1. Initial Reconnaissance — Understanding the Objective
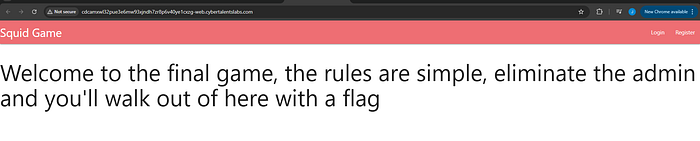
Upon accessing the application, the goal was clearly stated: eliminate the administrator.
This immediately suggested that the challenge would likely involve:
- Privilege escalation
- Authorization bypass
- Parameter manipulation
Instead of randomly testing inputs, the approach was logic-driven: If the goal is to eliminate the admin, then we must find how accounts are deleted and determine whether that process can be manipulated.
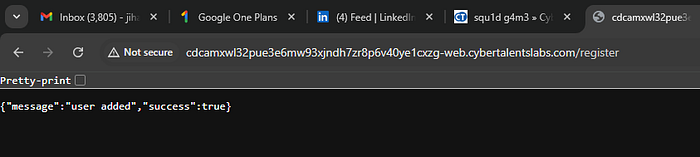
2. Registration and Behavioral Observation
The application provided a typical:
- Registration page
- Login page
The first step was registering a normal user account and logging in.
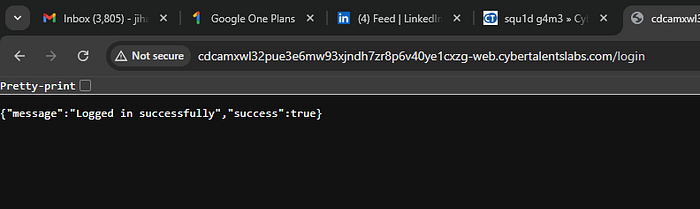
After authentication, the interface displayed user-related functionality, including account management options. From here, a critical observation emerged:
- There was a deletion feature.
- The application allowed users to trigger deletion requests.
- No obvious role restrictions were enforced in the UI.
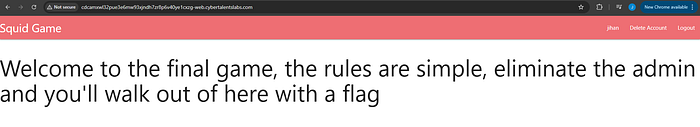
This led to a working hypothesis:
If the application does not properly validate ownership or authorization during account deletion, it may be possible to delete another user — including the administrator.
3. Traffic Interception Using Burp Suite
To validate this hypothesis, the next step was intercepting HTTP requests using Burp Suite.
Action Performed:
Attempted to delete the logged-in account while intercepting the outgoing request.
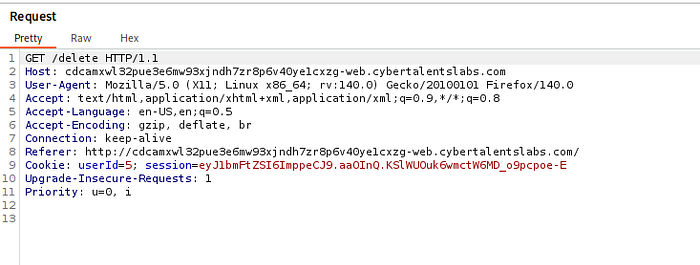
Observation:
The deletion request contained a parameter:
userid=<value>This was the critical finding.
The userid parameter determined which account the server would delete.
At this stage, a security question became central:
Does the server verify that the authenticated user actually owns the
useridbeing deleted?
If not, this would indicate an Insecure Direct Object Reference (IDOR) vulnerability.
4. Exploitation — Parameter Manipulation
Most web applications assign:
userid=1→ Adminuserid=2+→ Regular users
After intercepting the deletion request in Burp Suite:
- The original
useridvalue (assigned to the test account) was identified. - The value was modified manually to:
userid=13. The modified request was forwarded to the server.
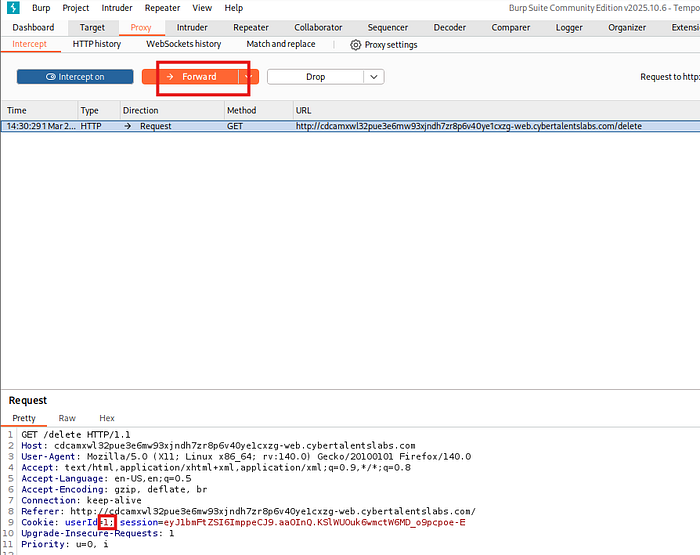
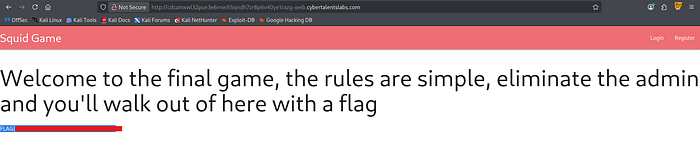
Result:
The challenge returned the flag, confirming completion.
5. Vulnerability Analysis
The root issue was:
Insecure Direct Object Reference (IDOR)
The application:
- Trusted user-supplied input (
userid) - Did not validate ownership
- Did not enforce proper authorization checks on the backend
Instead of verifying:
Is the requester authorized to delete this specific account?The server simply executed the deletion based on the provided ID.
This represents a classic broken access control vulnerability.
6. Exploitation Flow Summary
Step 1 — Understand the Goal
Eliminate the admin.
Step 2 — Explore Application Functionality
Register and log in as a normal user.
Step 3 — Identify Sensitive Actions
Locate the account deletion feature.
Step 4 — Intercept HTTP Traffic
Use Burp Suite to capture the deletion request.
Step 5 — Identify Controllable Parameters
Discover the userid parameter.
Step 6 — Modify and Exploit
Change userid to 1.
Step 7 — Achieve Objective
Admin account deleted. Flag retrieved.

