Introduction: The Uncomfortable Truth Behind the "Almost Ready" Trap
Here's a story that plays out every single day in the bug bounty world.
Someone discovers ethical hacking, gets genuinely excited, and dives deep. They spend months going through online courses, watching tutorials, practicing on legal lab environments, taking notes, building what feels like a serious knowledge base. They tell themselves they're almost ready to start hunting on real programs. Just one more course. Just one more certification. Just one more technique to master.
Six months pass. They still haven't submitted a single report.
This is the Ultimate Bug Bounty Roadmap 2026 problem that nobody talks about openly — and it has almost nothing to do with technical skill.
Here's the myth sitting at the center of it all: "The more you learn before you start, the faster you'll succeed once you do." It sounds like wisdom. It feels like responsibility. But it's a trap dressed up as preparation.
The real issue isn't your technical knowledge. It's validation — specifically, the absence of real-world feedback that only comes from actually submitting reports, getting responses from triage teams, and iterating on what you learn. No course replicates that. No lab simulates it. The complete ethical hacking blueprint for 2026 begins with understanding that hunting and learning are not sequential. They're simultaneous.
The Ultimate Bug Bounty Roadmap 2026: What It Really Covers
Before diving in, let's establish what this roadmap is and what it isn't.
This isn't a list of tools to download or certifications to collect. It's a structured progression through four distinct stages — foundation, recon, hunting strategy, and report mastery — that build on each other in a deliberate sequence. Each stage produces tangible output, not just knowledge. By the time you complete stage two, you should be actively hunting. By stage three, you should have submitted real reports. By stage four, you should understand exactly what it takes to earn consistent payouts.
The roadmap is designed around a core principle: doing produces learning that studying can never replicate. That principle shapes every recommendation in it.
Why the Traditional Learning Path Sets You Up to Fail
The traditional learning path for ethical hacking is built around completeness. The assumption is that you need to know about every vulnerability class, every attack surface, every tool category before you're qualified to hunt. That assumption produces researchers who know a little about everything and earn nothing from any of it.
The 2026 reality is that bug bounty programs don't reward broad knowledge. They reward specific findings, clearly communicated, backed by reproducible evidence. A researcher who understands one vulnerability class deeply enough to find non-obvious instances of it will consistently outperform one with surface-level familiarity across twenty classes.
The traditional path is wide. The profitable path is deep. These are genuinely different directions.
The Ethical Hacking Mindset Nobody Teaches in Courses
Here's an intellectual insight that changes how you approach every hunt: ethical hacking at the pro level is fundamentally a creative discipline, not a technical checklist.
Pro hunters don't open a target and run through a mental list of vulnerability classes until something triggers. They develop a model of how the target works — its business purpose, its user workflows, its technical architecture — and then they reason about where the gaps between intended behavior and actual behavior might exist. That reasoning process is creative, contextual, and deeply specific to each target.
It can't be automated. It can't be learned from a course alone. It develops through repeated exposure to real targets, real feedback, and real iteration. That's why starting early — even imperfectly — is built into this roadmap from the beginning.
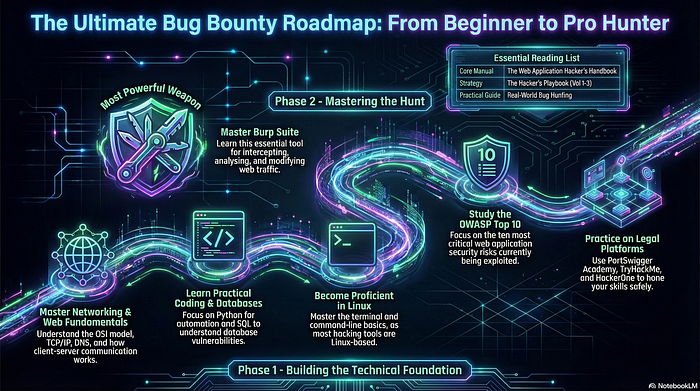
Stage One — Building the Right Foundation (Not Just Any Foundation)
Every pro hunter has a foundation. But the composition of that foundation matters as much as the depth of it. Spending months building knowledge in areas that don't directly translate to finding vulnerabilities on web application targets is a hidden time tax that beginners rarely account for.
