The cybersecurity landscape in 2026 has been rocked by a series of high-impact incidents that expose a dangerous convergence: trusted software supply chains are being weaponized, while zero-day exploits are lowering the barrier for full system compromise. From compromised downloads of popular PC tools to the emergence of the BlueHammer Windows zero-day, attackers are increasingly targeting the very foundations users rely on for security and performance.
What is a Zero-Day?
A zero-day vulnerability is a security flaw that is unknown to the software vendor or has not yet been patched. The term "zero-day" means developers have had zero days to fix the issue before it is exploited.
Because there is no official patch or signature available, zero-day exploits are highly valuable to attackers. They can bypass traditional security defenses, spread rapidly, and are often used in targeted attacks, espionage, or ransomware campaigns. This is what makes threats like BlueHammer particularly dangerous — they operate in a window where defenders are essentially blind.
Supply Chain Attack: When Trusted Tools Turn Malicious
One of the most alarming incidents involved CPUID, the developer behind widely used tools like CPU-Z and HWMonitor. Attackers breached the company's infrastructure and, for roughly six hours, redirected legitimate downloads to malware-infected installers.
The attack was subtle but highly effective. Users visiting the official website unknowingly downloaded trojanized files disguised as legitimate software. These malicious installers were designed to steal browser credentials — especially from Google Chrome — while employing advanced evasion techniques to bypass antivirus detection.
Security researchers noted that the malware was multi-stage, operated largely in memory, and used file masquerading to appear legitimate — hallmarks of a sophisticated supply chain attack.
Although the breach was quickly resolved and original signed files remained intact, the incident highlights a growing trend: attackers are no longer just targeting users — they're targeting the software distribution channels themselves.
The Rise of BlueHammer: A Dangerous Windows Zero-Day
While the CPUID breach demonstrates supply chain risks, the BlueHammer vulnerability represents a deeper systemic threat. This Windows zero-day exploit allows attackers to escalate privileges from a normal user to full SYSTEM-level access — without needing administrative rights.
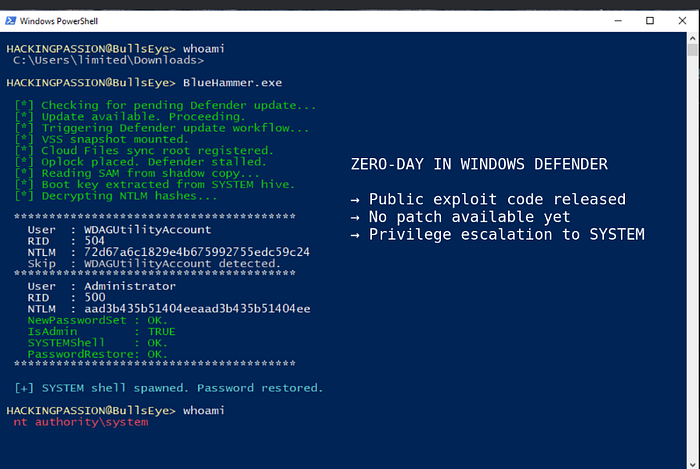
BlueHammer exploits a flaw in Microsoft Defender's update mechanism, combining race conditions and path confusion to access sensitive system files like the Security Account Manager (SAM) database.
What makes this vulnerability particularly dangerous is that:
- It is unpatched and publicly available
- It uses legitimate Windows features, making detection difficult
- It can be executed in under a minute once initial access is gained
Even more concerning, proof-of-concept code has already been released online, drastically lowering the barrier for attackers. Cybercriminal groups are known to weaponize such code within days, integrating it into ransomware and malware campaigns.
Why This Matters: From Initial Access to Full Compromise
Modern cyberattacks rarely rely on a single exploit. Instead, they chain multiple techniques:
- Initial Access — phishing or malware dropper
- Execution — user-level foothold
- Privilege Escalation — BlueHammer-style exploits
- Persistence & Exfiltration
BlueHammer is particularly dangerous because it bridges the gap between low-level access and full system control. Once SYSTEM privileges are achieved, attackers can:
- Dump credentials
- Disable security tools
- Establish persistent backdoors
This means even a minor breach — like opening a malicious file — can escalate into a complete system takeover.

Microsoft Defender: Protector and Potential Target
Ironically, BlueHammer weaponizes Microsoft Defender itself. By manipulating its update process, attackers can temporarily disable protections and access restricted resources.
However, in other cases — such as the CPUID breach — Defender successfully detected and blocked malicious installers, demonstrating its critical role in modern defense strategies.
This dual reality highlights a key lesson: security tools are powerful, but not infallible.
Key Takeaways for Users and Organizations
These incidents reinforce several critical cybersecurity principles:
- Never fully trust download sources — even official ones
- Verify file integrity and digital signatures
- Maintain updated endpoint protection
- Adopt layered security (defense-in-depth)
- Monitor for abnormal system behavior — not just malware signatures
As more businesses and individuals rely on digital tools, attackers will increasingly target widely used software ecosystems.
The events of 2026 signal a shift in cyber warfare tactics. Attackers are no longer just exploiting vulnerabilities — they are exploiting trust. Whether through compromised software downloads or unpatched zero-day exploits like BlueHammer, the message is clear: security must evolve beyond prevention to detection, response, and resilience.
In today's environment, even trusted tools can betray you — and a single vulnerability can open the door to total compromise.
Subscribe for exclusive breakdowns on cyber threats, tech policy, and business-infosec alignment.
Follow eL Njas!™
For a Newsletter
Subscribe 👉sign_in
