On the morning of March 31, 2026, somewhere between midnight and 3 AM UTC, a North Korean state hacking group quietly published two new versions of Axios to the npm registry. Axios — the most popular JavaScript HTTP client in existence, embedded in web apps, mobile backends, fintech APIs, and government services the world over had just been turned into a weapon. With over 100 million weekly downloads, Axios is embedded in web applications, mobile apps, backend services, and automated build pipelines across virtually every industry. And for a window of roughly three hours, every developer or automated system that ran "npm install axios" was silently handed a Remote Access Trojan.
What Actually Happened
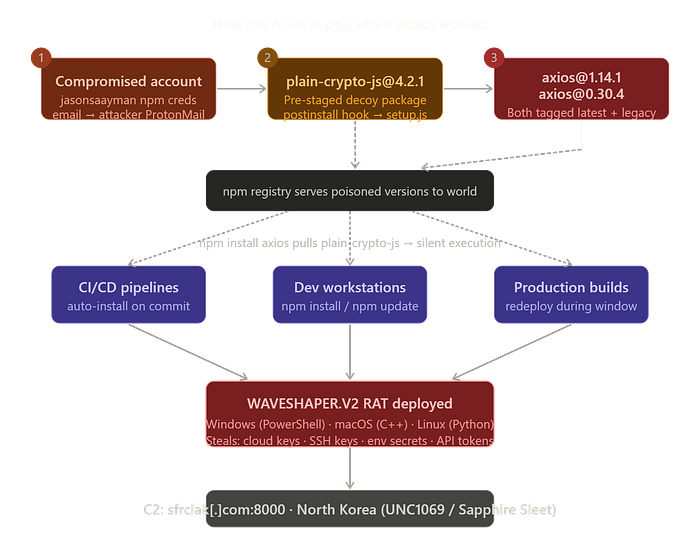
Elastic Security Labs detected a supply chain compromise targeting the axios npm package through automated supply-chain monitoring on March 30, 2026. The attacker compromised a maintainer account and published backdoored versions that delivered a cross-platform Remote Access Trojan to macOS, Windows, and Linux systems through a malicious postinstall hook.
The compromised account belonged to the primary Axios maintainer. The attacker changed the account's registered email to ifstap@proton.me — an attacker-controlled ProtonMail address and used this access to publish malicious builds across both the 1.x and 0.x release branches simultaneously, maximising the number of projects exposed.
Here's the clever part and the part that makes this attack so hard to catch. The attacker didn't touch a single line of Axios code itself. Axios worked exactly as before. Instead, they added one new dependency to the package manifest: plain-crypto-js.
The trusted package's application logic was not modified; instead, the threat actor added a dependency that is never imported by the package's runtime code but only exists to trigger an install-time script to download the second-stage RAT.
The Pre-Staging Operation
What makes this attack genuinely sophisticated is that it was planned well in advance. To avoid detection, the attackers added the malicious dependency pinned to a version that wasn't uploaded yet, this way they could overcome detections, as scanners trying to install this version would not see anything suspicious. Only when the malicious version of plain-crypto-js was uploaded did the malicious behaviour become observable.
The attacker tagged both the latest and legacy channels, maximising the blast radius across projects using either the current or legacy Axios API. The entire delivery chain hinged on npm's postinstall lifecycle hook and the malicious code executed automatically during npm install, with no user interaction required.
Once triggered, the payload dubbed WAVESHAPER.V2 , made itself at home. The first-stage loader dynamically checks the target system's operating system upon execution to deliver platform-specific payloads: PowerShell on Windows, C++ on macOS, Python on Linux. Three platform-native implementations of the same backdoor, all phoning home to the same North Korean command-and-control server. And then it covered its tracks. The dropper performs anti-forensic cleanup by deleting itself and swapping its package.json with a clean copy, erasing evidence of the postinstall trigger from node_modules.
The Most Dangerous Part: npm audit command will not reveal the compromise
There is no postinstall script, no setup.js file, and no indication that anything malicious was ever installed after self-deletion. Running npm audit or manually reviewing the node_modules/plain-crypto-js/package.json will not reveal the compromise.
