Welcome to this beginner friendly walkthrough of a Ƌ Minute Hack' room on TryHackMe. This one is entitled W1seGuy and from the description, looks to be related to cryptography. Let's get to it!
The first task is to download the task files. In this case, it is a .py file that contains the source code of an encryption function. I used Visual Studio Code to analyze the source code. No answer is required for this task so I just click on 'Check' to continue on to task 2.
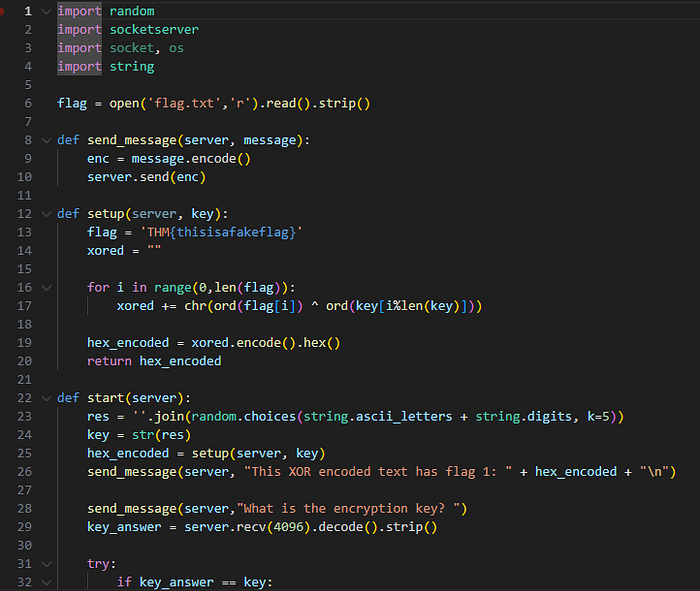
Looking at the source code, I get several important clues. The first thing I noticed was the 'flag'. Obviously 'THM{thisisafakeflag}' is not the correct flag, but it does give us our first clue to the format of this flag which will be crucial shortly. Second, I see 'return = hex_encoded' which tells me that is going to be the output. Directly above, I see how hex_encoded is formed. By first using XOR on the flag, then hexing on the XOR'd value I get hex_encoded. Lastly, I see that 'k=5' telling me the key is 5 characters long. That gives me a ton of information to start with.
Now, I need to set up my virtual environment. I click both 'Start Machine' and 'Start Attackbox' to set up my attacker machine and the vulnerable machine. I give that a few minutes to boot up and while it's doing that, I read task 2. Right away I know there is a listener running on port 1337, and I know there is going to be 2 flags.
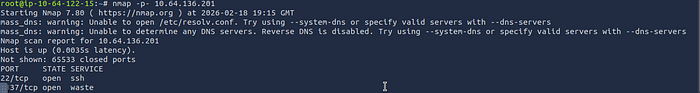
After approximately 5 minutes, I run the nmap command I start every case with, nmap -p- <target ip>. I see there are 2 open ports, 22 for ssh, and 1337 for 'waste'. I did run service detection on the IP as well (-sC -sV), but the results did not give me any useful information. Now that I know there is nothing else running on this machine, I'm going to connect to port 1337 as the task recommended.
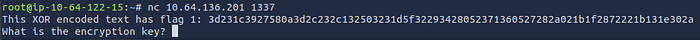
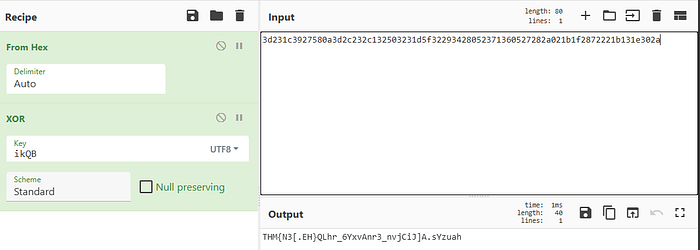
Ah, I've got my first flag! Now, I just need to make it fit the correct format. Going back to my source code review this is exactly what I would expect to see. I'm currently looking at hex_encoded. So, I need to reverse engineer this text and to do that I know that XOR and hex are important. The first thing I did was head over to CyberChef. I know that the key is 5 characters, and I also already know the first 4 characters: THM{. On CyberChef, I select the XOR function and since I know the key is in hex, I will take the first 4 characters which are represented with 2 characters a piece (so the first 8 characters of our hex string) in my case 3d231c39 as the key. Then, in the input I type 'THM{'. The output (ikQB), is the first 4 characters of my key.

Now I have to get the 5th and final character of the key. This is relatively easy, just some manual enumeration once I am set up. I now add 'From Hex' before the 'XOR' function in CyberChef, and change the key type to UTF8. I did this so I don't have to type in hex and to make it quicker. Next I put the first 4 digits 'ikQB' into the key box of the XOR function and copy the FULL hex_encoded text I got from my netcat connection.
You can see the output at the bottom is close to an actual flag. Having done hundreds of these rooms, I know TryHackMe uses a mix of numbers, capital letters, lower case letters, and characters to spell out the flag. From here, I am literally going through the alphabet lower case first then upper case next until I see something that resembles a flag.
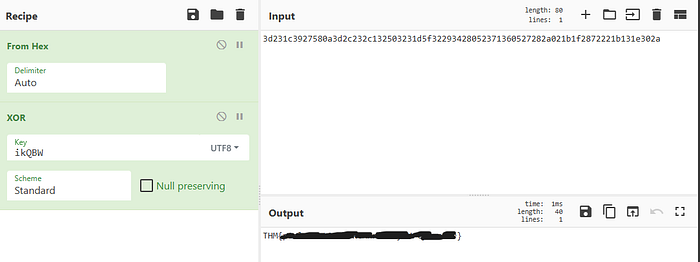
When I get to 'W' the curly brackets close, and it gives me a phrase 'plain text attack can really hurt your xor'. Woohoo! Flag 1 obtained, but more importantly, the full key has been obtained. Now I head back to my terminal and enter my encryption key to get the second flag.

Woohoo! Flag 2 is obtained and another one bites the dust.

Final thoughts: W1seGuy was a focused cryptography challenge that demonstrated how weak XOR-based "encryption" collapses when key length and plaintext patterns are predictable. By analyzing the provided Python source code, identifying the 5-byte key, and leveraging the known flag format (THM{}), the encoded hex/XOR output could be systematically reversed using a known plaintext attack. The room reinforced that encoding layers like hex offer no real protection, XOR is inherently reversible, and poor key management or deterministic plaintext structures create exploitable weaknesses. Overall, it was a strong exercise in cryptanalysis, source code review, and practical decryption workflow rather than traditional service exploitation.
