in modern criminal investigations, particularly in cybercrime cases. In Kenya, digital forensic practice is governed by a combination of evidentiary law, procedural law, and cybercrime legislation. This paper provides a detailed examination of the legal foundations of digital forensics in Kenya, analysing admissibility standards, investigative authority, procedural integrity, and evidentiary principles. It further interrogates the structural challenges faced by forensic practitioners, from technical capacity gaps to the evolving threat of AI-generated evidence. It proposes a forward-looking framework to strengthen digital forensic practice in the Kenyan legal context.
Keywords: Digital forensics, Kenya, electronic evidence, chain of custody, cybercrime law, admissibility, data protection, forensic soundness.
1. Introduction
Digital evidence has become indispensable to modern criminal investigations. From cybercrime prosecutions and financial fraud cases to counter-terrorism operations and political corruption inquiries, electronic data serves as a primary source of investigative leads and courtroom proof. In Kenya, the rapid digitisation of commerce, governance, and social interaction has correspondingly elevated the significance of digital forensics as a legal discipline.
Yet the evolution of forensic practice has not been seamless. Kenya's legal system has made commendable strides in recognising electronic records as admissible evidence, but questions of forensic reliability, chain of custody, investigator competence, and technological currency remain deeply contested. This paper provides a structured and detailed analysis of the legal architecture governing digital forensics in Kenya, the forensic processes employed in practice, the evidentiary standards that courts apply, and the challenges that practitioners must navigate.
The analysis draws on the principal statutory instruments governing electronic evidence and cybercrime in Kenya, supplemented by reference to procedural requirements and emerging global best practices. The paper ultimately argues that while Kenya's legal framework is substantively sound, practical implementation requires sustained investment in institutional capacity, procedural standardisation, and legislative modernisation.
2. Legal Foundations of Digital Forensics
Digital forensics in Kenya does not rest on a single statute. Instead, it draws from an interlocking matrix of laws governing evidence, cybercrime, criminal procedure, and data protection. Understanding this matrix is essential before any forensic evidence can be properly gathered, preserved, or presented.
2.1 Evidence Law and the Admissibility of Electronic Records
Kenyan evidence law explicitly recognises electronic records as admissible forms of evidence, subject to the satisfaction of defined threshold conditions. These conditions collectively serve to assure the court of the trustworthiness of the digital material being presented.
The following table summarises the four core admissibility requirements and their forensic implications:
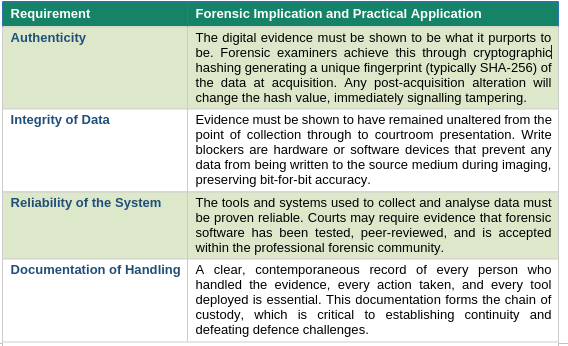
Key Legal Point
Failure to satisfy any of these requirements does not automatically render evidence inadmissible, but it substantially weakens the probative weight accorded to that evidence and opens the door to vigorous defence challenges. Courts retain discretion to exclude evidence where procedural deficiencies are egregious or where prejudice to the accused would result.
2.2 Cybercrime Legislation: Investigative Powers
Kenya's cybercrime legislation provides the operational backbone for digital forensic investigations. It grants law enforcement specific powers to engage with digital environments and collect electronic evidence in a manner that survives legal scrutiny.
