What Happened:
While testing a subdomain belonging to a major tech company, I found that sending a malformed `Authorization` header triggers an unhandled exception — and the server responds with a full Java stack trace exposed in the HTTP 500 response body.
One line was enough to reproduce it: curl -i -H "Authorization: Basic '" https://[REDACTED]/
What Gets Exposed:
The stack trace leaks more than just an error message. It reveals:
- Web server: Eclipse Jetty - Application framework: Axway SecureTransport 5.5 (with build number) - Operating system: AIX - Internal package structure: com.axway.st.server.httpd.* - Authentication handler class name and file line numbers - Session manager implementation
That's a full fingerprint of the stack in a single request.
Why This Matters:
Stack trace exposure is often dismissed as low severity, but in practice it's a meaningful reconnaissance primitive. Knowing the exact framework, version, and OS lets an attacker:
- Search for known CVEs specific to that version - Understand the internal architecture before attempting deeper exploitation - Craft more targeted payloads instead of spraying generic attacks
It's not a direct compromise — but it significantly reduces the attacker's effort.
Timeline:
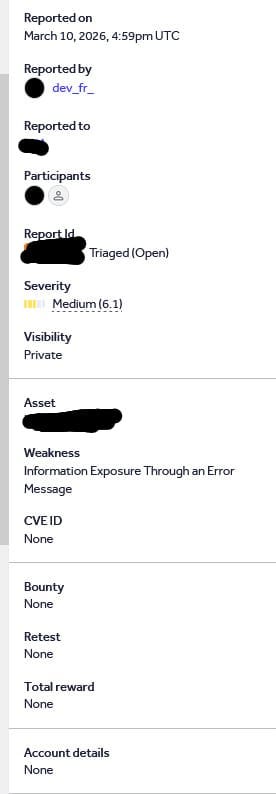
- Jan 2, 2026 — Reported - Jan 5, 2026— Triaged, then prematurely closed as Resolved - Jan 5, 2026— Retested and confirmed still vulnerable, commented with proof - Jan 6, 2026 — Reopened and moved back to Triaged - Feb 9, 2026 — The Company confirmed the team is actively working on a fix
Remediation:
- Return a generic error message like `Internal Server Error` — never a stack trace - Log detailed exceptions server-side only, never in the response body - Validate the `Authorization` header format before passing it to the authentication handler - Strip server version info from HTTP response headers - Disable debug mode in production environments
Reported: January 2026 — Currently open and under active remediation