This is what keeps security teams up at night. The attack self-destructs its evidence. Standard tooling gives you a false all-clear. Meanwhile, your cloud keys, SSH private keys, GitHub tokens, and AWS credentials have already been exfiltrated to a server in Pyongyang.
Here's a timeline of how this campaign escalated across March 2026:
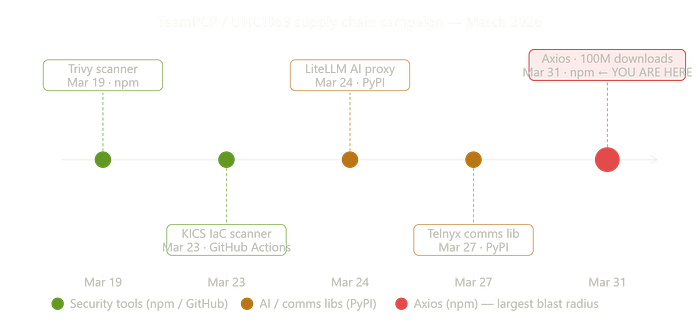
Early analysis indicates this attack may be a continuation of the TeamPCP supply chain campaign. Between March 19 and March 27, 2026, TeamPCP compromised four widely used open-source projects in rapid succession: the Trivy vulnerability scanner, the KICS infrastructure-as-code scanner, the LiteLLM AI proxy library on PyPI, and the Telnyx communications library on PyPI.
Microsoft Threat Intelligence and Google's GTIG both attributed the campaign to a North Korean state actor, Google's team tracks the group as UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018.
What You Need to Do Right Now
- Check your lockfiles first:
# Check for the malicious axios versions
grep -E '"axios"' package-lock.json | grep -E '1\.14\.1|0\.30\.4'
# Check for the injected dependency
npm ls plain-crypto-js2. Check for RAT artifacts on developer machines:
Inspect systems for platform-specific IoCs(Indicators of Compromise): /Library/Caches/com.apple.act.mond on macOS, %PROGRAMDATA%\wt.exe on Windows, and /tmp/ld.py on Linux.
These are the other IOCs that you can look for:
- Domain: sfrclak[.]com
- IP address: 142.11.206.73
- Malicious npm packages: axios@1.14.1 sha-256 checksum: 2553649f2322049666871cea80a5d0d6adc700ca ; axios@0.30.4 sha-256 checksum: d6f3f62fd3b9f5432f5782b62d8cfd5247d5ee71 ; plain-crypto-js@4.2.1 sha-256 checksum: 07d889e2dadce6f3910dcbc253317d28ca61c766
3. If you find either malicious version, assume full compromise
The malicious versions were removed from npm by 03:29 UTC, but in the window they were live, anyone whose CI/CD pipeline, developer environment, or build system pulled a fresh install could have been compromised without ever touching a line of Axios code.
4. Rotate everything
Cloud access keys, npm tokens, SSH private keys, .env secrets, database passwords, GitHub deploy keys — all of it. Treat them as stolen until proven otherwise.
5. Downgrade Axios immediately:
- Safe version for 1.x:
axios@1.14.0 - Safe version for legacy:
axios@0.30.3
6. Pin your dependencies.
Disable auto-updates for Axios npm packages, since the malicious payload includes a hook that will continue to attempt to update.
The Bigger Picture
This attack didn't require exploiting a bug in Axios. There was no zero-day, no memory corruption, no cryptographic flaw. The attackers simply compromised one human, a trusted maintainer and leveraged the ecosystem's unconditional trust in official package releases to do the rest. This follows a now-familiar pattern: compromise a legitimate maintainer account, publish a malicious version of a trusted package, and rely on the ecosystem's implicit trust of registered packages.
The npm ecosystem and the open-source software supply chain broadly runs on trust. That trust is increasingly being weaponized by nation-state actors who have realized that targeting the toolchain is far more efficient than attacking individual organizations one by one.
Sources: