Hello everyone, hope you all are doing good. Today I came to share something interesting which I came across during my recent testing. Actually I found this issue last night after reporting I wanted to create a article to make others understand this issue and check for similar issues.
How It Began
So when I was ready for hunting yesterday I wanted to try something new, so I started looking for other bug bounty platforms which are not that much popular like bugcrowd, hackerone, integriti etc. I wanted a less popular platforms which also pays bounties. At last I found one, I started exploring a target which paid a decent amount as average bounties.
The Workflow
Initially tested for html injection in their account creation via firstname and second name but it didn't worked. The target provided staging website which was a clone of their real website like staging.target.app.
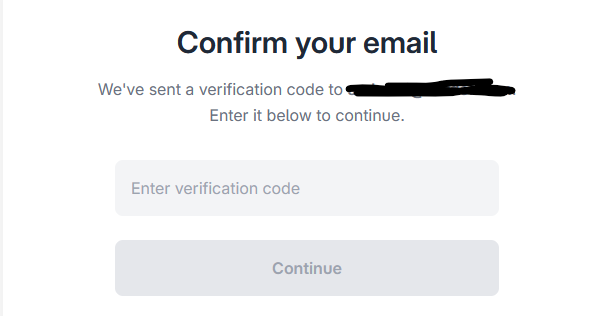
I started exploring the account creation function. So this was the account creation workflow user go to https://staging.target.app/signups/new endpoint enter users email address, then the website will send a verification code to users email address and when user enters the correct code the users was taken to the onboarding page which allowed the users to enter their full details including password and get inside the account.
First when I found the verification my instinct was to do response manipulation and bypass the security check, I created a normal account and checked their backend workflow. When user was entering the right verification code the response to that POST request was a 302 Found status code. So without wasting further time I entered an email and on the verification page I entered a wrong code and captured the request and the response was 422 Unprocessable Entity, I manipulated the response to 302 Found and forwarded the response but nothing changed and I was in the same page.
The Breakthrough
So at this point I was a bit disappointed, I went back to browser and tried to created another account just to see anything unusual is coming up
> I went to https://staging.target.app/signups/new
> Entered email address and click submit
> I was taken to a page which was like: https://staging.target.app/signups/<RANDOM-CODE-12345ABC> and was asked to enter the verification code.
> When entering the details I was taken to a url like:
https://staging.target.app/onboarding/account_details/<RANDOM-CODE-12345ABC>
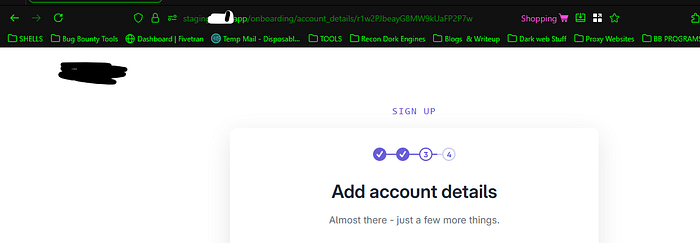
I just had a feeling if I manually browsed to the onboarding endpoint will they allow me to continue the account creation without verification, I created another for testing when entered the email and click submited they send me a token and took me to :
https://staging.target.app/signups/<RANDOM-CODE-09876XYZ>
I knew the random code was the user ID generated, I noted that code in my notepad and manually created the onboarding url:
https://staging.target.app/onboarding/account_details/<RANDOM-CODE-09876XYZ>
I pasted the url to the browser and YES the verification was bypassed and the website asked me to fill in the rest of information, I filled everything and clicked submit and the account was created. I tested it again and it worked.
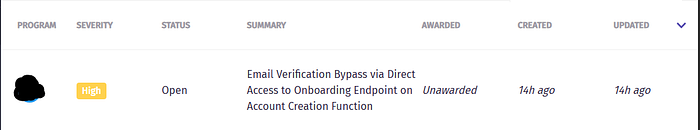
I created a bug report and reported to the target and all these happened yesterday night. I hope this one doesn't come as a duplicate.
If you liked this article, feel free to check out the rest…