Day 22 of breaking web applications on purpose.
Yesterday, I discovered something interesting!
A simple Ping tool on a website wasn't just checking connectivity.
It was passing my input directly to the server's command line.
Which meant something dangerous.
If the server runs one command I give it What happens if I give it two?
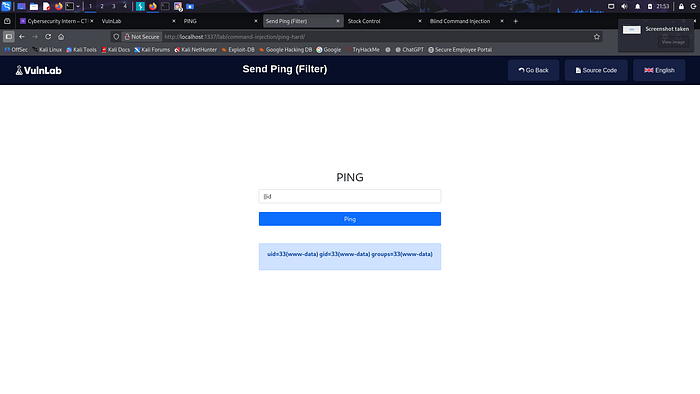
🎯 The Setup
The page had the same simple feature.
Enter an IP address. Click Ping. Get results.
Behind the scenes, the server probably runs something like:
ping <user_input>
But operating systems don't just run one command at a time.
They understand separators.
For example:
;
Which tells the system:
"Run the first command… then run the next one."
So I tried something slightly different.
🧠 The Experiment
Instead of entering just an IP address, I typed:
127.0.0.1;whoami
This tells the server:
Ping localhost.
Then run another command:
whoami
Which reveals the current system user executing commands.
I clicked Ping.
And waited.
💣 The Result
The response came back.
Ping results appeared.
But underneath them…
Another line showed up.
The output of whoami.
The server had executed both commands.
Which meant something huge.
The input field wasn't just taking data.
It was acting like a remote command line.
⚡ Why This Works
The application likely ran something similar to:
system("ping " . $ip);
When the user input includes a command separator like ;, the system interprets it as:
Run the ping command.
Then run whatever comes next.
Which means the attacker controls what the server executes.
🧠 Think About This
Imagine giving someone a walkie-talkie to your computer and saying:
"Tell it to check the network."
But instead they say:
"Check the network… and also tell me who you are."
And the computer just obeys.
That's the danger of command injection.
🔥 Why This Is Serious
If attackers can run system commands, they could:
• Read server files • Discover system configuration • Download malicious tools • Explore the internal network • Eventually take full control of the server
All from a single input field.
🛡️ The Fix
Never execute system commands using raw user input.
Instead:
• Validate input strictly (IP-only formats) • Avoid direct system command execution • Use secure APIs instead of shell commands • Escape shell arguments safely • Run services with minimal privileges
Security rule:
If the server treats input like a command, attackers treat the server like a terminal.
🎯 Day 22 Takeaway
Yesterday the server answered one question.
Today it answered two.
Which proved something important.
The input field wasn't just sending data.
It was giving me instructions over the system itself.
And once an attacker can do that…
The web app is no longer just a website.
It's a doorway into the server.
LESS GOOO 🔥
Sometimes a ping tool isn't a network tool… it's a command line in disguise.