I'm 17. I'm from Karachi. I study Electronics, not Computer Science. And somehow I ended up on EC-Council's Hall of Fame — the organization that certifies millions of cybersecurity professionals worldwide.
This is how it actually happened.
I want to be honest about something upfront: I wasn't on some serious mission when this started. I'd already done responsible disclosures on PriceOye and Waqar Electronics. This time I was just bored, curious, and poking around EC-Council's platforms for fun. No grand plan. Just time to kill.
I found two bugs on their store (eclstore.eccouncil.org) — an unhandled 500 error on a checkout endpoint and version numbers being leaked across all their static assets. Wrote it up properly, CWE references, reproduction steps, remediation suggestions, the whole thing. Submitted March 30.
April 8th, 5:58 AM — the rejection arrived.
"Based on their assessment… the submission has been classified as informational/invalid under the Bug Bounty Program scope and does not meet the criteria for a qualifying vulnerability."
Fair enough. Low severity findings, I knew that going in. But something about getting rejected made me want to keep looking. Not out of anger — more like a reflex. If I missed something there, what am I missing elsewhere?
So I opened their CodeRed platform instead. Same approach: read what the API is actually returning, follow the chain wherever it goes.
By 2:50 PM the same day I had 9 vulnerabilities documented and submitted. Three of them Critical.
Before I get into what I found — here's my entire toolkit for this session: browser DevTools, Claude, and Gemini. That's it. No Burp Suite. No mitmproxy. No paid platform. No fancy setup. Just F12, two AI assistants to help analyze responses, and pattern recognition.
The company that trains and certifies professional penetration testers worldwide. Found by a 17 year old with a browser console and two chatbots.
The first thing that caught my eye was an API endpoint returning way more data than it should — internal cloud storage paths buried in the response metadata. I followed that path. It led to a publicly accessible, unauthenticated container. Private user profile assets, no authentication required. That's two vulnerabilities chained into one attack path.
Then I found a live third-party API key being transmitted in plaintext URL query parameters. Not in headers, not encrypted — in the URL itself. Sitting in every browser history, every proxy log, every CDN access log simultaneously.
Then a wildcard CORS configuration on authenticated API endpoints. Access-Control-Allow-Origin: * is fine for public static files. On endpoints that return user-specific data after authentication, it means any malicious website can make requests on behalf of your logged-in users and silently read the response. Critical.
And then the same class of issue from my first rejected report — unhandled exceptions leaking raw framework stack traces — but this time on a production platform where it actually mattered.
The difference between my first report and this one wasn't skill. It was surface area. The store was a small WordPress site. CodeRed was a full authenticated platform with a complex API. More surface, more to find.
I submitted the full report at 2:50 PM — formal VDP document, HAR capture, PoC screenshots, CVSS scores. Referenced the previous ticket so they'd have full context.
Their team acknowledged it within 12 minutes.
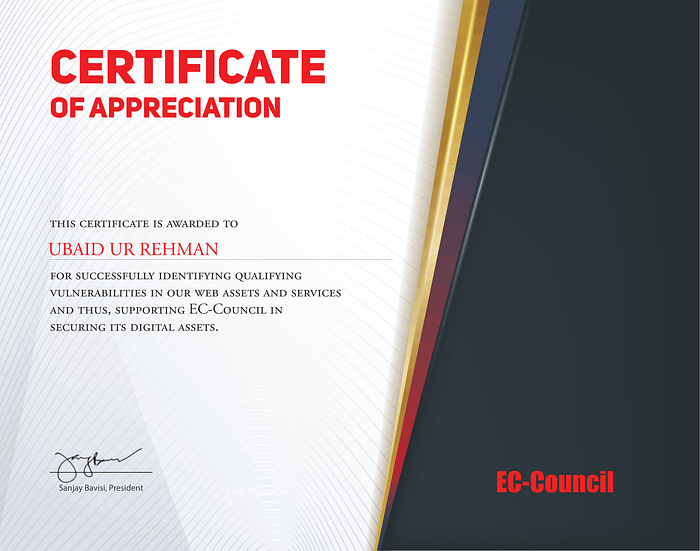
Then came the waiting. Responsible disclosure is mostly waiting. On April 30 they confirmed remediation was underway and asked for my full name for the certificate.
Then on May 1 they sent the certificate email addressed to "Siddharth."
I emailed back to let them know my name is Ubaid.
They apologized, fixed it, and on May 5 the certificate arrived — signed by Sanjay Bavisi, President of EC-Council — along with my name on their public Hall of Fame page.
I'm not writing this to flex. I'm writing this because when I was getting into security research, I couldn't find many stories from people who looked like me or came from where I come from. Most write-ups are from people with CS degrees, bug bounty platforms with real payouts, or labs with proper resources.
I have a laptop, a browser, and internet. That's it.
The vulnerabilities don't care where you're from. Neither do the Hall of Fame pages. If you're a researcher in Pakistan or anywhere else where this field feels out of reach — it isn't. F12 is free. Start there.
Ubaid Ur Rehman — Security Researcher, Karachi, Pakistan GitHub: darkmaster0345 | Portfolio: ubaid-ur-rehmanportfolio.vercel.app