🔧 Supercharge Your Burp Suite Workflow
✍️ By Ghostyjoe
🕷️ Top 10 Burp Suite Extensions for Bug Bounty Hunters
🔧 Supercharge Your Burp Suite Workflow
✍️ By Ghostyjoe
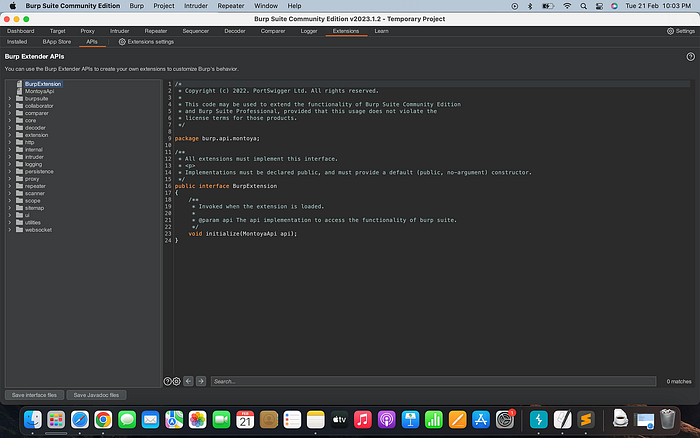
Burp Suite is already one of the most powerful tools used by bug bounty hunters and professional pentesters. But what really makes Burp incredibly powerful is its extension ecosystem.
Through the BApp Store, you can install extensions that add new capabilities such as:
🔎 Advanced scanning ⚡ Automation 🧠 Smart payload generation 📊 Data analysis 🕵️ Vulnerability discovery
In this guide, we will explore 10 Burp Suite extensions that every bug bounty hunter should consider using.
📦 How to Install Burp Suite Extensions
Before we start, here's how to install extensions.
Step 1
Open Burp Suite
Step 2
Navigate to:
Extender → BApp StoreStep 3
Click Install next to the extension.
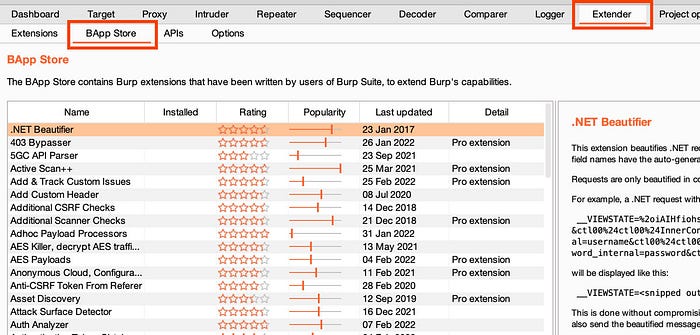
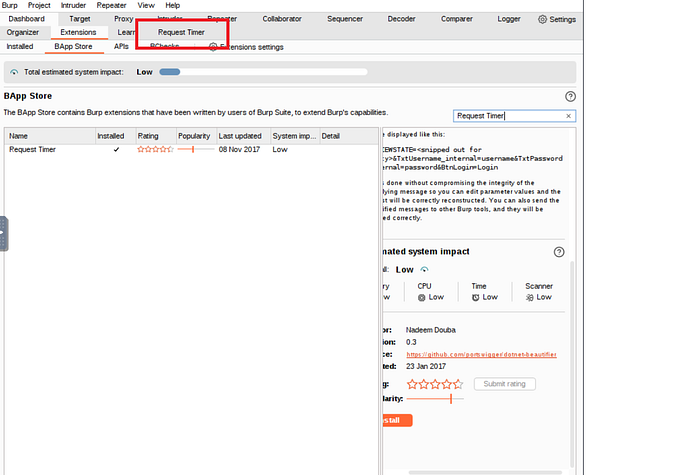

Once installed, extensions become available inside the Burp interface.
1️⃣ Autorize
One of the best extensions for detecting authorization vulnerabilities such as IDOR and broken access control.
What It Does
Autorize automatically compares requests between:
👤 Low privilege user 👑 High privilege user
This helps detect privilege escalation vulnerabilities.
