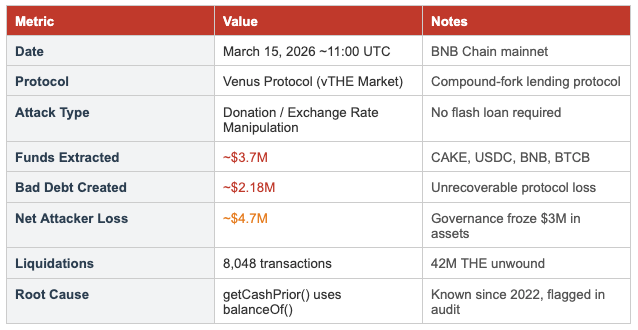
Executive Summary
On March 15, 2026, the Venus Protocol THE (Thena) market on BNB Chain was drained of approximately $3.7 million through a donation attack, a well-documented vulnerability class in Compound-forked lending protocols. The attacker exploited a single root-cause flaw in the getCashPrior() function, which reads the contract's underlying token balance via ERC-20 balanceOf() rather than an internal accounting variable. By transferring tokens directly to the vTHE contract address while bypassing the mint() function, the attacker inflated the vTHE exchange rate 3.81x, enabling them to borrow assets far exceeding the legitimate value of their collateral.
The attack left Venus Protocol with approximately $2.18 million in unrecoverable bad debt. The attacker ultimately suffered a net loss of approximately $4.7 million after the Venus community passed an emergency governance proposal to freeze $3 million in attacker-controlled assets.
This vulnerability was not new. It had been flagged in a Code4rena security audit and the Venus team declined remediation, stating that donations were an intentional feature with no negative side effects. Olympix's BugPoCer tool, run against the Venus Protocol repository on the morning of the attack, identified all three vulnerability dimensions with verified proof-of-concept exploits, confirming that automated pre-deployment detection was entirely feasible.
Background
Venus Protocol
Venus Protocol is a Compound-forked money market deployed on BNB Chain. Like Compound, it uses a cToken architecture where users deposit underlying assets to receive vTokens representing their share of the pool. The exchange rate between vTokens and underlying assets increases over time as interest accrues. The protocol supports isolated markets, supply caps, and a Comptroller contract for cross-market risk management.
THE (Thena) Token
THE is the governance token of Thena, a DEX/AMM protocol on BNB Chain. It has relatively thin on-chain liquidity compared to major assets, making it susceptible to price manipulation. The Venus THE market had a governance-set supply cap of 14.5 million THE tokens, intended to limit the protocol's concentration risk in this illiquid asset.
The Donation Attack Vector
Donation attacks against Compound-forked protocols have been documented since 2022. The attack exploits the fact that many Compound forks compute market cash, a key input to the exchange rate formula, by reading the raw ERC-20 balance of the vToken contract. Because anyone can transfer tokens to any address, an attacker can donate tokens to the vToken contract, inflating the reported cash balance without minting any vTokens. This directly inflates the exchange rate:
Exchange Rate = (totalCash + totalBorrows — totalReserves) / totalSupply
When totalCash is artificially inflated via donation, any holder of existing vTokens sees their redeemable underlying value increase and, critically, so does the collateral value the Comptroller assigns to their position.
Attack Timeline

Technical Analysis
Root Cause: getCashPrior() Uses balanceOf()
The vulnerability originates in VBep20.sol:
// VULNERABLE - VBep20.solfunction getCashPrior() internal view override returns (uint) { return EIP20Interface(underlying).balanceOf(address(this));}By reading balanceOf(address(this)), any tokens sent directly to the contract without going through mint() are immediately and silently incorporated into the exchange rate calculation. The patched version uses an internal state variable:
// FIXED - uses internalCash state variablefunction getCashPrior() internal view override returns (uint) { return internalCash; // only modified by mint/redeem/borrow/repay/liquidate}Exchange Rate Inflation Mechanics
With getCashPrior() returning balanceOf(), the attack proceeds as follows:
- The attacker supplies tokens normally through mint() to receive vTokens, establishing a legitimate position with real vTHE holdings
- The attacker transfers 28,100+ THE tokens directly to the vTHE contract address via ERC-20 transfer(), bypassing mint()
- getCashPrior() immediately reflects the inflated balance, increasing totalCash with no change to totalSupply
- The exchange rate inflates from $0.263 to $0.51 (a 3.81x multiplier), amplifying the attacker's vTHE collateral value proportionally
- The Comptroller uses this inflated exchange rate to compute collateral value, granting the attacker borrow capacity far exceeding their legitimate deposit
The attack is compoundable: each borrow cycle provides assets that can be swapped for more THE on DEXs, donated back to vTHE, and used to unlock further borrowing power. Over multiple cycles, the attacker extracted approx. $3.7M in CAKE, USDC, BNB, and BTCB.
