Surveillance cameras are installed to keep places safe — but what happens when the cameras themselves become the vulnerability? Across 82 countries, 14,706 IP cameras running Milesight firmware, sold under various brand names by OEM and white-label vendors worldwide, have been found carrying five critical security vulnerabilities, earning a maximum CVSS score of 9.8. These are not obscure industrial devices tucked away in a server room — they are watching over hotels, warehouses, offices, and commercial facilities globally, and this research reveals exactly how exposed they really are.
First up, CVE-2026–32644 (CVSS 9.8 — Critical) — a hard-coded cryptographic key baked into the firmware across all 82 affected product families. Second, CVE-2026–27785 (CVSS 8.8 — High) — hard-coded credentials, again sitting inside the firmware, affecting the same broad product range. Third, CVE-2026–20766 (CVSS 8.8 — High) — a heap-based buffer overflow, capable of crashing the device or worse. Fourth, CVE-2026–32649 (CVSS 6.8 — High) — OS command injection through the web interface. And finally, CVE-2026–28747 (CVSS 7.1 — High) — an authorization bypass through weak key generation in the firmware. Every single one of these affects the same massive product family — MS-C, MS-N, TS, PMC series and more — all the way from bullet cameras to video intercoms, spanning firmware versions across dozens of product lines.
Now comes the interesting part — finding exactly how many of these vulnerable devices are sitting exposed on the open internet. The journey started with a YouTube video. While analysing a Milesight camera login page demonstration (yes, sometimes the most useful research happens on YouTube),
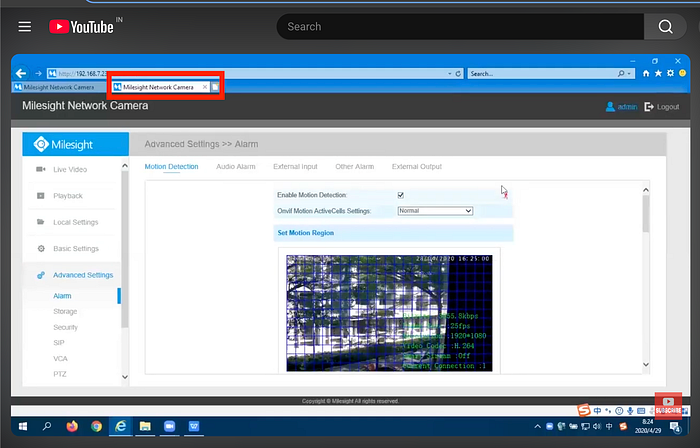
the page title read "Milesight Network Camera" — a simple but useful starting point. Running that as a Modat Magnify signature:
web.html~"Milesight Network Camera"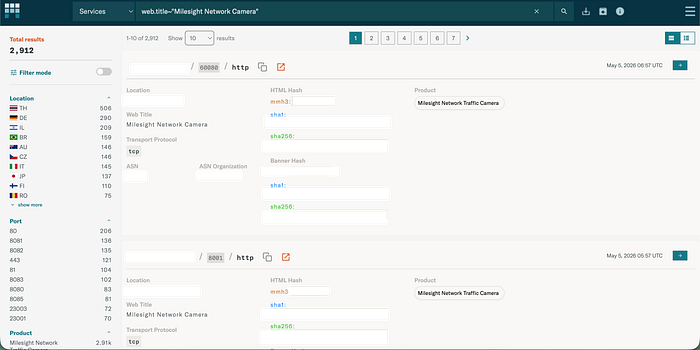
returned 2,912 devices worldwide. Not bad — but not the full picture either, because this only catches devices still wearing the Milesight name badge. Digging deeper into the HTML source of the camera's web interface revealed something more interesting — two structural identifiers, activeDiv and activeMask, sitting inside the page code regardless of whatever brand name was on the outside. These strings belong to the firmware's web interface framework — not the branding layer — meaning white-labeled variants carry them too. Firing this refined signature into Modat Magnify:
web.html~"activeDiv" and web.html~"activeMask"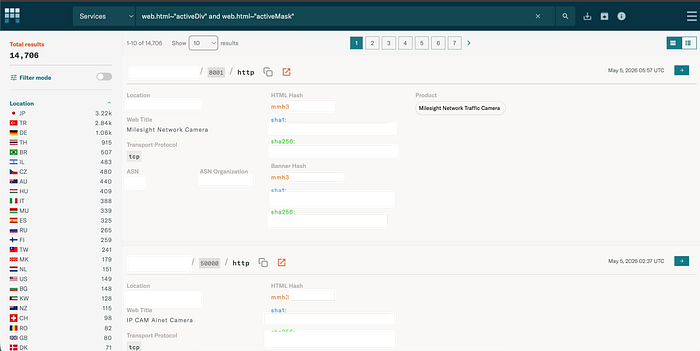
returned an alarming 14,706 devices across 82 countries — nearly five times the original number. That gap between 2,912 and 14,706 tells its own story, and Modat Magnify makes it impossible to ignore — the majority of exposed devices are white-labeled of milesight , rebranded, and completely off the radar of anyone searching specifically for Milesight vulnerabilities.
While analysing the 14,706 results returned by Modat Magnify, something immediately stood out — a significant portion of these devices were not presenting themselves as Milesight cameras at all. Different brand names, different logos, different login page designs — but underneath, the same Milesight firmware, and the same five critical vulnerabilities. These white-labeled variants are perhaps the most concerning part of this entire research, because their owners have no obvious reason to connect their device to a Milesight security advisory. They will not search for it, they will not find it, and their devices will remain unpatched — not out of negligence, but simply because nobody told them their camera is affected.
Impact: When a surveillance camera is compromised, it is not just a device that is lost — it is the physical space it was protecting. Across 82 countries, 14,706 cameras running vulnerable Milesight firmware, many of them hiding under white-label brand names, are potentially exposed. Hotels, offices, warehouses, and critical commercial facilities worldwide are in the frame — and not in the way they intended.
In a world where cameras are supposed to see everything, five CVEs proved that the biggest blind spot was the camera itself.