For over three years, delivr.to has helped security teams answer a deceptively simple question: what actually reaches users' inboxes? That question hasn't gone away — but it's no longer the only one worth asking.
Today, we're releasing Web Campaigns — a new campaign type that tests whether payloads are successfully downloaded via web browser, evaluating security controls along the entire download chain: from network proxies to endpoint detection and response, and everything else in between.
What Web Campaigns Test
To be explicit about the control chain that web campaigns exercise:
- DNS filtering and web proxies — Does the organisation's network allow the download URL to resolve and connect?
- DPI firewalls and network sandboxes — Is the file inspected and detonated at the network edge?
- Browser-native protection — Does Chrome's Safe Browsing, Edge's SmartScreen, or Firefox's built-in scanner flag the download?
- Browser extensions and plugins — Do any security-focused browser extensions intervene? (e.g. Push Security's ClickFix detection)
- Endpoint detection and response — Does the EDR agent quarantine or block the file on write?
- Post-download scanning — Does scheduled or real-time antimalware scanning catch the file after it lands?
Each of these layers operates independently, and a failure at any single point means the payload reaches the user. Web campaigns give security teams a structured, repeatable way to identify which layers are working and which are not.
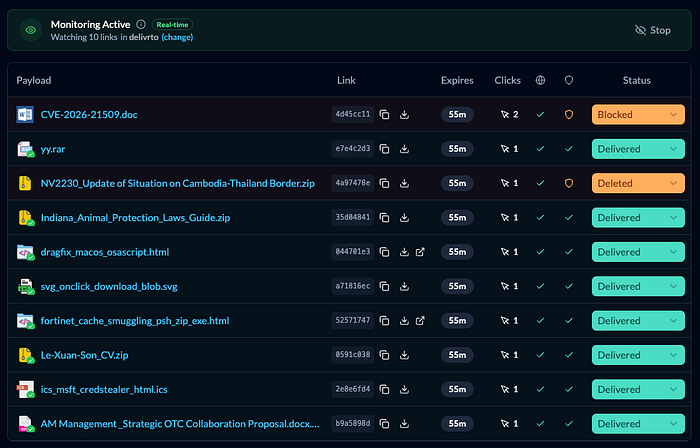
Tracking Results
When approaching delivr.to web delivery testing, we wanted the same focus on painless but comprehensive results collection that drives our email campaigns. That meant building automated verification directly into the download process — not just logging access events.
Server-side, each download is tracked with timestamp, source IP and user-agent. The results page surfaces these events in real-time, showing user-driven fetches, as well as any potential sandboxing 'clicks' that might occur at the same time.
Then, payload delivery is verified at two stages — from the hosted link to the browser, then from the browser to the endpoint file system.
Every download is hash-checked in the browser against an expected value. If it matches, the file made it through any proxy/SWG/network sandboxes intact. This works on all browsers with no configuration.
On Chromium browsers with our 'Download Monitoring' feature enabled, payloads are written to a selected folder via the File System Access API. delivr.to confirms a successful file write and also watches for post-write deletions. If Chrome's Safe Browsing blocks the initial write, the result updates automatically. If an endpoint security solution subsequently acts on the file, this result is captured too.
If this Chromium File System Access API sounds familiar, we previously published research on its weaponisation here:
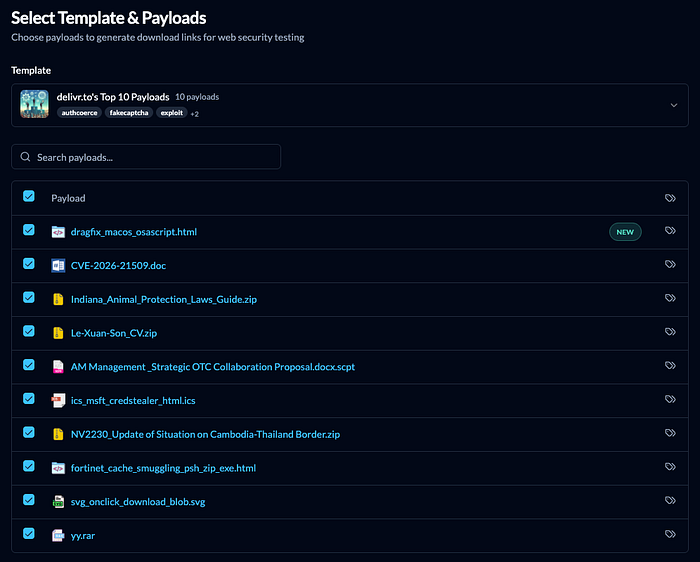
Launching a Campaign
Web campaigns follow a workflow that will be familiar to existing delivr.to users. The core concepts are the same — select payloads, launch a campaign, analyse results — with the delivery mechanism adapted for web-based testing.