Supply Cap Bypass
Venus governance had set a supply cap of 14.5 million THE tokens for the vTHE market to limit concentration in a single illiquid asset. However, the Comptroller's supply cap check operates against totalSupply of vTokens (which only changes through mint()), while the economic exposure operates through getCashPrior() (which reads balanceOf()). The two were decoupled.
Through the compounding donation loop, the protocol's effective THE exposure reached 53.23 million tokens, which is 367% of the 14.5 million supply cap. The governance-set risk parameter provided no protection against the attack.
Interest Rate Distortion
A secondary impact is the distortion of the interest rate model. The accrueInterest() function calls getCashPrior() to compute the utilization rate:
Utilization = totalBorrows / (totalCash + totalBorrows)
When totalCash is inflated by donations, utilization appears lower than it truly is, causing the interest rate model to charge lower borrow rates. During the attack, this also affected reserve accumulation: accrueInterest() independently calls getCashPrior() for reserve management logic, meaning donated tokens can accelerate reserve consumption beyond governance-intended thresholds.
Oracle Feedback Loop
The attack was further amplified by an oracle feedback loop. THE has thin on-chain liquidity; the attacker's large borrow-and-sell operations pushed spot prices on DEXs, which fed into Venus's oracle and temporarily sustained an elevated THE price (peaking at approx. $0.56) even as the attack progressed. This delayed premature liquidation and allowed additional borrowing cycles before the health factor collapsed.
Olympix Findings
Olympix's BugPoCer tool scanned the Venus Protocol repository (commit 4f8a2c1) on March 15, 2026 and identified three true-positive vulnerabilities, all sharing the same root cause in getCashPrior(). Each finding included a verified, executable proof-of-concept demonstrating real exploitability. All three were confirmed as True Positives.
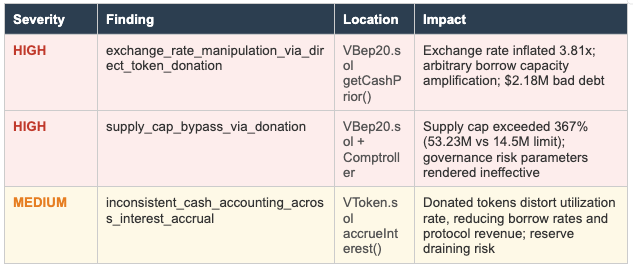
Finding 1 (High): exchange_rate_manipulation_via_direct_token_donation
Location
contracts/Tokens/VTokens/VBep20.sol — VBep20.getCashPrior() function
Description
The getCashPrior() function reads the underlying token balance via EIP20Interface(underlying).balanceOf(address(this)) rather than tracking deposits through an internal accounting variable. Tokens sent directly to the vToken contract, bypassing mint(), are immediately counted as protocol cash in the exchange rate calculation.
The exchange rate formula uses getCashPrior() as the totalCash input. An attacker who holds vTokens can donate arbitrary amounts of underlying tokens, inflating totalCash without affecting totalSupply, thereby increasing the exchange rate and the collateral value of their vToken position.
Proof of Concept Results
File: test/poc/VBep20_exchange_rate_manipulation_via_direct_token_donation.t.sol
- Attacker supplies 10,000 THE through mint(), receives vTokens
- Attacker donates 28,100 THE directly via ERC20.transfer()
- Exchange rate inflates from 1.0 to 3.81
- Borrow capacity jumps from 7,500 USDT to 28,575 USDT (3.81x amplification, creating 21,075 USDT in bad debt)
- Fixed version using internalCash: same donation has zero effect on exchange rate
- Compounded loop test over 3 rounds: 28,828 USDT in bad debt from 7,500 USDT of legitimate collateral
Prior Context
This vulnerability was flagged in a Code4rena security audit. The Venus team declined remediation, stating donations were an intentional feature with no negative side effects. The BNB Chain deployment remained unpatched at the time of the March 2026 attack.
Finding 2 (High): supply_cap_bypass_via_donation
Location
contracts/Tokens/VTokens/VBep20.sol — VBep20.getCashPrior() function; Comptroller supply cap check
Description
The Comptroller's supply cap mechanism compares against totalSupply of vTokens, which is only modified by mint(). Because getCashPrior() reads balanceOf(), direct token donations inflate the protocol's actual underlying exposure without triggering the supply cap check. This creates a fundamental mismatch between the protocol's internal supply accounting and its real economic exposure.
In the March 2026 incident, the Venus THE market had a governance-set supply cap of 14.5M THE tokens. Through the donation loop, effective economic exposure reached 53.23M THE (367% of cap) with the supply cap providing no protection.