The three principal powers conferred are:
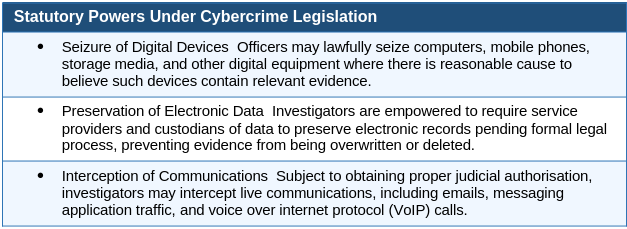
Each of these powers carries corresponding obligations. Seizures must be conducted pursuant to a valid warrant in most circumstances. Preservation orders must specify the scope and duration of required preservation. Interceptions require prior judicial sanction and must be conducted proportionately. Failure to comply with these obligations may result in evidence being excluded and potentially expose investigators to civil or criminal liability.
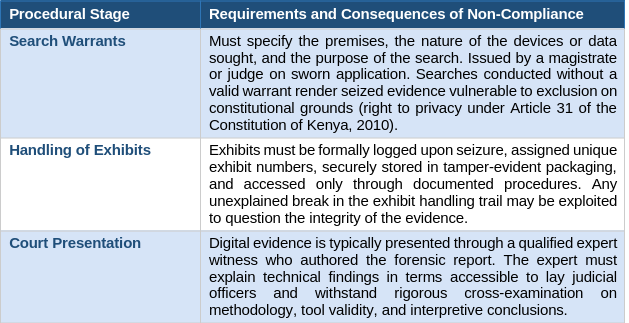
2.3 Criminal Procedure: Warrants, Exhibits, and Court Presentation
Procedural law governs the mechanics of evidence gathering from inception to courtroom delivery. Its requirements are not mere formalities; they are substantive legal protections for accused persons, and courts treat procedural compliance as integral to the fairness of the criminal process.
2.4 Data Protection: Balancing Investigation and Privacy
Digital forensic investigations inherently involve the processing of personal data. Kenya's data protection legislation imposes obligations on all entities that process personal data, including law enforcement agencies conducting forensic examinations to handle such data lawfully, proportionately, and securely.
For forensic practitioners, this legislative framework creates a tripartite set of obligations:
- Justification for Processing: There must be a lawful basis for the collection and examination of personal data. In criminal investigations, this basis typically derives from statutory authority (a warrant or preservation order) or legitimate law enforcement necessity. Examiners who collect or retain data beyond the scope of authorisation may breach data protection law.
- Data Minimisation: Investigators should collect only the data necessary for the specific investigative purpose. Indiscriminate data harvesting, for example, imaging an entire corporate server when only specific files are sought, may be disproportionate and unlawful.
- Protection of Third-Party Information: Forensic images of devices frequently contain personal data belonging to third parties who are not suspects in the investigation (e.g., contacts, communications, stored photographs). Protocols must be established to restrict access to and use of such data to only what is necessary and proportionate.
Tension in Practice
Data protection obligations can create practical friction with forensic imperatives. The gold standard forensic practice of imaging entire devices to preserve all potentially relevant data may be in tension with the principle of data minimisation. Practitioners must develop protocols that satisfy both evidentiary integrity requirements and data protection compliance, an increasingly important challenge in enterprise and cloud-based investigations.
3. The Digital Forensic Process in Practice
Digital forensic investigations follow a structured, internationally recognised methodology. Each phase of the process is not merely a technical step; it carries legal significance that directly impacts the admissibility and weight of evidence in court.
3.1 Phase One: Identification
Identification is the foundational phase in which investigators recognise and document potential sources of digital evidence. At this stage, the investigator must cast a sufficiently wide net to capture all potentially relevant data while maintaining clear records of the investigative rationale.
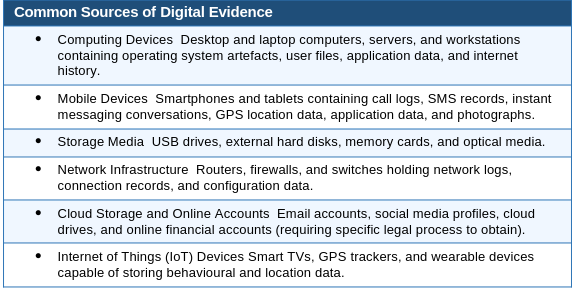
Potential sources of digital evidence in the Kenyan investigative context include:
3.2 Phase Two: Preservation
Preservation is arguably the most legally consequential phase of the forensic process. It is at this stage that the measures are taken to ensure that evidence is captured in a state that can be proven to be identical to the original, a prerequisite for any court to trust the findings derived from that evidence.
