In today's digital-first world, organizations invest heavily in cybersecurity tools, frameworks, and teams. Firewalls, SIEMs, EDRs, vulnerability scanners — the stack keeps growing.
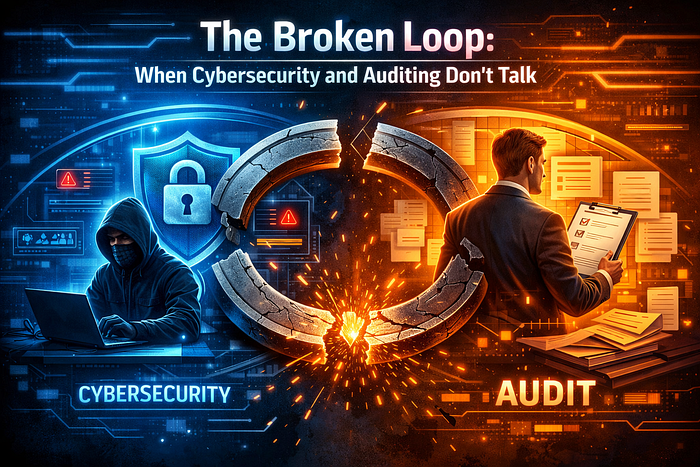
Yet breaches continue. Why?
Because most organizations are missing a critical truth:
Cybersecurity without audit is blind, and audit without cybersecurity is useless.
Security teams often operate on assumptions. Audit teams operate on checklists. And somewhere between the two — attackers thrive.
Hi , I'm Sumit Jain, a Cyber Security Specialist with experience in Ethical Hacking, Penetration Testing, and Security Training. I've trained students and actively share practical cybersecurity knowledge across LinkedIn, YouTube, and other platforms.This article breaks down the gap, the risks, real-world scenarios, and how to fix it.
Organizations today suffer from a disconnect between implementation and validation
- Security teams deploy controls but rarely validate their effectiveness continuously.
- Audit teams review policies and reports but often lack technical depth or real-world attack context.
This creates two dangerous conditions:
1. Blind Security
Security exists — but no one verifies if it actually works.
2. Hollow Audits
Audits are completed — but they don't reflect real attack surfaces.

→Understanding the Core Concept?
Cybersecurity = Defense Mechanism
- Firewalls
- Endpoint protection
- Access control
- Monitoring systems
Audit = Validation Mechanism
- Are controls working?
- Are policies followed?
- Are risks mitigated?
👉 Without audit → You assume you're secure 👉 Without cybersecurity → You document security that doesn't exist
Scenario 1 : We Have a Firewall , We're Secure
A company installs a next-gen firewall and believes it's protected.
Reality:
- Misconfigured rules allow outbound data exfiltration
- No audit is conducted on firewall logs or configurations
👉 Result: Sensitive data leaks silently
Scenario 2 : We Passed the Audit — Everything is Fine
An organization passes a compliance audit (ISO, SOC2, etc.)
Reality:
- Audit was checklist-based
- No penetration testing performed
- Weak authentication mechanisms still exist
👉 Result: Attacker bypasses login using simple credential stuffing
Scenario 3 : EDR Installed but Never Tested
A company deploys EDR across endpoints.
Reality:
- No red teaming or attack simulation
- Alerts are not monitored properly
👉 Result: Malware runs undetected despite "security tools"
Scenario 4 : Audit Reports Ignored
Internal audit identifies critical vulnerabilities.
Reality:
- No remediation tracking
- No accountability
👉 Result: Same vulnerability exploited months later
Why This Happens

The Missing Piece: Continuous Security Validation
Organizations must shift from Static Security to Continuous Security Testing
This includes:
- Vulnerability assessments
- Penetration testing
- Red teaming
- Attack simulations
- Continuous monitoring audits
Practical Solution Framework
1. Integrate Security + Audit
2. Adopt "Test Before Trust" Approach
3. Move Beyond Compliance
4. Implement Continuous Pentesting (VAPT)
5. Build Feedback Loop
Implement → Test → Audit → Fix → Retest → Monitor
Cybersecurity is not about tools. Audit is not about reports. It's about truth. If you don't test your defenses, you don't know them. If your audit doesn't reflect real attacks, it's irrelevant. The future of cybersecurity belongs to organizations that Continuously validate , break their own systems before attackers do , treat audit and security as one ecosystem.
Security without audit is assumption. Audit without security is illusion. Real security begins when both work together.
— Sumit Jain