Proof of Concept Results
File: test/poc/VBep20_supply_cap_bypass_via_donation.t.sol
- MockComptroller enforcing 14.5M THE supply cap deployed
- mint() correctly reverts above the cap: supply cap works as intended for normal deposits
- Direct token donation of 38.73M THE inflates totalSupplyUnderlying() to 53.23M (367% of cap) without triggering the supply cap
- Protocol is massively overexposed to a single illiquid asset while governance believes the cap is enforced
Finding 3 (Medium): inconsistent_cash_accounting_across_interest_accrual
Location
contracts/Tokens/VTokens/VToken.sol — VToken.accrueInterest() function
Description
The accrueInterest() function calls _getCashPriorWithFlashLoan(), which internally calls getCashPrior(). When getCashPrior() reads balanceOf(), donated tokens are included in the cash calculation used for interest rate model inputs. This distorts the utilization rate, producing an artificially low figure and causing the interest rate model to charge lower borrow rates.
Additionally, a reserve reduction path at the end of accrueInterest() independently calls getCashPrior() via actualCash = getCashPrior(). Inflated values here may reduce reserves faster than governance intended.
Proof of Concept Results
File: test/poc/VToken_inconsistent_cash_accounting_across_interest_accrual.t.sol
- Baseline: 50% utilization (50k cash, 50k borrows), borrow rate is 12%
- After 150k donation: getCashPrior() returns 200k, utilization drops to 20%, borrow rate halves to 6%
- Interest accrued over 100 blocks with vs. without donation: measurably less interest and fewer reserves accumulate
- Direct, quantifiable protocol revenue loss confirmed
How Olympix Could Have Prevented the Exploit
The March 15 exploit was entirely preventable. Every vulnerability dimension exploited by the attacker was identified by Olympix's BugPoCer tool with verified proof-of-concept exploits. Had Olympix been integrated into the Venus Protocol development and deployment workflow, the following prevention pathways would have been available:
Pre-Deployment Detection via BugPoCer
Olympix's BugPoCer performs automated vulnerability scanning and proof-of-concept generation against smart contract repositories. The scan of commit 4f8a2c1 produced three true-positive findings covering the exact vulnerabilities used in the attack:
- Finding 1 directly identified the getCashPrior() balanceOf() usage as an exchange rate manipulation vector, with a PoC demonstrating 3.81x amplification and bad debt creation
- Finding 2 identified the supply cap bypass as a separate high-severity risk, with a PoC demonstrating 367% cap violation
- Finding 3 identified the interest rate distortion as a revenue and reserve integrity risk
Had these findings been surfaced during a pre-deployment audit or integrated into CI/CD pipelines, the development team would have had actionable, evidence-backed findings with working exploits rather than theoretical warnings. The fix is straightforward (replacing balanceOf() with internalCash) and would have eliminated all three findings simultaneously.
Continuous Monitoring and Re-scan Triggering
The vulnerability existed across multiple deployments. A recurring BugPoCer scan integrated into the protocol's version control workflow would have surfaced this finding on each commit that preserved the vulnerable getCashPrior() implementation, creating a persistent, high-visibility signal that the issue remained unresolved.
Audit Finding Validation with PoC Evidence
The Code4rena audit flagged a related concern, but the Venus team dismissed it as an intentional feature. Olympix's PoC-backed findings provide a qualitatively different form of evidence: not a theoretical concern but a demonstrated, executable exploit with quantified financial impact. A working PoC showing 3.81x borrow capacity amplification and 21,075 USDT in bad debt from 7,500 USDT of collateral is substantially harder to dismiss than a descriptive finding.
Integrating Olympix into the audit response workflow, requiring PoC-backed evidence before closing audit findings as acceptable, would have changed the evidentiary threshold for dismissal and likely surfaced the true risk to the team.
Supply Cap Integrity Checking
Venus's governance-set supply cap of 14.5M THE was a deliberate risk management decision. Olympix's Finding 2 demonstrated that this cap could be violated by a factor of 3.67x with no governance action or on-chain alert. A monitoring integration that validates supply cap enforcement under adversarial conditions (not just nominal deposit flows) would have flagged the cap bypass as a protocol invariant violation, potentially triggering additional controls before the attack reached scale.
Recommendations
1. Immediate (Protocol-Level Fix)
- Replace getCashPrior() balanceOf() with internalCash: The fix is unambiguous. getCashPrior() must return a state variable that is exclusively modified by protocol-sanctioned operations: mint(), redeem(), borrow(), repay(), and liquidateBorrow(). Direct ERC-20 transfers to the contract must have zero effect on exchange rate or interest rate computations.
- Audit all markets in the Venus ecosystem: The vulnerability likely exists in other market implementations. All markets should be audited for the same getCashPrior() pattern and patched simultaneously.