Core preservation techniques and their legal significance are as follows:
- Write Blockers: Hardware or software write blockers are interposed between the forensic workstation and the source storage device. They physically or logically prevent any write commands from reaching the source device, ensuring that the examination process itself does not alter the original data. The use of a write blocker is generally considered a minimum standard for forensically sound evidence acquisition.
- Forensic Imaging: Rather than examining the original device directly, forensic examiners create a bit-for-bit image, an exact copy of the entire storage medium, including deleted file space and slack space. This image is what is subsequently analysed, leaving the original device untouched and preserved for independent verification if required.
- Cryptographic Hashing: Upon creating the forensic image, a cryptographic hash value (most commonly SHA-256) is calculated for both the original device and the image. A match between these values provides mathematical proof that the image is an exact duplicate. The hash value is recorded in the forensic documentation and can be verified by any party at any time.
- Environmental Controls: Where volatile data is at risk (e.g., data held in RAM or encrypted containers that would be lost if the device is powered off), specialist procedures such as live acquisition may be required. These procedures carry their own integrity considerations and must be meticulously documented.
3.3 Phase Three: Analysis
Analysis is the technical core of the forensic process, the phase in which the examiner interrogates the preserved data to identify evidence relevant to the investigation. Analytical scope must be guided strictly by the investigative mandate and the terms of any authorising legal instrument.
Key analytical areas include:

3.4 Phase Four: Documentation
Documentation is the evidentiary paper trail that transforms technical findings into legally usable evidence. Comprehensive documentation serves multiple functions: it establishes the chain of custody, enables independent replication of the analysis, supports the expert's testimony, and provides the court with a transparent account of the investigative methodology.
A complete forensic case file should include:
- Exhibit log: Detailed record of every item seized, including make, model, serial number, condition, date and time of seizure, and seizing officer's identity.
- Acquisition log: Record of the imaging process, including write blocker used, hash values, imaging tool and version, start and end times.
- Analysis log: Contemporaneous notes of analytical steps taken, tools used (with version numbers and hash values of the tools themselves), queries run, and observations made.
- Forensic report: A formal written report summarising the evidence examined, methodology employed, findings, and the examiner's opinions and conclusions.
- Appendices: Supporting exhibits including screenshots, extracted files, timeline charts, and any other material relied upon in forming the expert's opinion.
Courts have increasingly scrutinised the quality and completeness of forensic documentation. An examiner who cannot produce a contemporaneous analysis log, relying instead on memory, will face credibility challenges that may undermine otherwise robust technical findings.
3.5 Phase Five: Court Presentation
The culmination of the forensic process is the presentation of findings to the court. The forensic examiner typically appears as an expert witness, having been qualified by the court to give opinion evidence on matters within their area of expertise, a status not automatically afforded to all witnesses.
Effective forensic expert testimony requires the examiner to:
- Explain complex technical concepts in language accessible to judicial officers, magistrates, assessors, and lay jurors who may have no technical background.
- Present findings objectively, acknowledging both inculpatory and exculpatory evidence without advocacy for either party.
- Withstand cross-examination by defence counsel challenging methodology, tool reliability, analytical conclusions, and chain of custody.
- Maintain composure and credibility under pressure, distinguishing clearly between matters within their expertise and matters outside it.
4. Evidentiary Principles Governing Digital Evidence
Beyond the procedural framework, three core evidentiary principles govern the treatment of digital evidence in Kenyan courts. Mastery of these principles is as important for forensic practitioners as technical proficiency.
4.1 Chain of Custody
The chain of custody is the documented record of the continuous control and integrity of evidence from the moment of seizure until its presentation in court. It answers three fundamental questions that any court must be satisfied about before placing weight on physical or digital evidence:
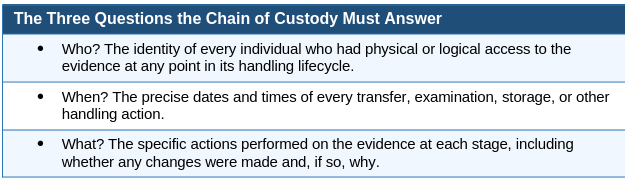
A broken chain of custody, for example, a gap in the exhibit log where evidence cannot be accounted for over a period of time, does not automatically result in exclusion of the evidence, but it creates a gap that the prosecution must be prepared to explain. Defence counsel will invariably exploit any such gap to raise reasonable doubt as to the integrity of the evidence.
In digital forensic cases, maintaining the chain of custody is particularly complex because evidence may pass through multiple hands (seizing officer, forensic examiner, exhibits officer, expert witness), be accessed remotely by multiple analysts, and exist simultaneously in multiple forensic copies held at different locations. Rigorous access logging and audit trail management are essential.
4.2 Forensic Soundness
Forensic soundness is the principle that the acquisition and examination of digital evidence must not alter the original data. It is the digital analogue of the principle that physical crime scene evidence should not be disturbed before being photographed and documented. Three requirements underpin forensic soundness:
- Non-Modification: The original evidence must remain in exactly the state in which it was found. Any unavoidable modification (for example, in live acquisition of volatile data) must be documented, explained, and justified.
- Validated Tools: The forensic tools used must have been subjected to independent testing and validation. Industry-standard tools such as EnCase, FTK (Forensic Toolkit), and open-source tools such as Autopsy and The Sleuth Kit are widely accepted. Novel or unvalidated tools invite challenges.
- Reproducibility: A hallmark of sound forensic science is that independent examiners using the same methodology and tools, applied to the same evidence, should reach substantially the same findings. Reproducibility is both a scientific quality standard and a legal safeguard: it enables the defence to commission an independent examination to verify or challenge the prosecution's forensic conclusions.
4.3 Expert Credibility and the Weight of Forensic Opinion
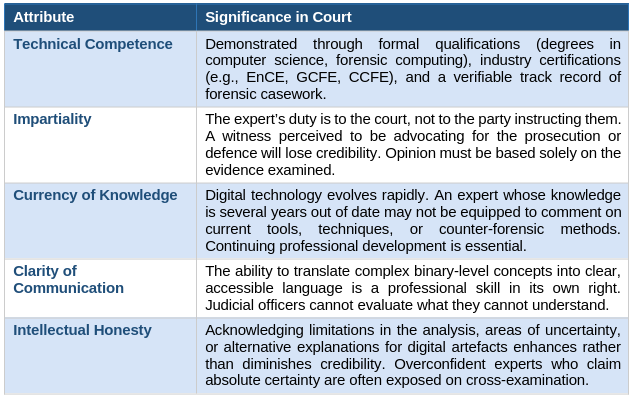
In adversarial legal systems such as Kenya's, the weight accorded to expert evidence depends heavily on the credibility and qualifications of the expert. A forensic examiner who cannot articulate the basis for their opinions, who has not maintained up-to-date expertise, or who presents as an advocate rather than an impartial expert risks having their evidence discounted or disregarded entirely.
The following attributes are central to expert credibility:
5. Challenges in Digital Forensics in Kenya
Despite the relative robustness of the legal framework, digital forensics practice in Kenya confronts a series of structural, technical, and legal challenges that limit its effectiveness and, in some cases, threaten the integrity of the forensic enterprise.
5.1 Technical Capacity Constraints
The forensic technology landscape is characterised by rapid tool evolution, high licensing costs, and demand for highly specialised skills that are in short supply in Kenya.
- Limited Access to Advanced Forensic Tools: Premium forensic platforms such as EnCase and Cellebrite UFED (Universal Forensic Extraction Device) command significant licensing costs that many agencies are unable to sustain. This can result in reliance on older tool versions or less capable alternatives.
- Skills Gap: Specialist areas such as mobile forensics, malware analysis, memory forensics, and cloud data acquisition require advanced expertise that is not yet widely available within Kenyan law enforcement and prosecution services.
