Hello everyone, I'm Sherlok, and today I'd like to share a story about how I found a hardcoded AWS AppSync API key in the frontend JavaScript.
While doing some recon, I decided to check the JavaScript files, and it turned out to be a good idea because I found:
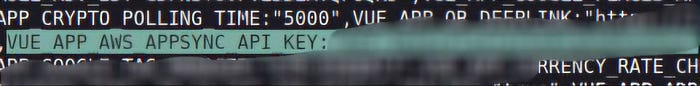
Now, having an API key in the frontend isn't always critical - sometimes it's used for public, read-only data. But in this case, the key had way more permissions than it should have.
It allowed not only queries (reading data), but also mutations (writing data).
In simple terms: anyone on the internet could send requests and create data in the backend without logging in.
Well, let's check if this API key works
To do this, we'll simply use the curl POST command:
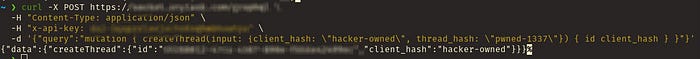
And it worked.
That confirmed the API key was valid — so let's break down what's actually happening behind the scenes.
How It Worked
Once the API key was extracted, it could be used to send requests directly to the GraphQL endpoint.
No authentication, no tokens, nothing else required — just the key.
By crafting a simple mutation request, it was possible to create new objects (like threads) in the system, and the server would happily accept it and return a valid response.
Impact
An attacker can:
- Create arbitrary threads without authentication
- Pollute application data
- Abuse backend business logic
- Perform spam or automated resource creation
This significantly impacts data integrity and trust in the messaging/thread system.
Root Cause (in plain terms)
This wasn't some complex exploit — just a combination of bad decisions:
- API key exposed in frontend (publicly accessible)
- Key allowed to perform write operations
- No authentication required for mutations
Basically, the backend assumed "if you have the key, you're trusted" — which is not how it should work.
Disclosure Note
I responsibly reported this issue to the company with a clear proof of concept and minimal impact testing. However, the report was marked as a duplicate.

Bugs like this are simple, but extremely impactful — and they show why backend validation should never rely on client-side secrets.
Anyway, that's it for this one. Happy hacking 👾
