Today, I want to share my first valid bug and my first bounty in bug hunting.
I started by choosing a program to hunt for access control vulnerabilities, and I decided to begin with one of my favorite programs: Tesla.

I first created an account on the main domain and started exploring the options available through:
https://tesla.com/teslaaccount
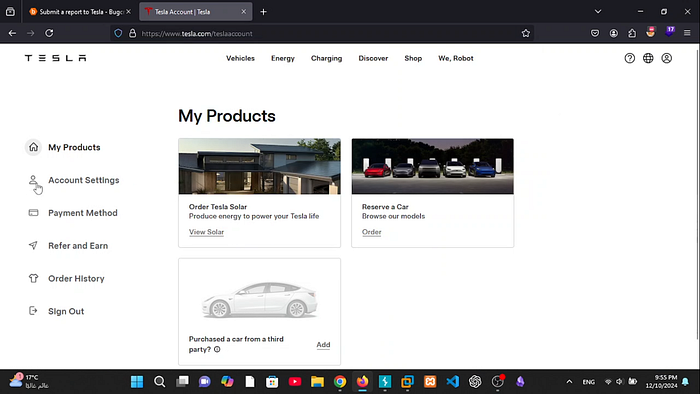
Nothing really caught my attention except Account Settings. When I clicked on it, I was redirected to:
https://accounts.tesla.com/en_US/account-settings/personal-information
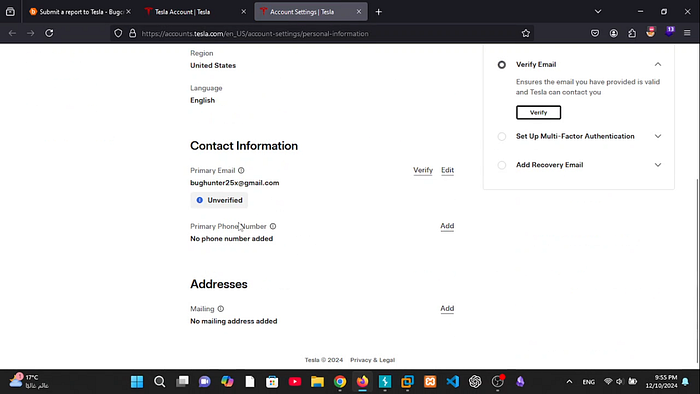
This page displayed account information such as the user's email address, phone number, and other personal details.
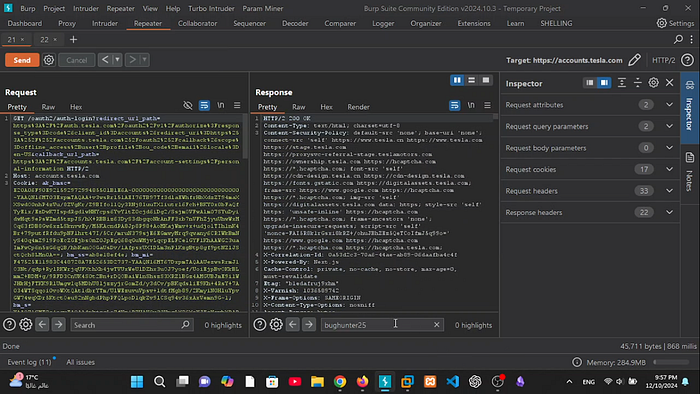
After that, I created a second account, opened Burp Suite, and refreshed the page from both accounts. Then, I captured the following GET request and sent it to Repeater, as shown in the screenshot.
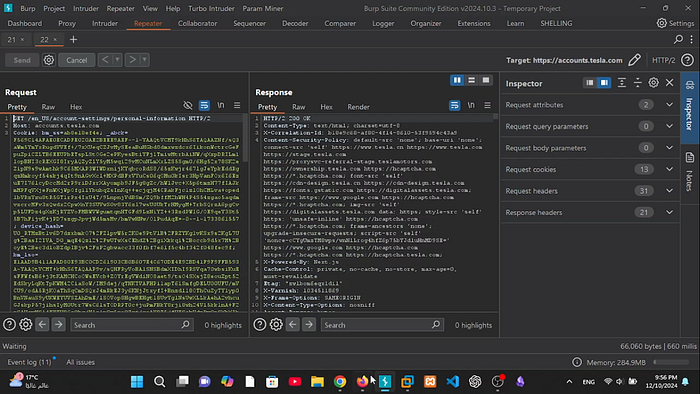
After analyzing the request, I noticed that the server identified the user based on a cookie parameter called:
auth_access_token=
This cookie contained a JWT token value, similar to the one shown in the screenshot.

When decoding the Base64 part of the token, the payload looked like this:
{
"iss": "https://auth.tesla.com",
"aud": [
"https://accounts.tesla.com/",
"https://auth.tesla.com/oauth2/v1/userinfo"
],
"azp": "accounts",
"sub": "f3c83e9d-83f0-46e5-aac8-91b2651ca72e"
As you can see, the sub value contained the account UUID.
At that point, I took the UUID from my second account and replaced the UUID in the first account's request. In other words, I copied the victim account's UUID value and pasted it into the attacker account's request instead of the attacker's original UUID.
The server responded with HTTP 307.
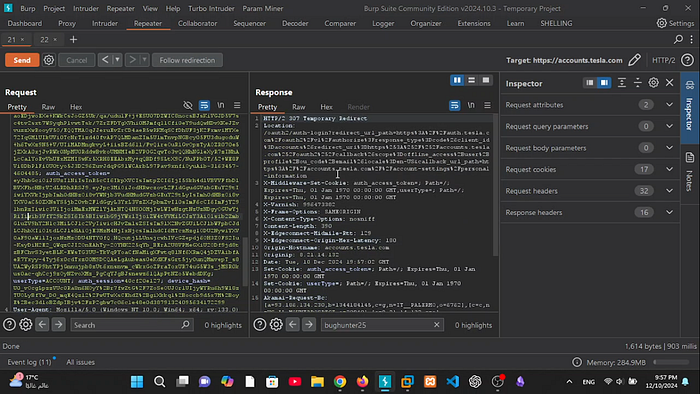
After following the redirect, I reached the following endpoint:
GET /oauth2/auth-login?redirect_url_path=https%3A%2F%2Fauth.tesla.com%2Foauth2%2Fv1%2Fauthorize%3Fresponse_type%3Dcode%26client_id%3Daccounts%26redirect_uri%3Dhttps%253A%252F%252Faccounts.tesla.com%252Foauth2%252Fcallback%26scope%3Doffline_access%2Buser%2Bprofile%2Bou_code%2Bemail%26locale%3Den-US&callback_url_path=https%3A%2F%2Faccounts.tesla.com%2F%2Faccount-settings%2Fpersonal-information
By searching through the response, I was able to find the victim account's email.

At that time, I also tried to find a way to disclose other users' UUIDs, but unfortunately I could not find any working method. So I reported the vulnerability as it was, and I received the following response from Tesla.

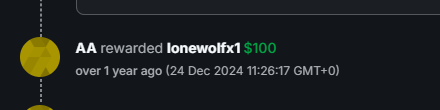
About two weeks later, I received the bounty, and later the vulnerability was fixed.
You can find the PoC video here: https://youtu.be/omc9kGl6DK4?si=rMWydDcrZ80NfaID