Stage one of the Ultimate Bug Bounty Roadmap 2026 is about building a deliberately targeted foundation — one that prepares you specifically for the hunting you'll be doing in stages two and three, not for a theoretical exam or a comprehensive curriculum.
Web Application Security: Your Non-Negotiable Starting Point
Web applications remain the most accessible, most documented, and most rewarding starting point for anyone following the complete ethical hacking blueprint in 2026. The tooling ecosystem is mature. The learning resources are extensive. And the vast majority of bug bounty programs have significant web application scope that beginner hunters can legally test.
This means your foundational knowledge needs to cover how the web actually works at a functional, not just conceptual, level. HTTP methods, request and response structure, cookies and session tokens, how authentication flows operate, how data is passed between client and server — these aren't advanced topics. They're the grammar of every web vulnerability you'll ever find.
An original example worth considering: imagine a beginner who decides to specialize in understanding broken access control — the vulnerability class where users can access resources or perform actions they shouldn't be authorized for. They spend three focused weeks doing nothing but learning how access control is supposed to work in well-built applications, then studying how developers commonly get it wrong. That three-week investment, pointed at a specific class, produces more hunting-ready knowledge than three months of broad survey learning across every vulnerability category.
The Three Pillars Every Pro Hunter Knows Cold
Beyond the fundamentals of how the web works, there are three specific knowledge areas that appear in virtually every high-impact finding chain: authentication and session management, input validation and output encoding, and access control logic. These aren't the only areas that matter, but they're the ones where beginner investment yields the fastest practical return.
Know them well before you expand. Every hour of additional depth in these three pillars is more valuable than an hour of introductory breadth in a new domain.
Scripting Basics: When to Learn and When to Skip
There's a recurring debate in bug bounty communities about whether beginners need to learn scripting before they start hunting. The honest answer is: it depends, and for most beginners starting on web application targets, it can wait.
Basic Python or Bash scripting becomes genuinely useful when you need to automate repetitive recon tasks or customize a specific test. It's not necessary for your first several months of hunting. Don't let the absence of scripting skills become another reason to delay starting. Learn it when you have a specific, concrete use case — not as a prerequisite.
Stage Two — Recon Mastery and the AI Advantage
Reconnaissance is the process of mapping a target's attack surface before you begin active testing. Done well, it transforms a vague, overwhelming scope into a structured set of specific areas worth investigating. Done poorly — or skipped entirely — it leads to wasted hours testing the wrong things on the wrong assets.
The Art and Science of Target Intelligence
Pro-level recon isn't just running subdomain enumeration tools and compiling a list of URLs. It's building genuine intelligence about your target — understanding their technology stack, their deployment patterns, their recent development activity, and the parts of their infrastructure that are newest and therefore least battle-tested.
New features and recent deployments are consistently where the most accessible vulnerabilities live. A product team that shipped a major new workflow three weeks ago has had three weeks for their security review process to catch issues. A researcher who finds that new feature quickly and tests it thoroughly is working against a different competitive landscape than one hunting on a feature that's been live for two years and tested by hundreds of researchers.
Reading engineering blogs, monitoring public code repositories, tracking changelog entries — this kind of intelligence work is unglamorous and rarely discussed in tutorial content. It's also one of the clearest differentiators between hunters who find things and hunters who don't.
How AI Has Reshaped Reconnaissance in 2026
Artificial intelligence tooling has meaningfully changed what's possible in the recon phase of a hunt, and understanding this change is a core part of the complete ethical hacking blueprint for 2026.
AI-assisted analysis can process large volumes of JavaScript, configuration files, and API documentation in a fraction of the time it would take manually. It can surface potentially interesting patterns — exposed endpoints, unusual parameter names, references to internal systems — that might be buried in thousands of lines of code. For beginners, this compression of the analysis phase is a genuine advantage.
