From a late-night idea to a production-ready security tool featuring 27 MITRE ATT&CK techniques.
We've all been there. You're staring at a vulnerability report with hundreds of "High" or "Critical" flags, wondering which ones actually matter.
Most organizations rely heavily on vulnerability scanners that simply check for known CVEs. They are great at telling you, "Port 443 is open," or "Your software is three versions behind." But they fail to answer the questions that actually keep Chief Information Security Officers (CISOs) awake at night:
- How would an attacker actually string these vulnerabilities together?
- What would our security operations center (SOC) miss during an active breach?
- How much damage (and financial loss) could we actually face?
- What specific system should we patch today to stop a nation-state threat?
I realized that to answer these questions, organizations don't need another scanner. They need an adversary. So, I decided to build one.
Here is the story of how I built an Advanced Persistent Threat (APT) Emulation Platform from scratch.
The Solution: Emulating the Adversary
I set out to build a platform capable of mimicking real APT groups — the exact same threat actors that target governments, financial institutions, and critical infrastructure.
By mapping the project directly to the MITRE ATT&CK framework, I ensured the tool wasn't just throwing random exploits, but executing calculated, realistic campaign sequences.
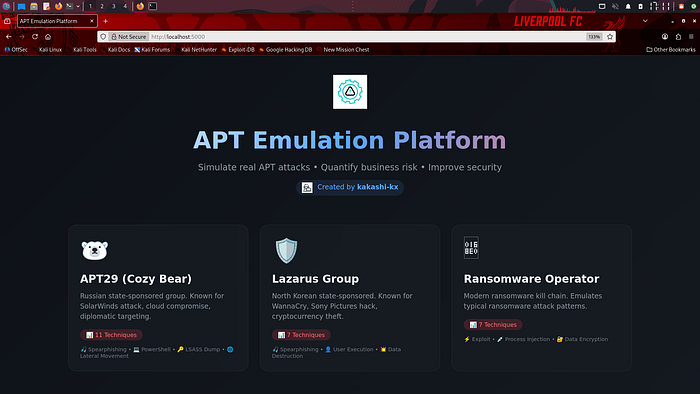
The Threat Profiles
Currently, the platform supports three major threat profiles:
- APT29 (Cozy Bear): Russian state-sponsored actors (infamous for the SolarWinds attack). Maps to 11 specific MITRE techniques.
- Lazarus Group: North Korean state-sponsored actors (WannaCry, Sony hack). Maps to 8 specific MITRE techniques.
- Modern Ransomware Operators: Simulates a standard ransomware kill chain using 8 MITRE techniques.
To give you an idea of how this looks in the code, here is how I defined a credential access technique:
# Sample technique: Credential Access via LSASS Dump
Technique(
id="T1003.001",
name="LSASS Memory Dump",
tactic="Credential Access",
description="Dump LSASS to extract credentials",
detection_risk=0.8,
command="procdump.exe -ma lsass.exe"
)Under the Hood: The Architecture
When building security tools, modularity is everything. You want to be able to swap out payloads, add new APT groups, and update techniques without breaking the core engine.
Here is a look at the project structure:
apt-emulation-platform/
├── web/ # Flask web interface
├── apt_profiles/ # APT group definitions
│ ├── apt29.py # 11 techniques
│ ├── lazarus.py # 8 techniques
│ └── ransomware.py # 8 techniques
├── core/ # Emulation engine
├── emulation_engine/ # Campaign manager
├── reporting/ # Report generator
└── utils/ # Logging & helpersThe execution flow itself is designed to be straightforward but highly effective. The engine iterates through the defined attack sequence, attempts the technique, checks if the local defenses detected it, and logs the outcome before generating a comprehensive report.
Making Security Accessible: The Web UI
A major flaw with many powerful open-source security tools is that they require a Ph.D. in terminal commands just to run a basic test. I wanted this platform to be accessible to analysts, managers, and red teamers alike.
I built a modern web interface using Flask.
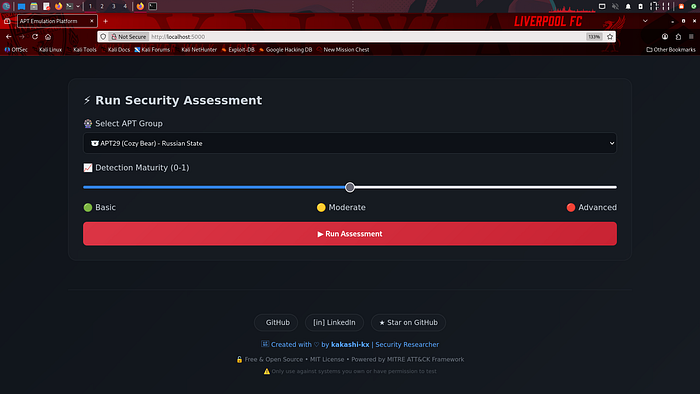
With the UI, running a campaign is as simple as:
- Selecting your target APT group.
