We often think of end-to-end encryption (E2EE) as an impenetrable shield for our private conversations. But what if the very mechanisms that make messaging convenient — like a read receipt or a reaction emoji — could be weaponized to track your every move, drain your phone's battery, and fingerprint your devices, all without you ever knowing?
This isn't science fiction. It's real. And it affects over 3 billion people.
The Scale of the Problem
WhatsApp alone serves over 3 billion users globally, handling billions of messages daily. These platforms aren't just for casual chats — they're used by high-profile government officials for sensitive conversations. The 2025 "Signalgate" incident and Austria's "Beidlgate" affair prove that the people making decisions about our world rely on these same apps.
At DEF CON 33, security researchers Gabriel Gegenhuber and Maximilian Günther presented their research on "Careless Whisper," revealing two significant vulnerabilities in the world's most popular messaging apps: WhatsApp and Signal.
Their finding? Just by using a simple "❤️", your life becomes an open book.
The Vulnerability: Silent Delivery Receipts
The core issue lies with delivery receipts — those silent acknowledgments that confirm a message has reached its target. Unlike "read receipts," which you can disable in settings, delivery receipts are fundamental to how E2EE protocols manage keys and forward secrecy. They cannot be turned off.
The researchers discovered that by sending a reaction to a non-existent message (or using a self-reaction or message deletion packet), they could trigger these delivery receipts without the target ever receiving a notification. It's a completely silent ping — a digital heartbeat the victim never feels.
And here's the kicker: You don't need to be friends with the victim. Just knowing their phone number is enough to start probing them on WhatsApp and Signal.
As the paper states: "This design decision… can have a significant impact on the privacy as well as the security of users."
What a Silent Ping Reveals
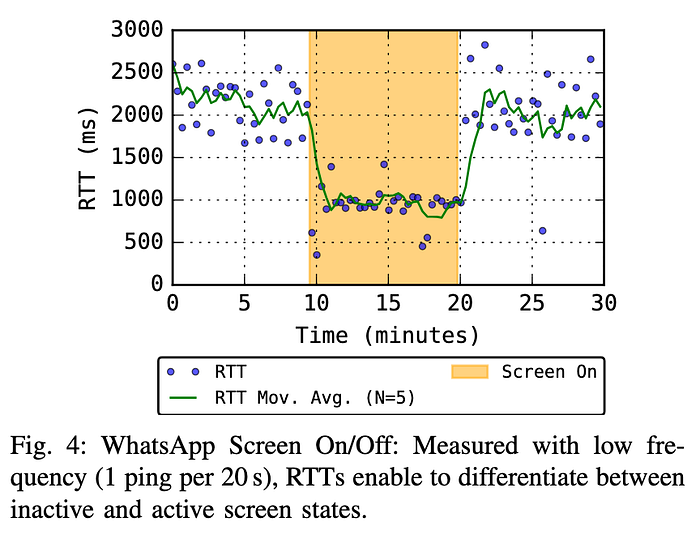
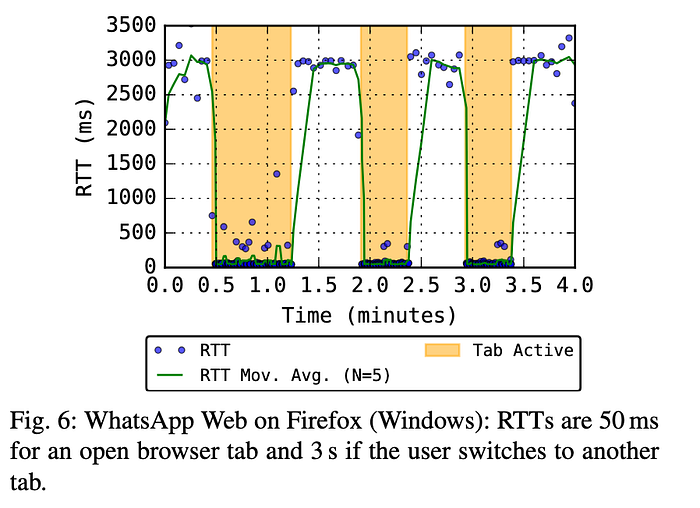
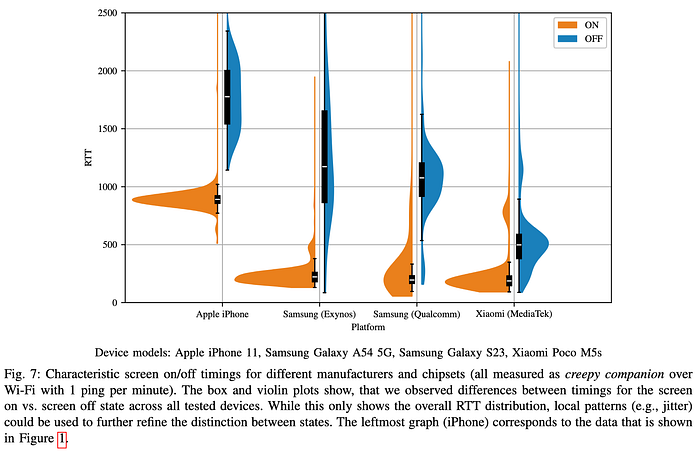
Once you can silently ping a device, the real surveillance begins. By analyzing the round-trip time (RTT) of these receipt packets, an attacker can infer incredibly detailed information about the victim's state:
Screen On/Off: The phone's processor sleep state causes measurable delays. An attacker can tell when you're actively using your phone and when it's sitting idle on the table.
App in Use: Is the messaging app itself in the foreground? RTTs drop dramatically (e.g., from ~1000ms to ~300ms on an iPhone), allowing precise tracking of when you're actively chatting.
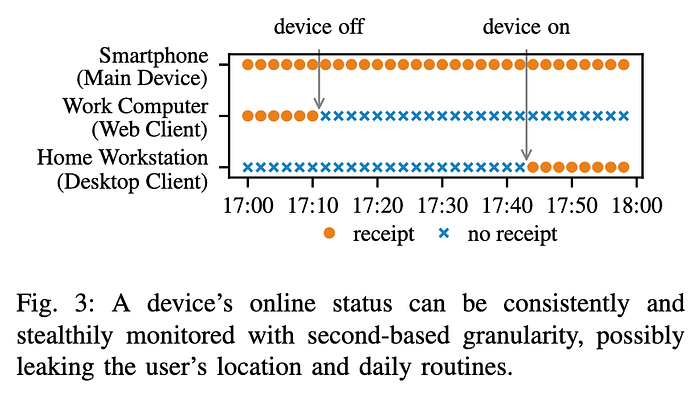
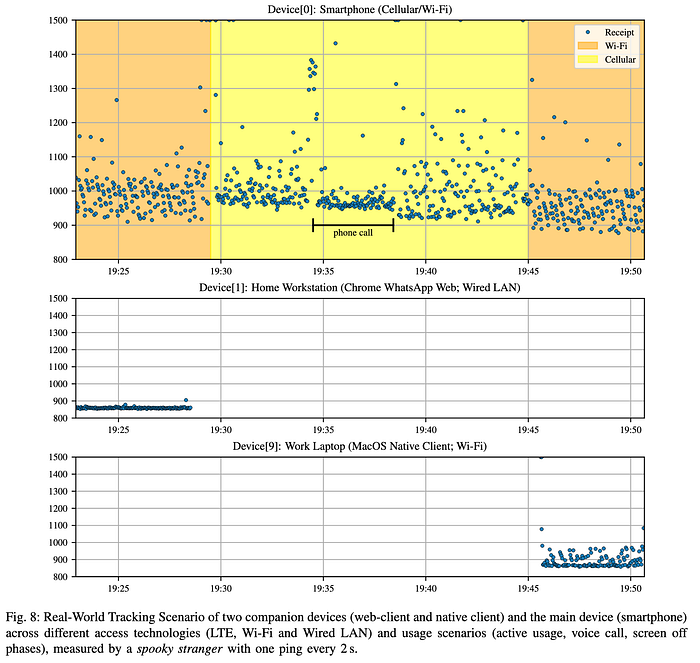
Companion Device Tracking: In multi-device setups, every device (phone, desktop, web client) sends its own independent delivery receipt. The researchers demonstrated this by tracking a volunteer:
- Leaving home (desktop goes offline)
- Walking to the office (phone switches from Wi-Fi to LTE)
- Turning on their work laptop (a new device comes online and acknowledges all backlogged pings)
They could even fingerprint the operating system based on the order of these receipts.

Beyond Tracking: Resource Exhaustion
The probing itself consumes resources, but the researchers found a way to amplify this dramatically. WhatsApp allows message reactions to carry up to 1 MB of payload data.
Data Drain: By blasting a victim with 1MB reaction packets, an attacker could consume 13.3 GB of data per hour — potentially incurring massive overage charges or simply clogging the victim's connection.
Battery Drain: Tests showed this bombardment could drain a phone's battery 14–18% per hour, even while the screen was off.
Breaking Forward Secrecy: WhatsApp's implementation of the Signal Protocol requires a stash of "prekeys" on the server for new sessions. By exhausting a victim's data plan or keeping their device busy, an attacker can force their client to fail at refilling this key stash. This can prevent message delivery and potentially weaken encryption guarantees.
Who is at Risk?
Literally everyone with WhatsApp or Signal installed. With WhatsApp alone serving over 3 billion users, the potential for abuse is staggering:
Stalkers and Abusers: To monitor a partner's activity, screen time, and location with frightening precision.
Corporate Espionage: To track the routines and devices of a competitor's CEO.
State-Level Actors: To monitor journalists, dissidents, or government officials.
The Bottom Line
End-to-end encryption promises privacy, but this research shows that promise is incomplete. Until messaging apps redesign how delivery receipts work, your phone number is all someone needs to turn your device into a silent spy.
The convenience of reactions and read receipts comes at a cost — one that 3 billion users are unknowingly paying.
Share this. Talk about it. The first step to fixing a problem is knowing it exists.
What do you think — should WhatsApp and Signal disable reactions from unknown numbers? Drop your thoughts in the comments.
For more information: