CVE-2019–18634 is, at the time of writing, the latest offering from Joe Vennix — the same guy who brought us the security bypass vulnerability that we used in the Security Bypass room. This one is slightly more technical, using a Buffer Overflow attack to get root permissions. It has been patched, but affects versions of sudo earlier than 1.8.26.
Here's the catch. When this option is turned on, it's possible to perform a buffer overflow attack on the sudo command. To explain it really simply, when a program accepts input from a user it stores the data in a set size of storage space. A buffer overflow attack is when you enter so much data into the input that it spills out of this storage space and into the next "box," overwriting the data in it. As far as we're concerned, this means if we fill the password box of the sudo command up with a lot of garbage, we can inject our own stuff in at the end. This could mean that we get a shell as root! This exploit works regardless of whether we have any sudo permissions to begin with, unlike in CVE-2019–14287 where we had to have a very specific set of permissions in the first place.
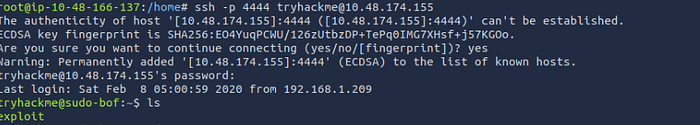
lets explore the vulnerability and try to find out the flag. First we have to login via SSH using port 4444. Let's start:
we are in the SSH, so lets enumerate a little; to find out the flag we are asked to find out in question number 2 in task 2:
| What's the flag in /root/root.txt?
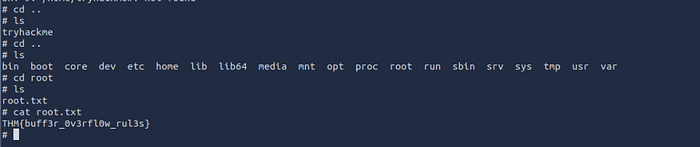
Okay, it was so easy! Try it out yourself now on TryHackMe, its real fun!