This writeup demonstrates how to exploit HTTP request smuggling to reveal front-end request rewriting. The application uses a front-end and back-end server, and the front-end does not support chunked encoding. Access to /admin is restricted to the IP address 127.0.0.1, and the front-end adds a custom IP header to incoming requests. By smuggling a request to the back-end server, we first uncover the added header, then craft another smuggled request that includes it to access the admin panel and delete a user.
Step 1: Intercept
Intercept the request to the application and send it to Repeater.

Step 2: Creating the headers
Remove all headers except Host, then change the HTTP method from GET to POST.

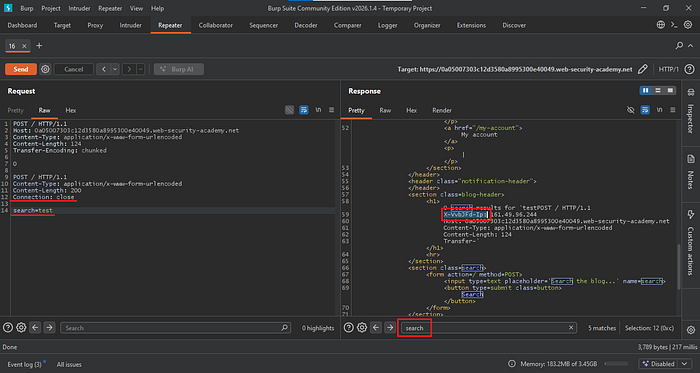
Now add the headers Content-Type, Content-Length, and Transfer-Encoding to the first request. Then add another POST request with the same Content-Type and Content-Length headers, but set the Content-Length to 200. Add a Connection header, and at the end include a search=test parameter.
After sending the request twice, check the response for the search parameter. You should see an additional IP-related header in the response. Copy this header, as it will be used in the next request.
Step 3: Exploitation
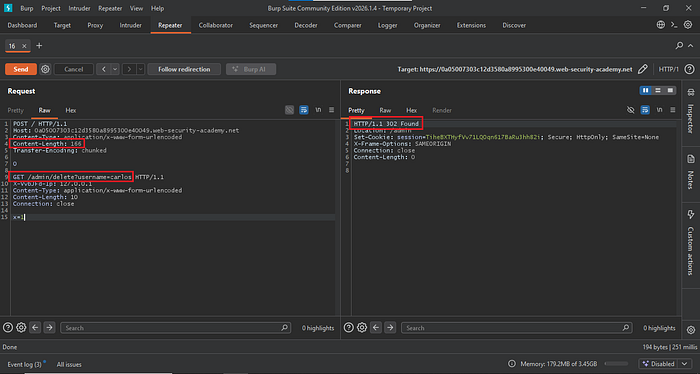
To exploit this, change the Content-Length of the first POST request to 143. Then change the second request from POST to GET and set it to the /admin path. Paste the IP header you copied earlier and set its value to 127.0.0.1. Update the Content-Length to 10, and replace search=test with x=1.
Send the request twice. A 200 OK response indicates that you have successfully accessed the admin panel.

Now delete a user by changing the Content-Length of the POST request to 166. Then update the admin path to /admin/delete?username=carlos to target that user.
Send the request twice. A 302 response indicates that the user has been successfully deleted.
To prevent this attack, ensure that both the front-end and back-end servers handle requests consistently and do not interpret them differently. Configure the system to reject unusual or malformed requests instead of forwarding them. Do not rely solely on front-end checks for sensitive features like the admin panel — enforce access controls on the back-end as well. Keeping servers updated and using secure default settings helps prevent attackers from bypassing restrictions through request smuggling.
