This writeup demonstrates how to exploit a CL.TE HTTP request smuggling vulnerability to bypass front-end security controls. The application uses a front-end and back-end server, and the front-end does not support chunked encoding while also blocking access to /admin. By smuggling a crafted request to the back-end server, we bypass the front-end restrictions, access the admin panel, and delete a user.
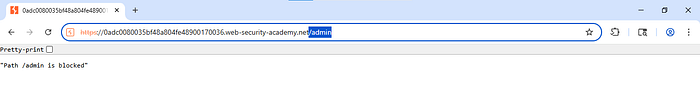
As shown, when we try to access the admin panel through /admin, the application returns an error indicating that the path is blocked.
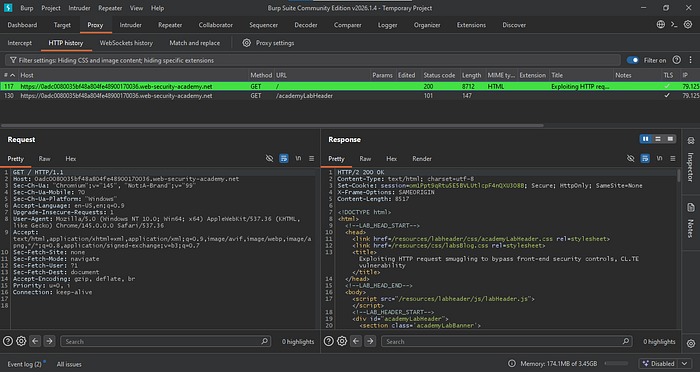
Step 1: Intercept
Intercept the request to the application and send it to Repeater.
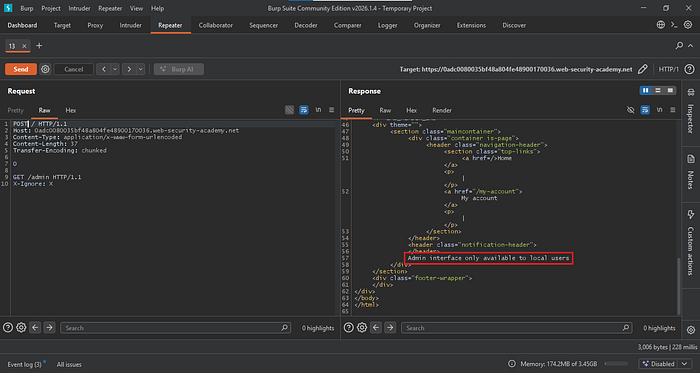
Step 2: Bypassing
In your request, change the HTTP method from GET to POST, then remove all headers except Host. Add the headers Content-Type, Content-Length, and Transfer-Encoding, and include a GET request for the /admin path.
If you send this request twice, you will receive an error stating that the admin interface is only available to local users.
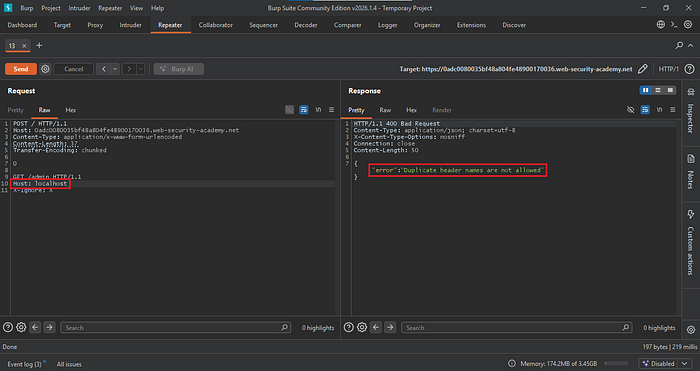
Now add a Host header to the GET request and set its value to localhost. If you send the request twice, you will receive an error indicating that duplicate header names are not allowed.
Step 3: Exploitation
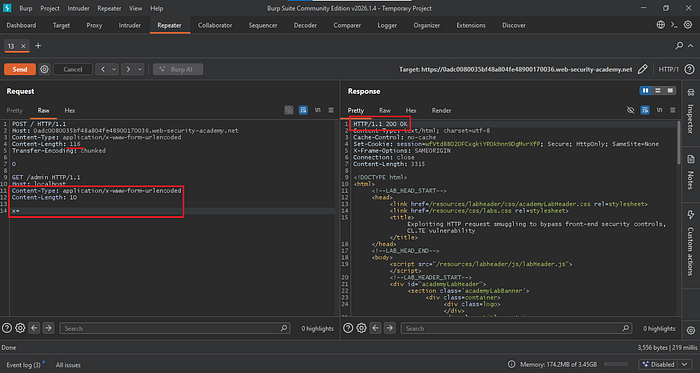
Now copy the Content-Type and Content-Length headers into the GET request, and change the Content-Length values to 116 for the POST method and 10 for the GET method. Add x= at the end, which will serve as a placeholder for a variable value.
If you send the request twice, you should receive a 200 OK response, indicating that you can now access the admin panel.
Now modify the GET request to delete a user by adding /delete?username=carlos. In this case, it will delete the user carlos. If you send the request twice, you should receive a 302 response, indicating that the user has been successfully deleted.

To prevent this type of attack, make sure the front-end and back-end servers handle requests in the same way and do not interpret them differently. Configure the system to block or reject unusual or malformed requests instead of forwarding them. Restrict access to sensitive paths like
/adminat the back-end as well, not just at the front-end. Keeping servers updated and using secure default settings helps ensure that security controls cannot be bypassed through request smuggling.
