Hacking Hub Challenge -VulnBegin
Introduction :
Hello everyone if you are new in hacking hub platform so start with this ctf, it is easy and beginner friendly ctf with 9 Flags.
before you start ctf first download some tools and wordlist like :
DNS information = https://github.com/projectdiscovery/dnsx
Subdomain enumeration = https://github.com/projectdiscovery/subfinder
ffuf = https://github.com/ffuf/ffuf
Wordlist = https://app.hackinghub.io/wordlists.zip
after done this open and start hub https://app.hackinghub.io/hubs/vuln-begin
Flag 1 :
For The hacking hub challenge i use dnsx tool

in this lab i face some DNS problem because but after some reaserch i found Flag [^FLAG^BED649C4DB2DF265BD29419C13D82117^FLAG^] flag available in TXT record.
Flag 2 :
after check dns record next i find subdomain with subfinder

i found 3 subdomain with name server,v64hss83,ggmjael1 and i check one by one with curl, this vulnbegin.co.uk are osint domain so check subdomain in main site.
curl https://ggmjael1.phosphorus.ctfio.com [not open] so try v64hss83 curl https://ggmjael1.phosphorus.ctfio.com and now second flag here [^FLAG⁰⁴⁷⁵²⁴FE61AE6B5FD1D184994C7322FC^FLAG^]
Flag 3 :
Next i check last subdomain server phosphorus
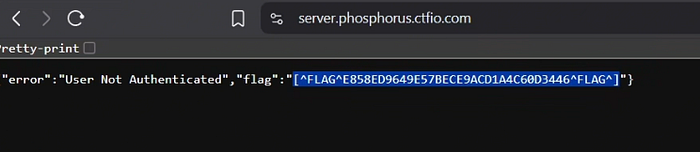
in this subdomain see Error user not authenticated means i need cookie or header so check later.
Flag 4 :
First check main domain,
in this page i nothing found interesting so i check source code and in source code no comment and no extra links available, so next i fuzz endpoint with ffuf [ffuf -u https://phosphorus.ctfio.com/FUZZ -w content.txt ] and found robots.txt, cpadmin, css and js.
so first i check https://phosphorus.ctfio.com/robots.txt
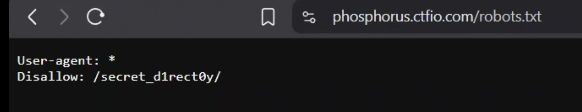
found new endpoint so check https://phosphorus.ctfio.com/secret_d1rect0ry and flag 4 here [^FLAG²B22E2CB70E218510802B0359488F6A2^FLAG^]
Flag 5 :
next check last endpoint cpadmin the cpadmin redirect to the login page [https://phosphorus.ctfio.com/cpadmin/login]

i try random username, password and see this is give me only username is invalid error it's mean first they verify username after verify password so i don't have username and password that's why i brute force username with burp suit (send request in intruder, select username add password list in payload , go settings add username is invalid in auto pause attack and start) for password same but remove auto-pause [username = admin & password = 159753 ]
after login with username and password and see flag 5 [^FLAG⁹³D7491FB4B054FB5C5AC3E0292BE41C^FLAG^]
Flag 6 :
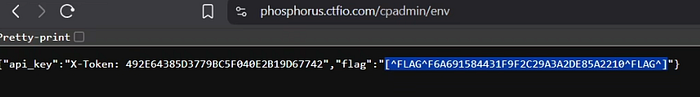
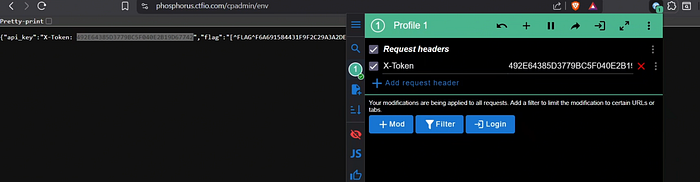
now i am authenticated user so see more endpoint with ffuf and i found login, logout, env and flag 6 available in here.
ffuf -u https://phosphorus.ctfio.com/cpadmin/FUZZ -w content.txt -H "Cookie:token=value" (-H for Header)
Flag 7 :
after see /env endpoint i found X-Token (X-Token is header). for header i use mod header extension [ https://chromewebstore.google.com/detail/modheader-modify-http-hea/idgpnmonknjnojddfkpgkljpfnnfcklj?hl=en ]
i have x-token but this token for which user and after see domains i need authentication in server domain so add header and refresh.
now i authenticated and get 7 flag [^FLAG^BDC60CC5E283476E7107C814C18DCCF^FLAG^]
Flag 8 :
next find server domain endpoints with ffuf and i found user
ffuf -u https://server.phosphorus.ctfio.com/FUZZ -w content.txt -H "X-Token:value" (-H for Header)
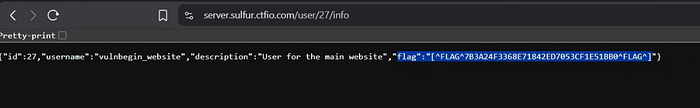
in user endpoint available /27/info endpoint so i check and i get 8 flag.
Flag 9 :
see endpoint /27/info (27 is id) so i fuzz ids (may be IDOR bug work) and i found 27,5 id. so i check id 5 and i get 9 flag.
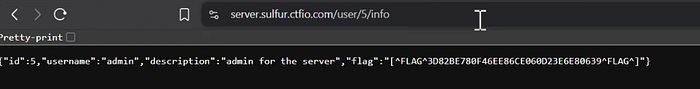
IDOR = Insecure direct object references (IDOR) are a type of access control vulnerability that arises when an application uses user-supplied input to access objects directly. (view other users data without permission).

