Every bug hunter knows that sometimes the most interesting vulnerabilities aren't buried deep within complex application logic, but are hiding in plain sight. Recently, while hunting on Flipkart, I stumbled upon an intriguing case of Third-Party Asset Exposure (CWE-16) that highlighted a unique supply chain risk on e-commerce platforms.
Even though this finding ultimately turned out to be a duplicate, it was a great reminder to always check the small details. Here is a breakdown of how a simple misconfiguration by a third-party seller could have been leveraged to distribute malware to unsuspecting buyers.
The Reconnaissance: Exploring Product Pages
While analyzing the various components that make up a Flipkart product page, I decided to pay close attention to the technical specifications section. On e-commerce sites, third-party sellers often populate these fields with data.
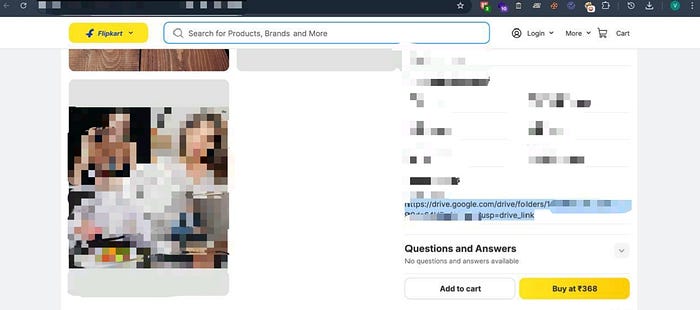
While checking the specifications for a specific electronic accessory, I noticed something unusual in one of the technical parameter fields. Instead of a standard alphanumeric value, the seller had embedded a raw Google Drive URL. The link was seemingly intended to share additional high-resolution images or digital manuals with potential buyers.

The Vulnerability: A Misconfigured Third-Party Asset
Curiosity took over. What happens when a platform with massive inherent trust (like Flipkart) hosts an outbound link managed by a third party?
I copied the URL and opened it in an incognito window to ensure none of my active Google sessions influenced the access level. The link directed me to a Google Drive folder containing product assets. However, I immediately noticed the + New button and upload capabilities were active.
The seller had misconfigured the directory permissions to "Anyone with the link can Edit."
Because this link was hosted natively within a verified Flipkart product specification table, it inherited the trust of the platform. An attacker could trivially abuse this writable directory without needing any authentication on Flipkart or Google.
The Impact: Turning a Product Page into a Trap
This simple misconfiguration presented a critical Supply Chain and Customer Trust risk. An attacker with Editor access to this linked folder could execute several highly damaging scenarios:
- Malware Distribution: An attacker could delete the legitimate product images and upload a malicious payload disguised as
Product_User_Manual_and_Warranty.pdf.exe. Customers clicking the link from the Flipkart listing would inherently trust the file and execute it, leading to device compromise. - Targeted Phishing: The attacker could upload a document containing a phishing link (e.g., a fake form stating, "Click here to claim your Flipkart cashback for this purchase"), leading to direct credential theft.
- Brand Defacement: The legitimate product images could be replaced with inappropriate content, explicit material, or competitor advertisements, causing direct reputational damage to the platform.
The Disclosure & Outcome
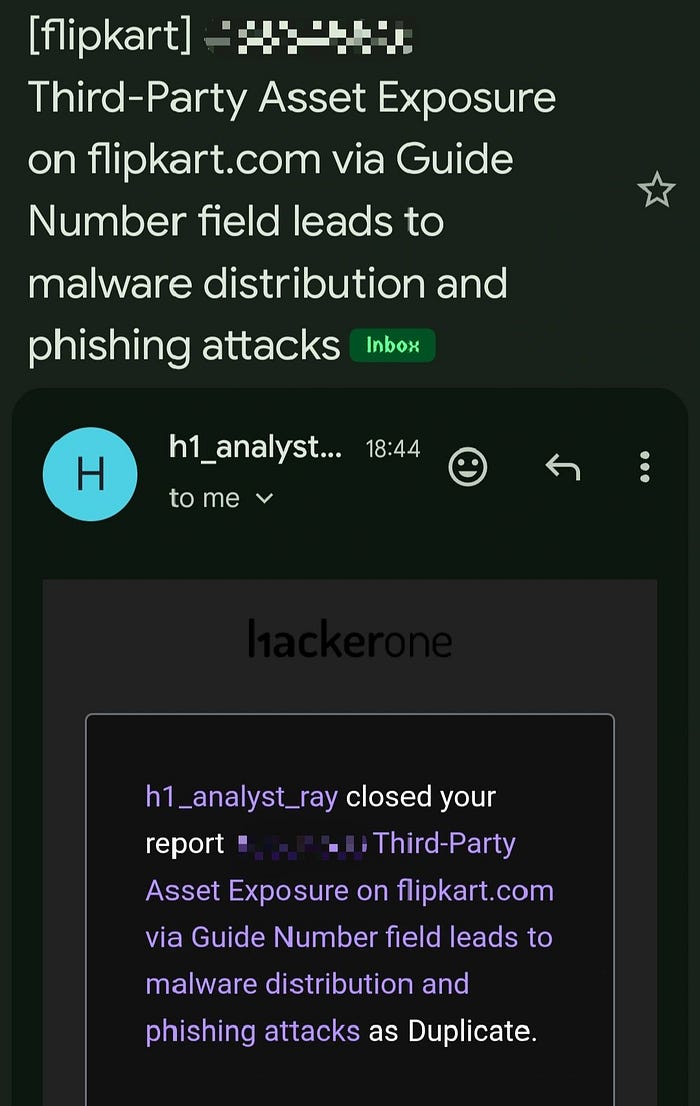
I immediately documented my findings — ensuring I adhered strictly to Flipkart's Responsible Disclosure Policy by only verifying the visual presence of edit access without actually modifying or uploading any files — and submitted the report via HackerOne.
After the triage process, the report was closed as a Duplicate. Another researcher had spotted this exact vector a few months prior!
Key Takeaways
Getting a "Duplicate" on a high-impact bug is always a bittersweet moment. On one hand, you miss out on the bounty. On the other hand, it is the ultimate validation of your methodology. It proves you are looking in the right places and finding legitimate, impactful vulnerabilities.
Lessons for Hunters:
- Don't ignore the data fields: Inputs that are meant to hold plain text but end up holding URLs or scripts are always worth investigating.
- Follow the outbound links: If an application links to a third-party service (S3 buckets, Google Drive, Notion docs), always check the access controls of the destination. Broken Link Hijacking and Misconfigured Assets are still incredibly prevalent.
Happy hunting!