- Review oracle configurations for illiquid assets: Oracle configurations should include TWAP floors and circuit breakers for assets with low liquidity depth to prevent feedback loop amplification.
2. Near-Term (Protocol Governance)
- Implement supply cap enforcement at the balance level: Supply cap checks should operate against the actual underlying balance (internalCash), not just totalSupply of vTokens. This ensures the cap reflects true economic exposure.
- Apply stricter collateral factor limits for illiquid assets: A high collateral factor on THE was too permissive given its liquidity profile. Risk parameters for illiquid assets should reflect liquidation feasibility under stressed conditions.
- Require PoC-backed evidence before closing high/critical audit findings: Dismissing audit findings without verified proof-of-concept validation creates a false sense of security.
3. Structural (Security Program)
- Integrate Olympix BugPoCer into the CI/CD pipeline: Every commit that modifies vToken contracts should trigger an automated BugPoCer scan. Findings that were previously identified and marked as resolved should be automatically re-checked on each relevant commit.
- Implement real-time exchange rate deviation monitoring: Anomalous exchange rate increases (e.g., more than 5% in a single block without corresponding interest accrual) should trigger automated market pausing or oracle circuit breakers. The 3.81x inflation in the March 15 attack would have been immediately detectable with such a monitor.
- Conduct donation attack simulation as part of market listing due diligence: Before listing any new asset as collateral, simulate a donation attack against the proposed market parameters. This would have flagged the THE market as vulnerable before it was deployed.
Venus Protocol Response
Venus Protocol's response to the incident was swift on the operational side:
- Immediate pause of THE market borrowing and withdrawals upon detection of unusual activity
- Precautionary pause of additional markets (BCH, LTC, UNI, AAVE, FIL, TWT) to prevent contagion
- Coordination with Chainalysis and Hexagate for on-chain monitoring and attacker tracking
- Emergency governance proposal to freeze approximately $3M in assets still controlled by the attacker, passed successfully, resulting in the attacker suffering a net loss of approx. $4.7M
- Governance proposal submitted for full bad debt repayment of $2,203,024
- Post-mortem review initiated by Allez Labs (protocol risk manager) covering oracle protections and supply cap enforcement
- getCashPrior() patched to use internalCash state variable, eliminating the root cause across BNB Chain deployments
While the community response was effective at limiting further damage and imposing consequences on the attacker, the approximately $2.18M in bad debt represents a real loss borne by the protocol and its users.
Conclusion
The Venus Protocol THE market exploit is a case study in the cost of dismissed audit findings. A single function, getCashPrior(), reading balanceOf() instead of an internal state variable enabled an attacker to inflate an exchange rate by 3.81x, bypass a supply cap by 367%, and extract $3.7M from the protocol, leaving $2.18M in bad debt. The vulnerability was known and had a straightforward one-line fix.
Olympix's BugPoCer identified every dimension of this attack: exchange rate manipulation, supply cap bypass, and interest rate distortion, each with executable, quantified proof-of-concept exploits. The findings were not theoretical; they demonstrated precisely the attack that occurred, with matching amplification factors and bad debt calculations.
The core lesson for DeFi protocols is that security tooling must produce evidence-grade findings rather than just warnings, and that evidence-grade findings must be treated with commensurate rigor. A PoC showing 21,075 USDT in bad debt from 7,500 USDT of collateral is not an intentional feature with no negative side effects.
Integrating Olympix into the Venus Protocol security workflow, across CI/CD, audit response validation, and real-time monitoring, would have prevented this incident entirely.
References
1. THE Market Incident Post-Mortem — Venus Community Forum
2. BNB Chain THE Market Bad Debt Repayment — Venus Governance Proposal
3. Explained: The Venus Protocol Hack (March 2026) — Halborn
4. Venus Protocol left with roughly $2M in bad debt after exploit — The Block
5. Donation Attack on Venus Protocol Leaves $2.15M in Bad Debt — CryptoTimes (March 19, 2026)
6. Venus Protocol Hit by $3.7M Supply Cap Attack — CryptoTimes (March 16, 2026)
7. Venus' governance token XVS plunges 9% over exploit-driven bad debt — CoinDesk
8. Venus Protocol hacker lost $4.7M after nine months of planning — Protos
10. Venus BugPoCer Findings Report — Olympix (March 15, 2026)
Olympix: Your Partner in Secure Smart Contracts
Olympix provides advanced Solidity analysis tools to help developers identify and fix vulnerabilities before they become critical exploits.
Get started today to fortify your smart contracts and proactively shield them from exploits in the evolving Web3 security landscape.
Connect with us on:
Twitter | LinkedIn | Discord | Medium | Instagram | Telegram | Newsletter