Example Workflow
Login as normal user
Capture request
Send to Autorize
Replay as admin
Compare responsesIf responses are similar, you may have found an access control flaw.
2️⃣ Param Miner
Param Miner is a hidden parameter discovery tool created by PortSwigger.
Why It's Powerful
Many applications use undocumented parameters.
Example:
?debug=true
?admin=true
?internal_api=1Param Miner automatically brute forces thousands of potential parameters.
3️⃣ Active Scan++
Active Scan++ enhances Burp's scanning engine.
It adds checks for:
✔ Cache poisoning ✔ Header injection ✔ CORS misconfigurations ✔ Edge case vulnerabilities
This extension helps uncover vulnerabilities that default scans sometimes miss.
4️⃣ Turbo Intruder
Turbo Intruder is designed for high-speed attacks.
It is extremely useful for testing:
- Race conditions
- Rate limiting
- Brute-force attacks
Example
Testing a password reset race condition.
Send 1000 simultaneous requestsTurbo Intruder can launch these attacks far faster than Intruder.
5️⃣ Logger++
Logger++ provides advanced traffic logging and filtering.
This makes it easier to track:
- Interesting responses
- Error messages
- Unique parameters
- Hidden endpoints
Why It Matters
Bug bounty hunting often involves huge volumes of traffic, and Logger++ helps you filter the noise.
6️⃣ Collaborator Everywhere
This extension automatically inserts Burp Collaborator payloads into requests.
This helps detect out-of-band vulnerabilities such as:
- SSRF
- Blind XXE
- Blind command injection
If the server interacts with the payload, Burp will detect it.
7️⃣ JS Link Finder
JavaScript files often contain hidden endpoints and APIs.
JS Link Finder scans JavaScript files to extract URLs.
Example discovered endpoints:
/api/v2/admin
/internal/auth
/private/debugThis is extremely useful during recon and endpoint discovery.
8️⃣ Retire.js
Retire.js detects outdated JavaScript libraries.
Example findings:
jQuery 1.8 (vulnerable)
AngularJS outdated
Bootstrap vulnerable versionThese outdated libraries can expose applications to known vulnerabilities.
9️⃣ JSON Beautifier
Many APIs return large JSON responses that are difficult to read.
JSON Beautifier formats the output so you can easily analyze:
- API responses
- Tokens
- IDs
- Authentication data
🔟 Hackvertor
Hackvertor is an extremely powerful encoding and decoding tool.
It supports:
- Base64
- URL encoding
- Hex
- HTML entities
- Custom payload manipulation
Example
Convert payload automatically:
<script>alert(1)</script>Into:
%3Cscript%3Ealert%281%29%3C/script%3EVery useful when crafting payloads.
🧠 Pro Tip for Bug Bounty Hunters
Do not install every extension you see.
Too many extensions can:
❌ Slow down Burp ❌ Cause crashes ❌ Create conflicts
Instead, build a small toolkit you understand well.
🛠️ Example Burp Workflow
A typical workflow might look like this:
1 Recon (subfinder, httpx, katana)
2 Browse application through Burp proxy
3 Discover endpoints with JS Link Finder
4 Test parameters with Param Miner
5 Check authorization with Autorize
6 Perform attacks with Turbo IntruderThis combination dramatically increases your chances of discovering vulnerabilities.
⚠️ Ethical Use & Disclaimer
This content is intended only for educational purposes and authorized security testing.
Only test:
✔ Systems you own ✔ Systems you have permission to test ✔ Official bug bounty programs
Unauthorized testing may be illegal.
Always follow responsible disclosure practices.
🧠 Final Thoughts
Burp Suite becomes far more powerful with the right extensions.
If you are serious about bug bounty hunting, these extensions will significantly improve your workflow.
The most successful hunters combine:
🕷️ Strong recon 🧠 Manual testing ⚡ Smart automation
👏 If you found this helpful, a few claps on Medium are always appreciated.
☕ Support my work: https://buymeacoffee.com/ghostyjoe