Here's the intellectual insight to hold alongside that: AI tools are good at pattern recognition and bad at contextual judgment. They can tell you that a parameter exists and that it resembles patterns associated with certain vulnerability classes. They cannot tell you whether testing that parameter in a specific way will violate the program's scope rules, or whether the business logic surrounding it makes the standard attack irrelevant.
The correct mental model is AI as a highly capable research assistant that needs direction and verification — not an autonomous hunter that can replace strategic human thinking. Hunters who develop that collaborative relationship with AI tooling will move faster than those who either ignore it or over-trust it.
Stage Three — Hunting Strategy: Where Pros Separate From Amateurs
Technical skill gets you to the door. Strategy determines whether you walk through it carrying something valuable.
Stage three is where the roadmap shifts from building capability to deploying it deliberately. The decisions you make at this stage — which programs to target, which vulnerability classes to focus on, how to structure your hunting sessions — have a larger impact on your outcomes than almost any technical improvement you can make.
Program Selection: The Decision That Determines Everything
Experienced hunters treat program selection as a strategic decision that deserves serious time and research. Beginners often treat it as an afterthought — picking whatever appears first or sounds most interesting.
The criteria worth evaluating before committing time to any program include the scope's breadth and clarity, the program's history of paying out valid findings, the responsiveness and quality of their triage communication, and the recency of significant changes to their product or infrastructure.
A well-structured approach to program selection looks like this: identify several programs that meet your criteria, spend time reading publicly available information about each one's history and vulnerability landscape, and then choose the one where your specific skill set and specialization creates the most opportunity. That's not a complicated process. It's just a deliberate one — and most beginners skip it entirely.
The Business Logic Edge: Finding What Scanners Can't
Business logic vulnerabilities deserve their own prominent place in any serious bug bounty roadmap. They represent one of the most consistently underexplored categories in modern programs, not because they're rare, but because they're invisible to automated tooling and require genuine understanding of the target's intended behavior to find.
A business logic flaw exists when the rules of a business process are implemented in a way that allows unintended outcomes. Consider a platform that allows users to schedule a resource for a specific time slot. A logic flaw might allow two users to simultaneously book the same slot through a race condition, or allow a user to cancel someone else's booking through a predictable identifier pattern. Neither of these would trigger any automated scanner. Both represent real, reportable vulnerabilities that programs reward.
Finding them requires reading the target's documentation carefully, mapping the intended user journey, identifying edge cases in that journey, and testing what happens when those edge cases interact with each other in unexpected ways. It's methodical, creative, and deeply manual work — which is precisely why it remains one of the clearest paths to high-value findings for hunters willing to invest the time.
Stage Four — From Finding to Payout: The Report Mastery Blueprint
Stage four is where the work you've done in stages one through three either converts into a payout or disappears into a triage queue never to be heard from again.
Report quality is not a soft skill. It's a technical discipline that determines your actual earnings. A valid finding with a poor report can be closed as informational, marked as a duplicate of a better-written submission, or simply deprioritized by an overwhelmed triage team. A valid finding with an excellent report gets fast triage, clear communication, and the best possible severity assessment.
The Five-Part Report Framework That Gets Fast Triage
Every high-quality vulnerability report answers five questions with precision and clarity.
First, what is the vulnerability — its technical classification and a plain-language description of the issue. Second, where does it exist — the exact URL, endpoint, parameter, or code path. Third, how do you reproduce it — numbered steps, specific inputs, expected versus actual behavior, with screenshots and HTTP captures where relevant. Fourth, what is the impact — articulated not just technically but in terms of the business risk it represents, the data it exposes, or the user harm it enables. Fifth, how should it be fixed — a suggested remediation direction, even a rough one, that demonstrates good faith and helps the engineering team act faster.
Hunters who internalize this framework and apply it consistently to every report they submit will build a reputation for quality that compounds over time. That reputation is worth more than any individual finding.
Building a Long-Term Reputation That Opens Private Programs
The bug bounty ecosystem runs on reputation. Programs track which researchers submit consistent signal. Platforms use quality metrics to determine which hunters receive private program invitations. Triage teams develop informal opinions about which researchers to prioritize based on past experience.
