The Recon
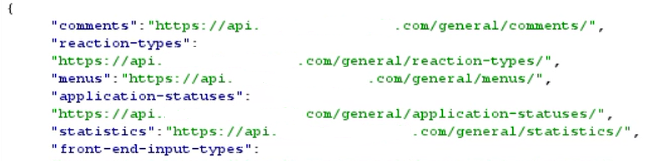
While I was browsing the website I started checking the API requests in the background. Suddenly the GET /general/ HTTP/2 endpoint caught my attention. When I went to this endpoint I found a list of other available endpoints in the application.
In this list the comments endpoint looked interesting. When I accessed this endpoint I saw something very surprising. The system was listing all the comments that were "Pending Approval". These are comments that normally only editors should see before they are published. Even though I was just a regular user I could see all of this private content.
Exploitation
When I saw the pending comments some questions came to my mind. Can I edit these comments, delete them, or maybe even approve them by myself ? While I was checking I noticed that every comment has a specific ID. When I changed the endpoint to GET /general/comments/{id}/ I saw that it only brings that specific comment.
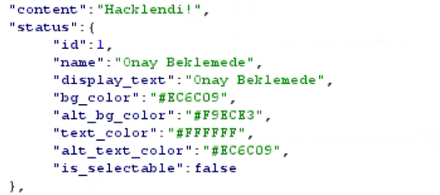
After that I wanted to try changing the comment content. I changed the request method to PATCH and added this to the body:
{ "content": "Hacklendi !" }
I sent the request and the answer was 200 OK. The comment was changed.
Then I wanted to check if I can delete it too. I edited the request again with the DELETE method and boom!

The answer was 204 No Content. When I sent the GET /general/comments/ request again to check the list I saw that the comment was gone.
After I did these I thought about if I can approve the comments too. Then I remembered an endpoint I saw before:GET /general/application-statuses/
I went to this endpoint and it showed what the status codes mean. In the response I saw that status: 2 means "Approved". So I edited the request and sent it. The result was 200 OK but in the response the status was still 1. So this part was secure.
Impact
With this vulnerability a malicious person could access all the unapproved comments in the system. Not just reading them they could change other people's comments however they want or delete all of them at once.Just imagine someone shares a post on your site and I can delete hundreds of pending comments with one move or I can change the content to mislead people. In other words the comment mechanism of the system was completely under my control.
Conclusion
In short the main reason for this vulnerability was that the system only checks if the user is logged in but doesn't verify if the user owns that specific comment. There was a lack of "Object Level Authorization."
I reported this finding to the system owners in a responsible way.
Thanks for reading…