How Cyber Extortion Became a Structured Global Economy in 2025
The year 2025 will likely be remembered as the moment when ransomware fully crossed the line from opportunistic cybercrime into a mature and organized digital industry. The scale of attacks alone tells part of the story. Depending on the telemetry source, the number of ransomware incidents worldwide reached somewhere between roughly 7,400 and more than 9,200 cases during the year. That represents an increase of approximately 30 to 45 percent compared with 2024. Yet the true transformation is not simply the growth in numbers. The deeper shift lies in the structure of the threat ecosystem itself. Ransomware operations now resemble coordinated enterprises with specialized divisions, affiliate recruitment programs, technical research teams, and negotiated revenue sharing models.
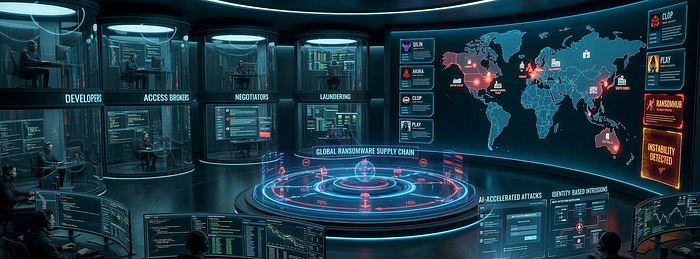
Security analysts increasingly describe this system as a professionalized criminal economy rather than a loose collection of hacking groups. The older ransomware-as-a-service structure that dominated the early 2020s has fractured into a decentralized network of actors with overlapping partnerships and shifting alliances. Developers produce encryption tools, access brokers sell entry points into corporate networks, negotiators manage ransom discussions, and laundering partners handle the financial flows. According to multiple cybersecurity research reports published throughout 2025, this division of labor has made ransomware more resilient than ever. When law enforcement dismantles one brand or infrastructure node, affiliates simply migrate to another operation. The ecosystem absorbs disruption and continues functioning.
The rise of collaborative "supergroups" illustrates how far the ransomware economy has evolved. Some operations now bring together specialists from multiple criminal organizations to conduct large scale campaigns. One such example is the alliance sometimes referred to by researchers as Scattered Lapsus$ Hunters, where individuals linked to earlier hacktivist or financially motivated groups cooperate in high impact attacks. These alliances behave less like gangs and more like project based coalitions assembled for specific targets.
Financial incentives remain the driving force behind this system. In sectors where operational downtime carries enormous costs, ransom demands have risen dramatically. Manufacturing companies, for instance, saw average ransom demands jump from roughly $523,000 in 2024 to close to $1.2 million in 2025. The logic behind these numbers is brutally simple. If a company loses millions of dollars every day its production line stops, attackers know the leverage they possess.
Within this expanding ecosystem several ransomware groups emerged as dominant actors during 2025. Five groups in particular shaped the trajectory of the year's cyber extortion campaigns. These groups are Qilin, Akira, Clop, Play, and RansomHub. Each represents a distinct operational philosophy and technological strategy, revealing how varied the ransomware economy has become.
Qilin and the Rise of the Prolific Predator
Among all ransomware groups active in 2025, Qilin stands out as the fastest rising force. Originally appearing in August 2022 under the name Agenda, the group experienced explosive growth during the following years. By the end of 2025 Qilin was responsible for roughly 14 to 15 percent of all recorded ransomware attacks globally. The number of victims attributed to the group exceeded one thousand during the year, representing a growth rate of more than 400 percent compared with previous periods.
Part of Qilin's success lies in its technical transformation. The original ransomware variant was written in Go, a language commonly used for cross platform malware. However, by late 2024 the developers shifted to Rust. This change was strategic rather than cosmetic. Rust allows attackers to build highly portable malware capable of targeting Windows, Linux, and VMware ESXi systems simultaneously while also complicating reverse engineering efforts. The result is ransomware that can move across heterogeneous corporate environments with relative ease.
Qilin operates through a structured affiliate program typical of modern ransomware operations. The core developers maintain the encryption platform, the command infrastructure, and the affiliate dashboard used to manage attacks. Independent operators then conduct the intrusions themselves, paying between fifteen and twenty percent of ransom revenue to the developers. This model allows the organization to scale rapidly because dozens of affiliates can run campaigns simultaneously.
The group's attack methods demonstrate significant technical sophistication. Initial access frequently comes through voice phishing attacks, where attackers impersonate IT staff and convince employees to reveal credentials. In other cases the group exploits vulnerabilities in widely deployed enterprise software. Security researchers observed Qilin exploiting weaknesses in Veeam Backup and Replication as well as Fortinet VPN appliances throughout 2025.