- Adjusting your assumed detection maturity (Basic to Advanced).
- Clicking "Run Assessment".
The platform provides real-time execution tracking, showing you exactly which techniques succeeded, which failed, and crucially, which ones slipped past your simulated defenses.
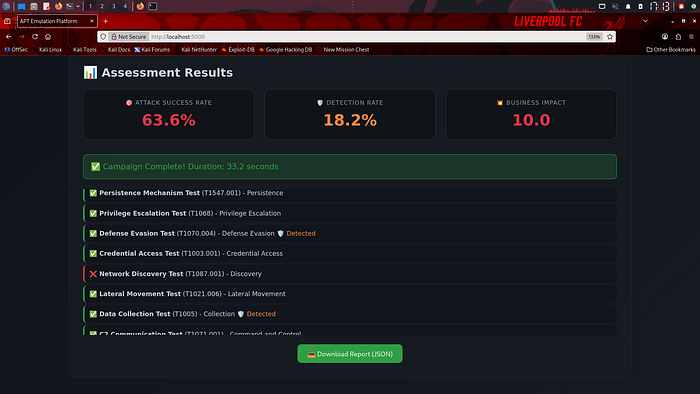
[📸 Insert Screenshot Here: Results Display showing the success rates and business impact score]
The Reality Check: Testing a Simulated Environment
To see what the platform could do, I tested it against a simulated financial services environment. The results were a massive wake-up call.
┌──────────────────────────────────────────────┐
│ APT29 63.6% Success | 27.3% Detection │
│ Lazarus 87.5% Success | 62.5% Detection │
│ Ransomware 100% Success | 75.0% Detection │
│ │
│ Business Impact: $25-50M | Score: 10/10 │
└──────────────────────────────────────────────┘What does this actually mean?
- Complete Compromise: With a 63.6% success rate for APT29, the simulated company would have been fully compromised.
- Massive Blind Spots: Only 27.3% of those techniques triggered a detection. The attackers were essentially moving like ghosts.
- Translated Risk: By calculating a potential $25–50M business impact, the report translates technical jargon into a language the board actually understands.
Lessons Learned: What I'd Do Differently Next Time
Building this wasn't entirely smooth sailing. If you are looking to build your own security tooling, learn from my mistakes:
- Map to MITRE First: I spent way too much time building out the infrastructure before I actually mapped the techniques. Next time, the technique mapping comes first, the code comes second.
- Configurations Over Hardcoding: The
user_config.yaml.examplewas a late addition. Implementing user configs earlier would have saved me hours of refactoring. - Perfect the CLI Before the GUI: The command-line version was perfectly sufficient for testing. I let myself get distracted by building the Flask interface before the core engine was 100% flawless.
- Log Everything: Debugging a failed emulation sequence without granular logs is incredibly painful. Build robust logging from day one.
The Road Ahead
This platform is a living project, and I have big plans for it.
Short-term (Next 1–2 months):
- Integrate profiles for APT28 (Fancy Bear) and APT41.
- Enhance detection simulation using basic Machine Learning models.
- Build out automated PDF report exporting.
Long-term (Next 3–6 months):
- Containerize the platform with Docker for one-click deployment.
- Build CI/CD pipelines for automated testing.
- Create native integrations with popular SIEMs like Splunk and Elastic.
Why This Matters
We need to stop evaluating our security posture based strictly on compliance checklists and theoretical vulnerabilities. Tools like this help organizations find real gaps, quantify their risk in actual dollars, justify security budgets with hard data, and train SOC analysts against realistic, actionable scenarios.
I've made the platform entirely open-source. I'd love for you to try it, break it, and help me improve it.
👉 Check out the project on GitHub: APT Emulation Platform
# Quick start
git clone https://github.com/kakashi-kx/apt-emulation-platform.git
cd apt-emulation-platform
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
python3 web/app.pyLet's connect! I'm actively looking for opportunities in cybersecurity, red teaming, and tool development. You can find me on GitHub or reach out on LinkedIn.
If you found this breakdown helpful, give it a clap 👏 and share it with your network!