- Digital Forensics Laboratory Infrastructure: The absence of sufficiently equipped, standardised forensic laboratories in regional centres means that cases may be delayed while evidence is transported to Nairobi for examination, increasing handling risks.
- Anti-Forensics Awareness: As public and criminal awareness of digital forensics grows, so does the deployment of anti-forensic techniques, such as encryption, data wiping, and steganography to defeat forensic examination. Investigators must keep pace with these countermeasures.
5.2 Legal and Jurisprudential Complexity
The legal landscape governing digital forensics is not static. It is shaped by overlapping statutory instruments, evolving judicial interpretation, and the incremental development of case law that has not always kept pace with technological change.
- Legislative Overlap and Inconsistency: Multiple statutes, including evidence law, cybercrime legislation, data protection law, criminal procedure codes, and sector-specific regulations, interact in ways that are not always coherent. Practitioners must navigate this complexity without the benefit of clear consolidating legislation.
- Evolving Judicial Attitudes: Judicial officers differ in their familiarity with and comfort around digital evidence. Inconsistent judicial treatment of admissibility applications creates uncertainty for practitioners and prosecutors.
- Cross-Border Evidence Challenges: Many cybercrimes involve evidence held on servers in foreign jurisdictions. Obtaining this evidence through mutual legal assistance treaties (MLATs) is often slow, cumbersome, and dependent on the cooperation of foreign governments and private service providers.
5.3 Emerging Technologies Posing Novel Forensic Challenges
Three categories of emerging technology pose particularly acute challenges to established forensic paradigms:
Challenge 1: Encrypted Communications
End-to-end encrypted messaging platforms (such as Signal, WhatsApp, and Telegram) present a significant barrier to forensic access. Even where a device is lawfully seized, the content of communications may be inaccessible without the encryption keys. Lawful interception frameworks designed for traditional telephony do not straightforwardly apply to modern encrypted communications.
Challenge 2: Cloud Computing
Data increasingly resides not on local devices but on cloud servers operated by large technology companies, often headquartered in the United States or Europe. Accessing this data requires navigating complex jurisdictional frameworks, lengthy MLAT processes, and the terms of service of private companies. Emergency disclosure processes exist but are inconsistently applied.
Challenge 3: AI-Generated Evidence and Deepfakes
Advances in artificial intelligence have made it possible to generate highly convincing synthetic audio, video, and photographic content, so-called 'deepfakes'. This creates a new category of forensic challenge: not merely finding and preserving genuine evidence, but detecting and excluding fabricated evidence. The forensic community is developing detection tools, but courts and legal practitioners are only beginning to grapple with the evidentiary implications.
6. Future Directions and Recommendations
Strengthening digital forensics in Kenya requires a multi-pronged approach addressing legislative, institutional, technical, and capacity dimensions simultaneously.
6.1 Standardisation of Forensic Procedures
Kenya would benefit substantially from the development and adoption of a national digital forensic standard, a framework document specifying minimum procedural requirements for evidence acquisition, analysis, documentation, and court presentation. Such a standard would provide a benchmark against which practitioner conduct could be measured, reduce inconsistency in forensic output, and give courts a reference point for evaluating the acceptability of forensic methodologies.
Reference may be drawn from international frameworks including the Scientific Working Group on Digital Evidence (SWGDE) guidelines, the International Organisation for Standardisation (ISO) 17025 standard for testing laboratories, and the ACPO (Association of Chief Police Officers) Principles for Digital Evidence, which remain influential internationally despite their UK origins.
6.2 Investment in Training and Institutional Capacity
Sustainable improvement in forensic quality requires sustained investment in human capital. Recommended measures include:
- Establishment of a dedicated Digital Forensics Training Institute, potentially in partnership with regional universities and international organisations, offering structured career pathways for forensic examiners.
- Mandatory continuing professional development requirements for practising forensic examiners, ensuring currency with evolving tools and techniques.
- Specialist training for prosecutors and judicial officers in digital evidence evaluation reduces the burden on forensic experts to educate the court on basic concepts during trials.
- Investment in regional forensic laboratory infrastructure to reduce centralisation bottlenecks and improve turnaround times.
6.3 Legislative Modernisation
Kenya's legislative framework, while substantively sound, would benefit from targeted modernisation to address gaps and inconsistencies identified in practice:
- Consolidated Digital Evidence Legislation: A dedicated statute consolidating and clarifying admissibility requirements, forensic standards, and procedures for digital evidence would reduce practitioners' reliance on disparate overlapping instruments.
- Cloud Evidence Framework: Clearer legislative provisions governing the process for obtaining data from cloud service providers, including emergency access procedures, time limits, and oversight mechanisms, would reduce delay and uncertainty.
- AI Evidence Guidelines: The legislature or judiciary should develop specific guidance on the treatment of AI-generated evidence, including authentication requirements and the evidential weight to be accorded to deepfake detection findings.
6.4 Ethical Integration of AI in Forensic Practice
AI tools hold genuine promise for forensic practice, offering the ability to process vast datasets rapidly, identify patterns invisible to human examiners, and detect manipulated content. However, their deployment in the forensic context must be governed by clear legal and ethical safeguards:
- Transparency: The operation of AI tools used in forensic analysis must be explainable to courts. 'Black box' algorithms whose outputs cannot be interrogated and understood are problematic from an evidentiary standpoint.
- Validation: AI forensic tools must be subject to rigorous independent validation before deployment in casework, with results replicable by human analysts.
- Accountability: Clear lines of professional responsibility must exist; the forensic examiner who deploys an AI tool remains professionally responsible for the conclusions drawn from its outputs.
7. Conclusion
Digital forensics in Kenya occupies a position of increasing strategic importance within the criminal justice system. The legal framework that governs its practice, drawing on evidence law, cybercrime legislation, criminal procedure, and data protection, provides a substantively solid foundation for the collection, preservation, and presentation of electronic evidence.
Yet the integrity and effectiveness of digital forensic practice are not secured by legal frameworks alone. It depends on the competence, resources, and professional standards of the practitioners who operate within those frameworks; on judicial officers who are sufficiently equipped to evaluate forensic evidence critically; and on a legislature and policy apparatus that responds with agility to the rapid pace of technological change.
The challenges examined in this paper, technical capacity constraints, legal complexity, and the disruptive potential of emerging technologies are real and significant. But they are not insurmountable. Through standardisation of forensic procedures, sustained investment in human and institutional capital, targeted legislative modernisation, and the ethical integration of emerging tools, Kenya can build a digital forensic capability that is both technically rigorous and legally robust.
The stakes are high. Digital evidence increasingly determines the outcome of prosecutions for serious crimes, including terrorism, organised financial crime, and cybercrime. Getting digital forensics right is not merely a technical imperative; it is a justice imperative.
References and Further Reading
The following legislative instruments and academic resources form the principal sources for this analysis:
- Constitution of Kenya, 2010 (Articles 31 and 50 Right to Privacy and Fair Trial)
- Evidence Act (Cap. 80), Laws of Kenya (Electronic Records Provisions)
- Computer Misuse and Cybercrimes Act, 2018 (№5 of 2018)
- Criminal Procedure Code (Cap. 75), Laws of Kenya
- Data Protection Act, 2019 (№24 of 2019)
- Karie, S. & Mativo, J. (2021). 'Digital Forensics and Admissibility of Electronic Evidence in Kenyan Courts.' Nairobi Law Review, 14(2), 112–134.
- Scientific Working Group on Digital Evidence (SWGDE). Best Practices for Computer Forensic Acquisitions. SWGDE, 2018.
- Casey, E. (2019). Digital Evidence and Computer Crime: Forensic Science, Computers and the Internet (3rd ed.). Academic Press.
- Carrier, B. (2005). File System Forensic Analysis. Addison-Wesley Professional.
- ISO/IEC 27037:2012 Guidelines for Identification, Collection, Acquisition, and Preservation of Digital Evidence. International Organisation for Standardisation.
- Kenneally, E.E. & Bailey, M. (2014). 'Cyber-Risk Management: Technical and Legal Challenges.' IEEE Security & Privacy, 12(3), 60–67.