Once inside a network, Qilin often deploys custom tools designed to disable endpoint security software before encryption begins. These tools are sometimes referred to as EDR killers because they terminate security monitoring processes before defenders can react. After security controls are neutralized the attackers move laterally through the network, exfiltrate large volumes of data, and only then trigger encryption.
The consequences of these attacks can be devastating. One of the most widely reported incidents linked to Qilin involved the British healthcare provider Synnovis in June 2024. The attack disrupted pathology services for several hospitals across London. More than ten thousand outpatient appointments and roughly seventeen hundred surgical procedures had to be canceled. According to reporting from healthcare security analysts, the attack caused at least £32 million in direct recovery costs and contributed to at least one patient death due to delayed treatment.
Incidents like this demonstrate that ransomware is no longer merely a financial crime. It has become a threat to public safety and critical infrastructure.
Akira and the Professionalization of the Conti Legacy
While Qilin represents rapid growth, Akira embodies continuity within the ransomware world. The group first appeared in March 2023 but quickly gained credibility among cybercriminal communities because many analysts believe its operators include former members of the notorious Conti ransomware organization.
Evidence supporting this connection includes similarities in code structures, identical file exclusion rules used during encryption, and the use of overlapping cryptocurrency wallet infrastructure. Despite these links Akira has carefully avoided the political controversies that contributed to Conti's downfall following the Russian invasion of Ukraine. Instead the group maintains a strictly profit driven profile.
By the end of 2025 Akira had claimed responsibility for between 735 and 947 victims. Researchers estimate the group extracted roughly $244 million in ransom payments across North America, Europe, and Australia.
Akira's technical approach relies heavily on what security professionals call living off the land techniques. Instead of deploying large amounts of custom malware, attackers use legitimate administrative tools already present within the target environment. This approach allows them to move through networks while blending in with normal system activity.
Access is commonly achieved through vulnerabilities in enterprise VPN appliances, particularly those produced by Cisco and SonicWall. Once access is established the attackers escalate privileges, identify valuable systems, and deploy encryption tools across virtual infrastructure environments.
In 2025 Akira introduced a new encryption tool known as Megazord written in Rust. This variant specifically targets VMware ESXi and Nutanix AHV virtualization platforms, reflecting the growing importance of virtual infrastructure within modern enterprise networks. By encrypting virtual machine hosts rather than individual systems, attackers can paralyze entire corporate environments in a single operation.
The group's targets reveal a clear economic strategy. Manufacturing companies represent the largest share of victims, followed by healthcare organizations, universities, and financial services firms. These sectors share a common characteristic. They cannot tolerate extended operational disruption, which increases the likelihood that victims will pay.
Clop and the Power of Mass Exploitation
Where Qilin and Akira specialize in targeted intrusions, the Clop ransomware group has built its reputation through mass exploitation campaigns. Active since at least 2019 and believed to be connected with the cybercriminal organization TA505, Clop has repeatedly demonstrated how a single vulnerability in widely used enterprise software can produce hundreds of victims simultaneously.
The group's most significant campaign in 2025 involved Oracle E Business Suite, one of the most widely deployed enterprise resource planning platforms in the world. Security analysts discovered that Clop operators had exploited previously unknown vulnerabilities within the system beginning in mid 2025.
These vulnerabilities allowed attackers to access sensitive databases containing financial records, payroll data, and human resources files. Instead of encrypting systems immediately, the attackers quietly exfiltrated data for several months. On September 29, 2025, executives at dozens of organizations began receiving emails informing them that their internal data had been stolen.
The list of victims included prominent companies and institutions such as Logitech, Harvard University, Schneider Electric, and Mazda. According to investigators analyzing the incident, Clop claimed to have extracted more than 1.8 terabytes of internal data from Logitech alone.
This campaign illustrates an important trend within ransomware operations. Increasingly, attackers are abandoning encryption entirely in favor of pure extortion. Instead of locking systems, they threaten to publish stolen data unless victims pay. For large corporations the reputational damage and regulatory consequences of a data leak can exceed the cost of a temporary outage.
The Clop strategy also reveals the systemic risks associated with software supply chains. A single vulnerability in widely used enterprise software can instantly expose hundreds of organizations across multiple industries.
Play and the Quiet Specialists
Another significant ransomware group during 2025 was Play. Emerging in 2022, the group initially operated as a closed team but later adopted a ransomware as a service model that allowed affiliates to participate in attacks.
Unlike groups that actively promote their operations on dark web forums, Play maintains a relatively low public profile. Their campaigns focus on operational precision rather than publicity.
Play typically enters networks through compromised credentials rather than software exploits. Once access is established the attackers move slowly and methodically, often remaining inside a network for several weeks. During this time they map the environment, identify high value data repositories, and exfiltrate sensitive information.
Only after this preparation phase do they deploy their custom encryption malware. The result is a highly damaging double extortion scenario in which both operational disruption and data exposure threaten the victim simultaneously.
Play's victims during 2025 included financial institutions, technology companies, media organizations, and managed service providers. Because managed service providers often support multiple downstream clients, a single compromise can cascade into dozens of secondary infections.
RansomHub and the Volatile Challenger
Not every ransomware organization achieves long term stability. The rise and fall of RansomHub during 2025 illustrates the volatile nature of the cyber extortion economy.
The group first appeared in February 2024 and rapidly gained popularity among affiliates. By early 2025 RansomHub had recorded more than 250 attacks in a single quarter, placing it among the most active ransomware groups in the world.
However the organization soon faced internal conflict. The most notable episode involved the massive breach of Change Healthcare in the United States. After the victim paid a ransom reportedly worth $22 million to another ransomware group, the operators disappeared with the funds without compensating their affiliate.
The disgruntled affiliate subsequently approached RansomHub with the stolen data and attempted to extort the victim again. The incident affected approximately 192.7 million individuals and produced economic damages estimated at more than $2 billion.
Despite its early success RansomHub experienced operational disruptions in April 2025. Affiliates began migrating to more stable platforms such as Qilin and Akira, and the group's activity declined sharply.
This episode exposed a fundamental weakness within the ransomware economy. Even among criminals, trust remains fragile.
Geography of the Ransomware Crisis
The global distribution of ransomware victims reveals a clear pattern. High income economies remain the most attractive targets because organizations operating in these environments have greater financial resources and stronger incentives to restore operations quickly.
The United States continues to account for the majority of ransomware incidents. Security monitoring of dark web leak sites suggests that between 50 and 64 percent of publicly claimed victims in 2025 were American organizations.
Canada, Germany, the United Kingdom, and France follow behind, though with significantly smaller shares of global attacks. Germany in particular experienced a notable increase in incidents during 2025, with researchers reporting growth of more than 60 percent compared with the previous year.
Asia Pacific also saw significant changes. South Korea experienced a dramatic surge in ransomware incidents with year over year growth estimated at more than 500 percent. Australia likewise reported a substantial increase in attacks, particularly against infrastructure and manufacturing companies.
Why Manufacturing and Healthcare Are Primary Targets
Certain industries consistently appear at the center of ransomware campaigns. Manufacturing remains the most frequently targeted sector, accounting for roughly 14 to 19 percent of all recorded incidents.
Manufacturers often rely on legacy operational technology systems that cannot easily be patched or replaced. When these systems fail production stops immediately, creating enormous financial pressure to restore operations quickly.
Healthcare has also become a major target. In some threat tracking reports from 2025 healthcare organizations experienced more ransomware incidents than any other sector.
The reason is simple. Hospitals cannot afford extended downtime. When diagnostic systems, medical records, or laboratory infrastructure become unavailable, patient care suffers immediately. Attackers understand this pressure and use it to demand higher ransom payments.
Artificial Intelligence and the Future of Cyber Extortion
The ransomware ecosystem continues to evolve as new technologies become available. Artificial intelligence is beginning to accelerate several stages of the attack lifecycle.
Generative AI tools can assist attackers in writing phishing emails, researching vulnerabilities, and automating parts of the lateral movement process once inside a network. Some incident response teams reported that the fastest ransomware attacks in 2025 moved through corporate environments four times faster than similar attacks just two years earlier.
Another major trend involves identity based attacks. Investigators estimate that weaknesses in identity management systems were involved in nearly 90 percent of ransomware incidents during the year. Instead of breaking through security perimeters, attackers increasingly log in using stolen credentials, session tokens, or compromised authentication infrastructure.
This shift has profound implications for cybersecurity strategy. Traditional perimeter defenses such as firewalls and network segmentation remain important, but they cannot stop attackers who already possess legitimate access credentials.
The New Economics of Cyber Extortion
Taken together the events of 2025 reveal a simple truth. Ransomware is no longer a fringe cybercrime problem. It is a structured economic system with its own market dynamics, labor divisions, and innovation cycles.
The groups dominating the year's headlines represent only the visible portion of this ecosystem. Beneath them exists a vast supply chain of access brokers, malware developers, infrastructure providers, negotiators, and laundering services.
Law enforcement operations can disrupt individual groups, but the underlying economy remains intact. As long as digital infrastructure continues expanding faster than organizations can secure it, ransomware will remain profitable.
Defending against this threat therefore requires more than technical tools. Organizations must adopt a proactive security posture centered on identity protection, rapid patch management, supply chain monitoring, and resilient data backup strategies.
The ransomware economy of 2025 demonstrated remarkable adaptability. If defenders hope to keep pace, their strategies must evolve just as quickly.