The Communication Chasm
One of the most persistent structural challenges in cybersecurity is the communication gap between technical teams and organizational leadership. Security professionals rely heavily on shorthand — terms like C2, SQL injection, and zero-day — that are efficient among peers but immediately alienating to non-technical executives. When leadership cannot understand a risk, they will not allocate budget to address it.
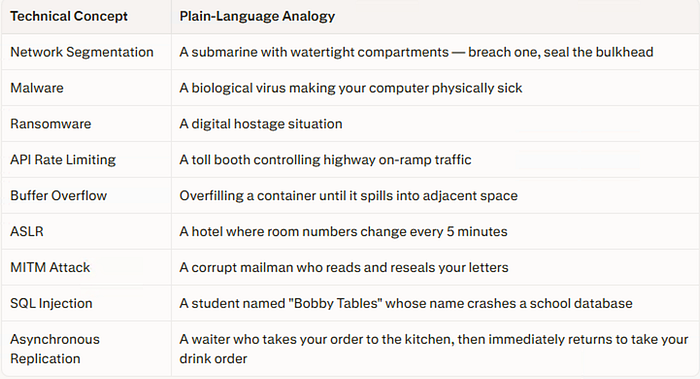
The solution is analogy. Translating technical architecture into physical, real-world comparisons bridges this gap instantly:
The Three States of Data
Data exists in three operational states, each requiring a distinct defensive approach:
1. Data at Rest Inactive data stored on servers or drives. Threat: physical hardware access via JTAG, SPI, or SATA interfaces. Defense: full-disk encryption using tools like Microsoft BitLocker, Linux eCryptFS, or Trusted Platform Modules (TPM). Tradeoff: computational overhead from symmetric encryption at scale.
2. Data in Flight (In Motion) Data traveling over a network — from local TCP packets to global internet streams. Threat: interception via MITM attacks. Defense: VPN tunneling (L2TP, IPsec, SSL/TLS), Tor for anonymity.
3. Data in Use (In Process) The most vulnerable state — data being actively processed must exist in plain text in RAM. Threat: memory-scraping exploits. Example: the Heartbleed vulnerability in OpenSSL, where a malformed heartbeat packet caused servers to leak active working memory, exposing passwords, session cookies, and private encryption keys.
Key Attack Methodologies (CNE)
Computer Network Exploitation (CNE) involves weaponizing a system's own architecture against itself:
- Buffer Overflow: Excess input data spills into adjacent memory and can force the CPU to execute malicious code. Mitigated by ASLR (Address Space Layout Randomization), which randomizes memory locations to prevent reliable payload delivery.
- SQL Injection: Malicious SQL commands inserted into input fields (e.g., login forms) cause databases to execute unintended queries — extracting data or dropping tables.
- MITM Attacks: An attacker inserts their infrastructure between client and server, intercepting data in transit without detection.
- SYN Flooding / DoS: Exhausting server resources by flooding with connection requests. Note: cloud-hosted DoS tests are often naturally throttled by the hypervisor's Linux scheduler, which prevents any single virtual CPU thread from monopolizing physical resources.
- IoT RAM Exhaustion: Flooding lightweight IoT devices with DNS responses via the
getaddrinfo()API forces dynamic RAM allocation until memory is fully exhausted and the device crashes — no traditional "hack" required.
Defensive Architecture
VPN Tunneling Tiers:
- Layer 2 (Bridging): L2TP, OpenVPN bridged mode — effective for localized use, limited scalability
- Layer 3 (Routing): PPTP, IPsec, SSL/TLS — enterprise standard; handles large topologies and both IPv4/IPv6
Tor (The Onion Router): Routes traffic through three nodes (entry → middle → exit) using layered Diffie-Hellman-negotiated encryption. No single node knows both the origin and the destination, ensuring anonymity.
Firewall Tiers:
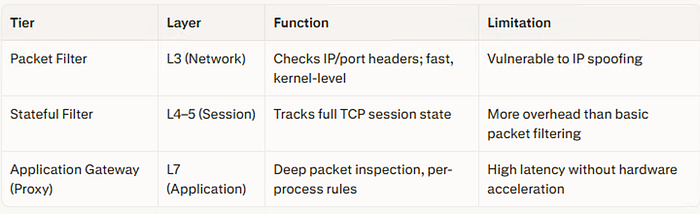
Next-Generation Firewalls (Cisco, Fortinet, Palo Alto) unify all three tiers with dedicated silicon, adding SD-WAN routing and multi-cloud protection.
CERT Top 10 Secure Coding Practices (Key Principles)
- Validate all input — Treat all inbound data as inherently malicious; prevents SQL injection and buffer overflows
- Keep design simple — A minimal codebase reduces the attack surface
- Default deny posture — Access must be explicitly granted; deny everything else by default
- Principle of least privilege — Every user and process receives only the minimum permissions required
Emerging Risk: AI in Security Tooling
As organizations increasingly rely on AI to write and audit security code, a new architectural risk emerges: what if AI tools inherit the logical blind spots and biases of their creators? Unquestioning trust in automated security systems may itself become an exploitable vulnerability — a paradigm shift that security architects must begin to account for.
Published by SDN Tech Networking Podcast | Insights sourced from the SDN Tech Forum #Cybersecurity #NetworkSecurity #CyberAwareness #InfoSec #DataProtection #CyberThreats #TechPodcast #SDNTech #ZeroTrust #Firewall #VPN #Encryption #CyberRisk #CISO #SecureCoding #Ransomware #Malware #DataBreach #IoTSecurity #TechLeadership #CybersecurityForAll #DigitalSecurity #Heartbleed #SQLInjection #TorNetwork #sdntechforum
🙏 Thank you 🙏 for being a part of the SDNTechForum community! 💖🤖💖
Before you go, don't forget to leave some claps 👏👏👏 (≥50 would be amazing 😉) and follow me ️🙏.
For further reading, explore my in-depth analysis on Medium and YouTube.