This reputation system works in your favor if you treat every report — including the low-severity ones, including the ones you're not confident about — as an opportunity to demonstrate professional standards. It works against you if you treat reports as rough communications that triage will figure out.
The hunters invited to the most exclusive private programs, which consistently offer better scope, less competition, and more responsive triage, are not necessarily the ones with the highest technical skill. They're the ones with the longest track record of professional, high-quality communication. Start building that track record on your first submission.
Frequently Asked Questions
Q1: What's the most realistic timeline for earning a first payout following this roadmap? With consistent, focused effort and the approach outlined here — specializing early, hunting while learning, and investing in report quality — many hunters can reach their first valid payout within three to nine months. The timeline compresses significantly for those who actively hunt on real programs rather than waiting until they feel fully prepared.
Q2: Do I need expensive tools or paid platforms to follow the Ultimate Bug Bounty Roadmap 2026? No. The most critical skills in this roadmap — strategic target selection, business logic analysis, and report writing — require no paid tools whatsoever. Free resources and free tiers of established platforms provide more than enough capability for beginners to make genuine progress. Paid tooling can enhance efficiency later but is never the bottleneck at the start.
Q3: Is it necessary to know programming to become a pro bug bounty hunter? Programming knowledge is useful but not a prerequisite for meaningful success, especially in web application security. Understanding how code works conceptually helps you identify vulnerabilities faster. Writing basic scripts helps you automate repetitive tasks. But the most important skills — adversarial reasoning, target research, and clear writing — are not coding skills.
Q4: How do I handle finding a vulnerability I don't fully understand yet? Report it anyway, with honest acknowledgment of what you observed and what you're uncertain about. A partially understood finding, honestly communicated, is better than a finding you hold back waiting until you fully understand it. Triage teams can work with incomplete information. They can't work with information you never submitted.
Q5: What's the difference between a bug bounty program and a vulnerability disclosure program? A bug bounty program offers monetary rewards for valid findings within a defined scope. A vulnerability disclosure program (VDP) provides a legal, structured channel for reporting vulnerabilities without a financial reward component. Both are legitimate and legally protected frameworks. For hunters focused on earnings, bug bounty programs are the relevant target. VDPs can be useful for building early experience and reputation without competitive pressure.
Q6: How should beginners handle duplicate findings — the most common early frustration? Duplicate findings are a normal part of bug bounty hunting, especially early on. Rather than treating them as failures, treat them as intelligence. A duplicate means the vulnerability was real and valid — the timing simply wasn't on your side. Study the disclosed version of the finding where possible to understand what the winning report looked like, and use that intelligence to refine both your hunting approach and your report quality.
Conclusion: The Roadmap Is Clear — The Choice Is Yours
The Ultimate Bug Bounty Roadmap 2026 is not a mystery. It's a deliberate progression through four stages — foundation, recon mastery, hunting strategy, and report excellence — each one building on the last and each one producing real output rather than abstract knowledge.
The complete ethical hacking blueprint laid out here challenges the most damaging myth in the beginner community: that preparation and action are separate phases. They're not. The most effective hunters in 2026 are those who learn while they hunt, who specialize before they generalize, who treat every report as a professional deliverable, and who understand that AI is a tool to be directed — not a replacement for adversarial thinking.
The roadmap is clear. The question was never whether a path exists from beginner to pro hunter. The question is whether you're willing to start walking it before you feel completely ready.
In 48 hours, I'll reveal the exact program-scoring checklist that pro hunters use before committing a single hour to any target — a five-minute exercise that most beginners skip and then spend months regretting.
If this roadmap gave you one insight you didn't have before, follow for weekly deep-dives into ethical hacking strategy that go beyond the surface. Share this with someone who's been "almost ready" for too long — it might be the nudge that changes everything.
💬 Comment Magnet: What's the one thing you believed about bug bounty hunting before you started that you now realize was completely holding you back?
Get Lifetime Access: Download Now