Selecting web delivery from the sidebar, payload selection works identically to email campaigns — choose a template, browse the payload library, toggle individual payloads on or off.
Email body-only payloads are naturally filtered out, since web campaigns deliver files via hosted download links, rather than inline email content.
Campaign configuration is simplified. There are no recipients, senders, subject lines, or delivery delays. You configure the campaign name, link expiry duration, and whether to receive email results on completion. Web campaigns launch immediately — there is no scheduled start.
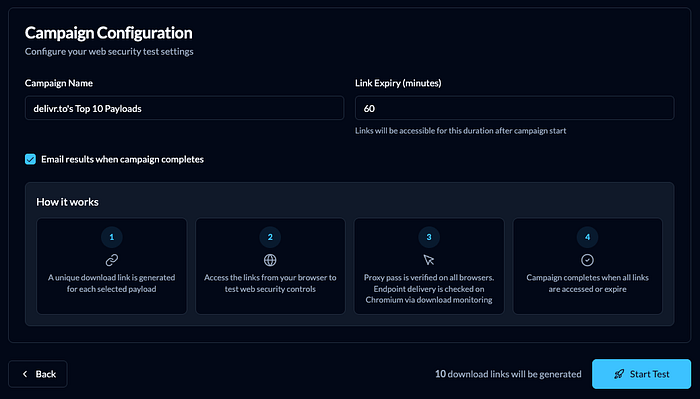
On launch, delivr.to generates a unique hosted download link for every selected payload. Links are reusable within the expiry window, allowing repeated testing against the same URLs. The campaign results page displays every payload with its corresponding download link, link expiry time, and access status.
Payloads can be downloaded or visited manually one-by-one by clicking the row buttons (e.g. visiting pastejacking sites or fake login portals), or by clicking 'Download All' to trigger the sequential background download of every payload.
This is where the security control chain is exercised. Each download traverses the full stack of web security controls deployed in your environment — the same path a real end user would follow when downloading a file from a malicious or compromised website.
Conclusion
Email remains the most common delivery vector for phishing, BEC, and malware distribution — and delivr.to's email campaign capabilities continue to expand. But the data increasingly shows that other initial access methods are coming to the fore.
Mandiant's M-Trends 2025 report recorded web compromise as an initial access vector in 9% of incidents, nearly doubling from 5% the prior year.
The techniques behind these numbers are well-documented. ClickFix — where a fake CAPTCHA or error prompt instructs a user to paste a clipboard-hijacked command into Run or Terminal — surged 517% in the first half of 2025 and was rapidly adopted by several nation-state groups. Its variants continue to evolve, where FileFix moved the interaction to the file explorer address bar, and our recent research into DragFix demonstrated how the HTML Drag and Drop API can smuggle commands via a completely separate data channel, bypassing clipboard monitoring altogether.
All of these techniques deliver a payload through the browser. Security teams that only test their email controls are testing half the attack surface.
Web campaigns are available now to all delivr.to users at their existing subscription tier, with no additional licensing required. Put your web security controls through their paces — you might be surprised what reaches disk!
delivr.to
delivr.to is a platform for validating email and web security controls, through the continuous and automated sending of email attachment and link content.
delivr.to has a broad collection of over 800 payload samples, ranging from recreations of threat actor activity, esoteric and weaponisable file formats, and emerging techniques. These are presented in hand-crafted 'campaigns' to provide an evidence-based appraisal of email and web defences and highlight areas for attack surface reduction.
delivr.to offers a free 30 day trial, so head over and try it out now!

